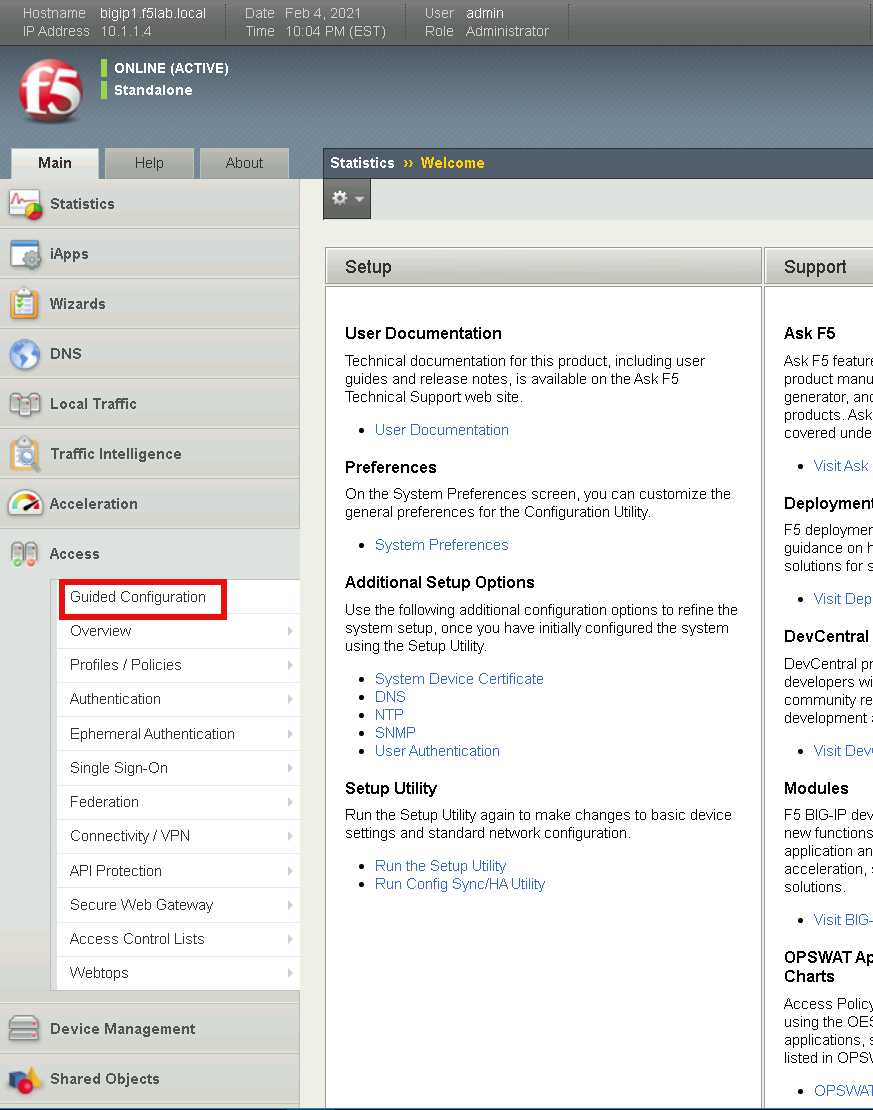
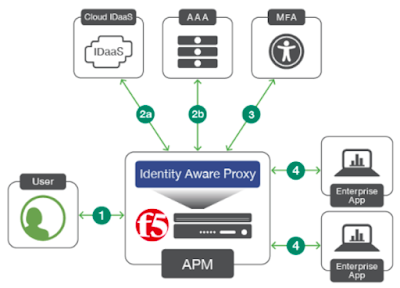
F5 BIG IP APM Identity aware proxy IAP
F5 apm posture hot sale assessment
Share.
Visit »
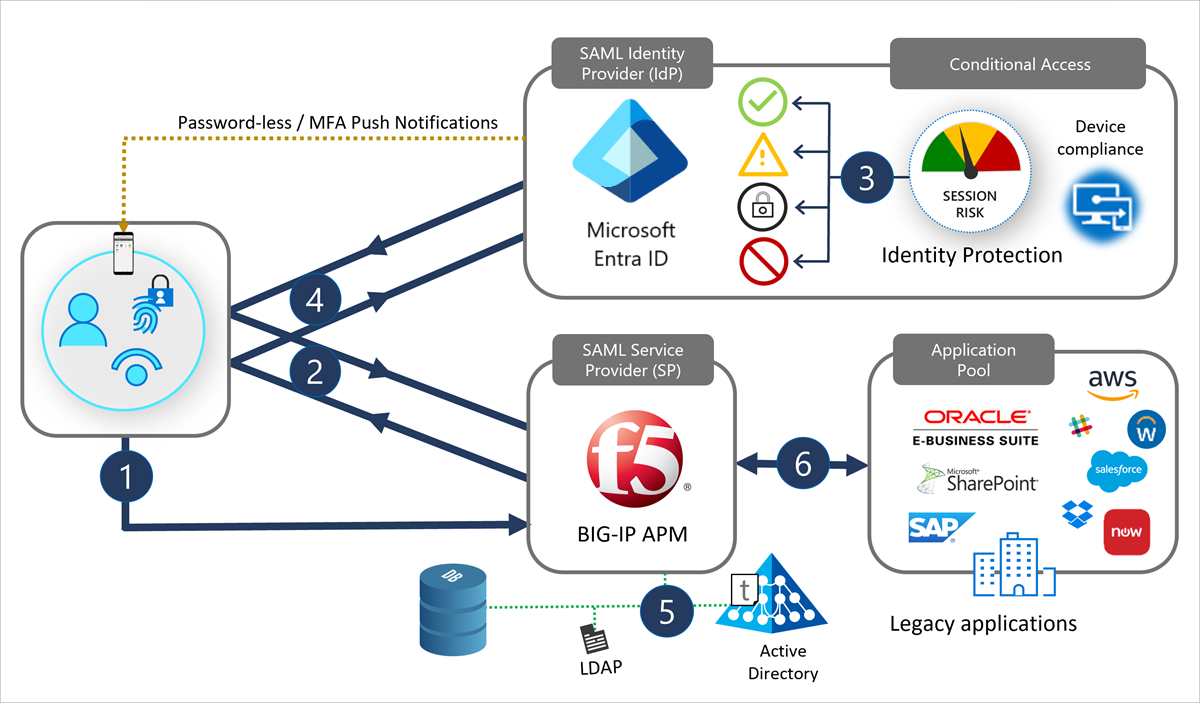
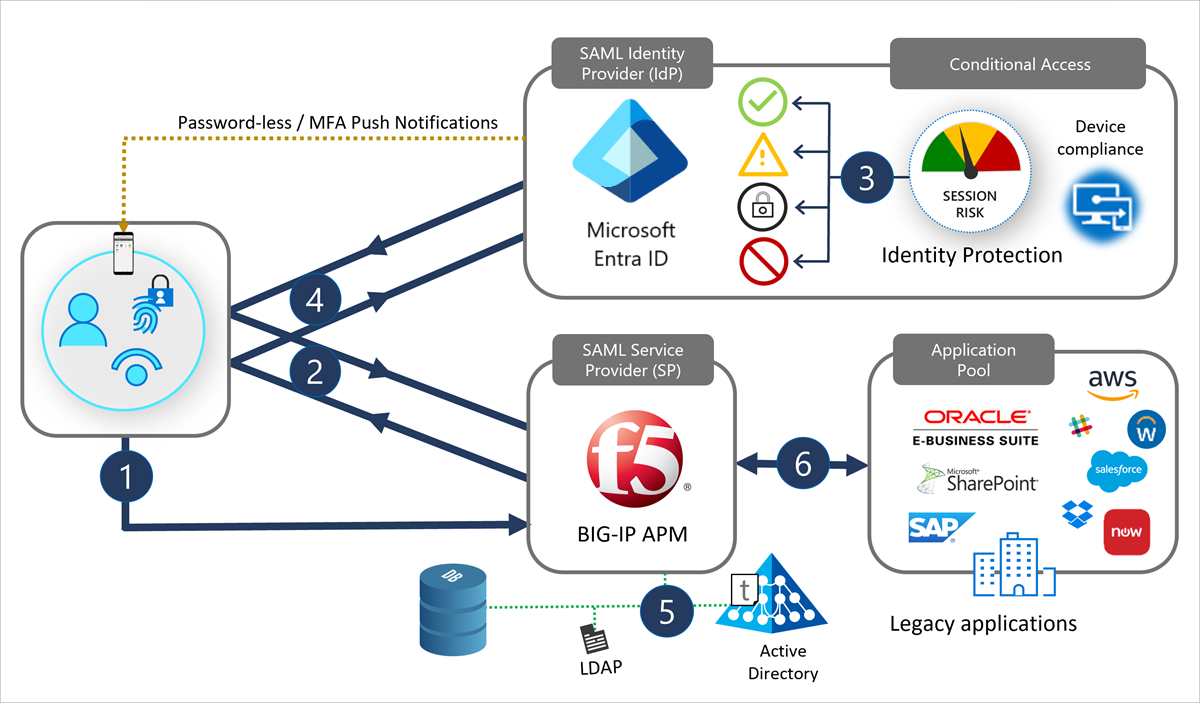
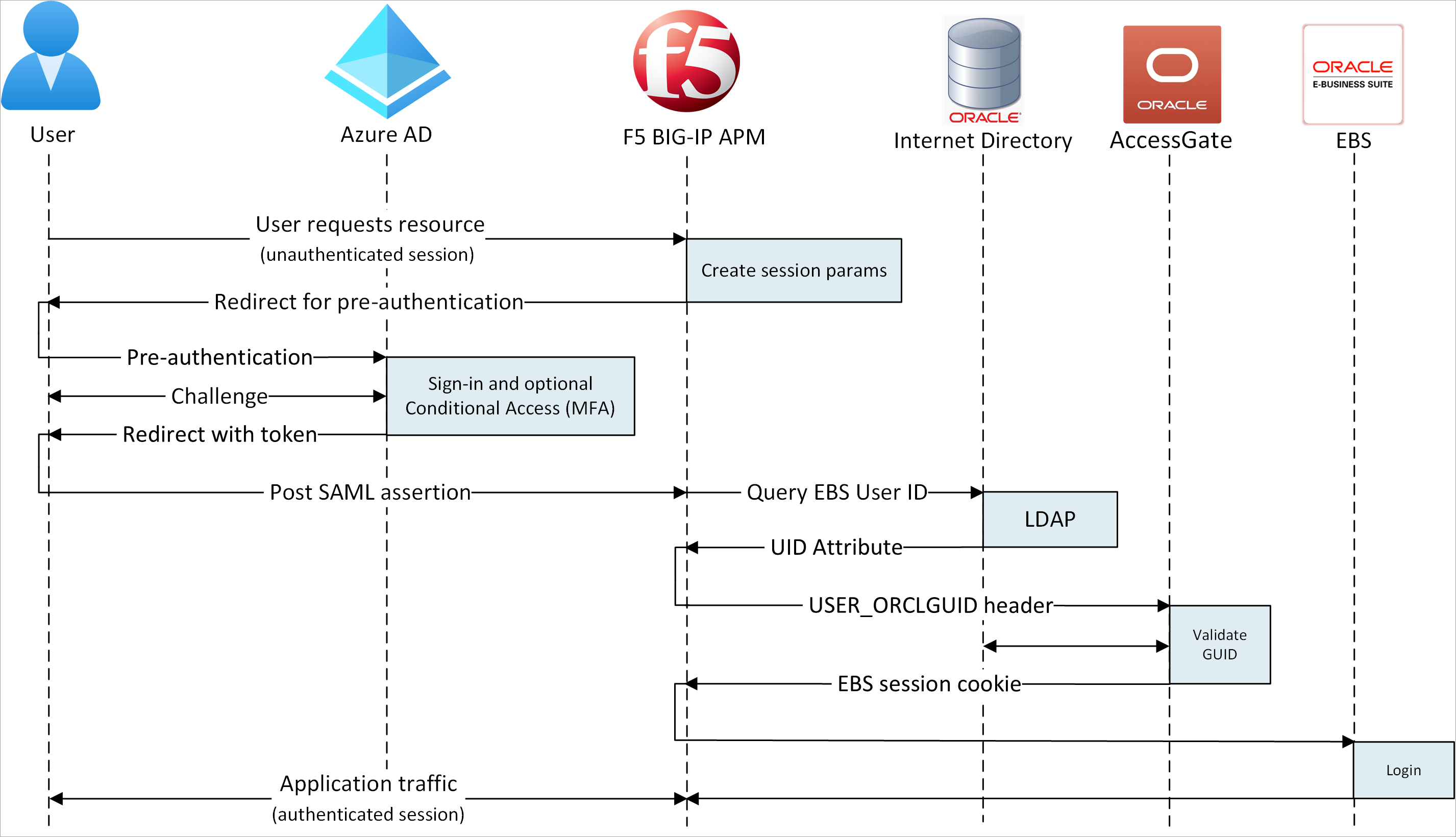
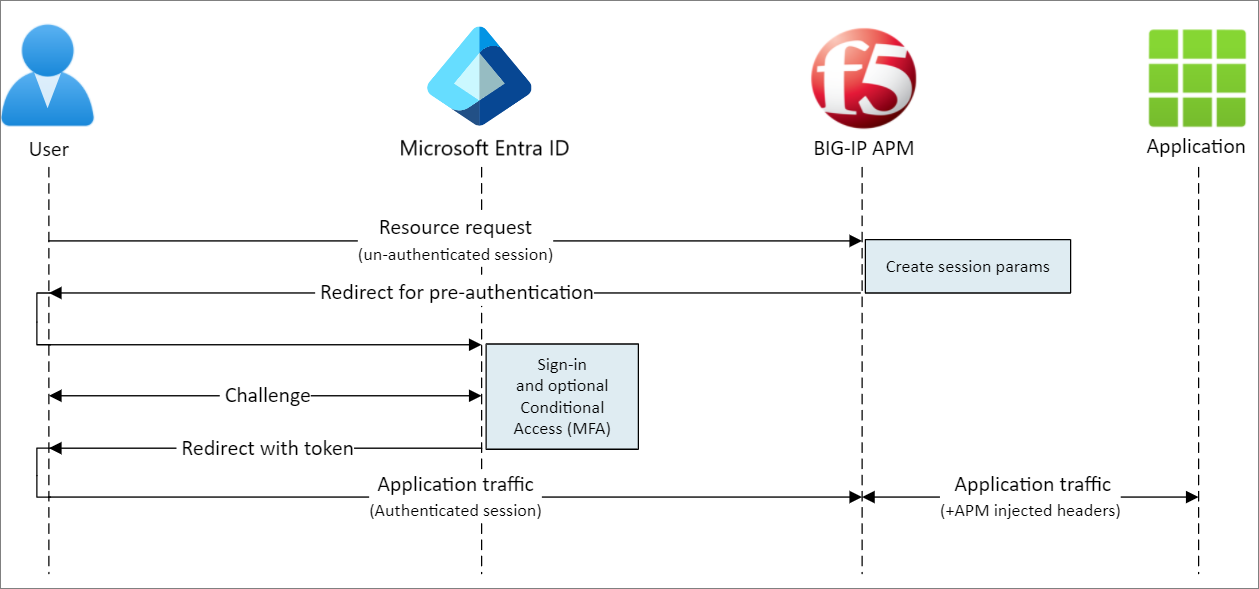
Secure hybrid access with F5 Microsoft Entra ID Microsoft Learn 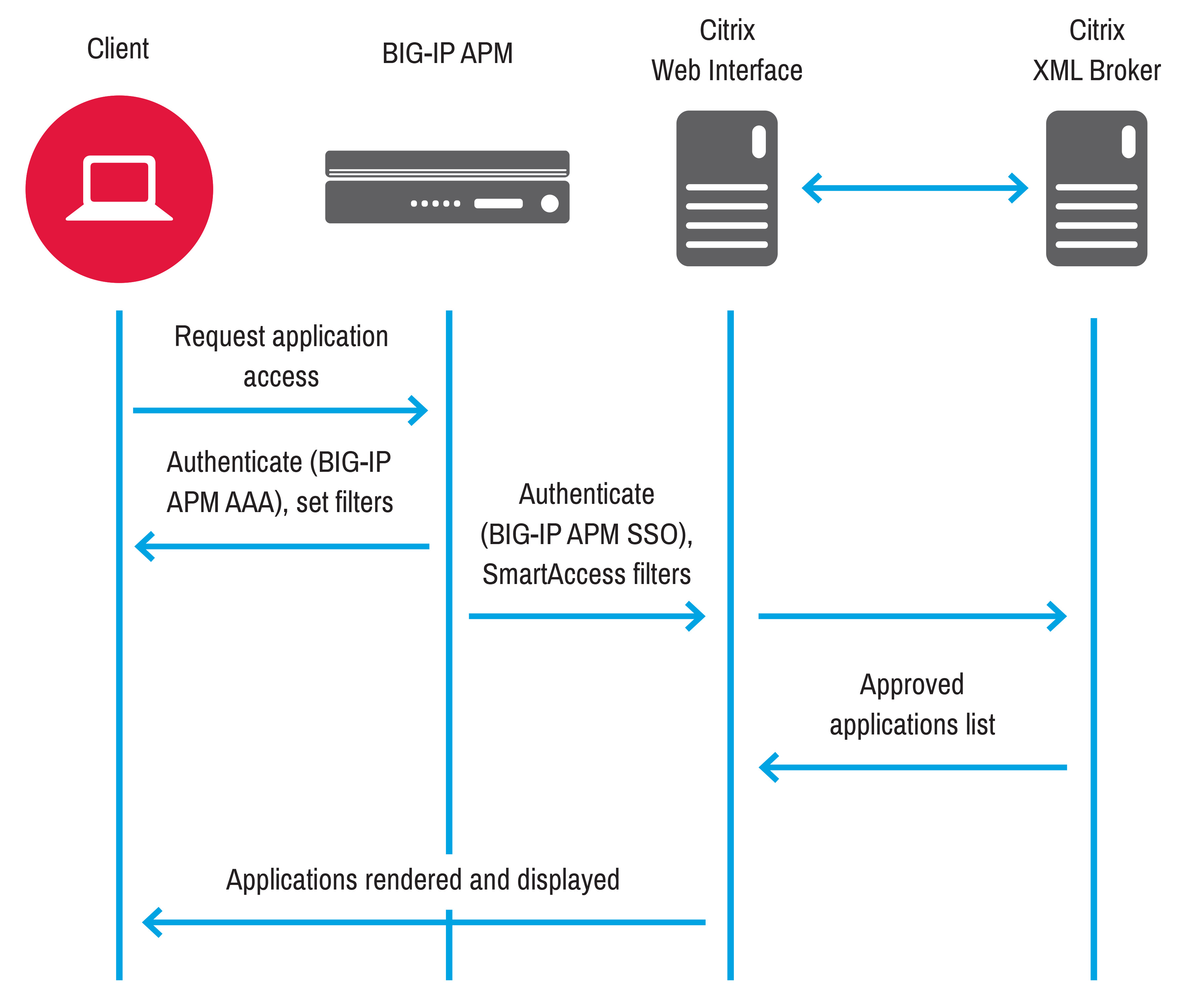
Use cases BIG IP APM operations guide 
F5 Networks TMOS Administration Study Guide by F5 Books Issuu 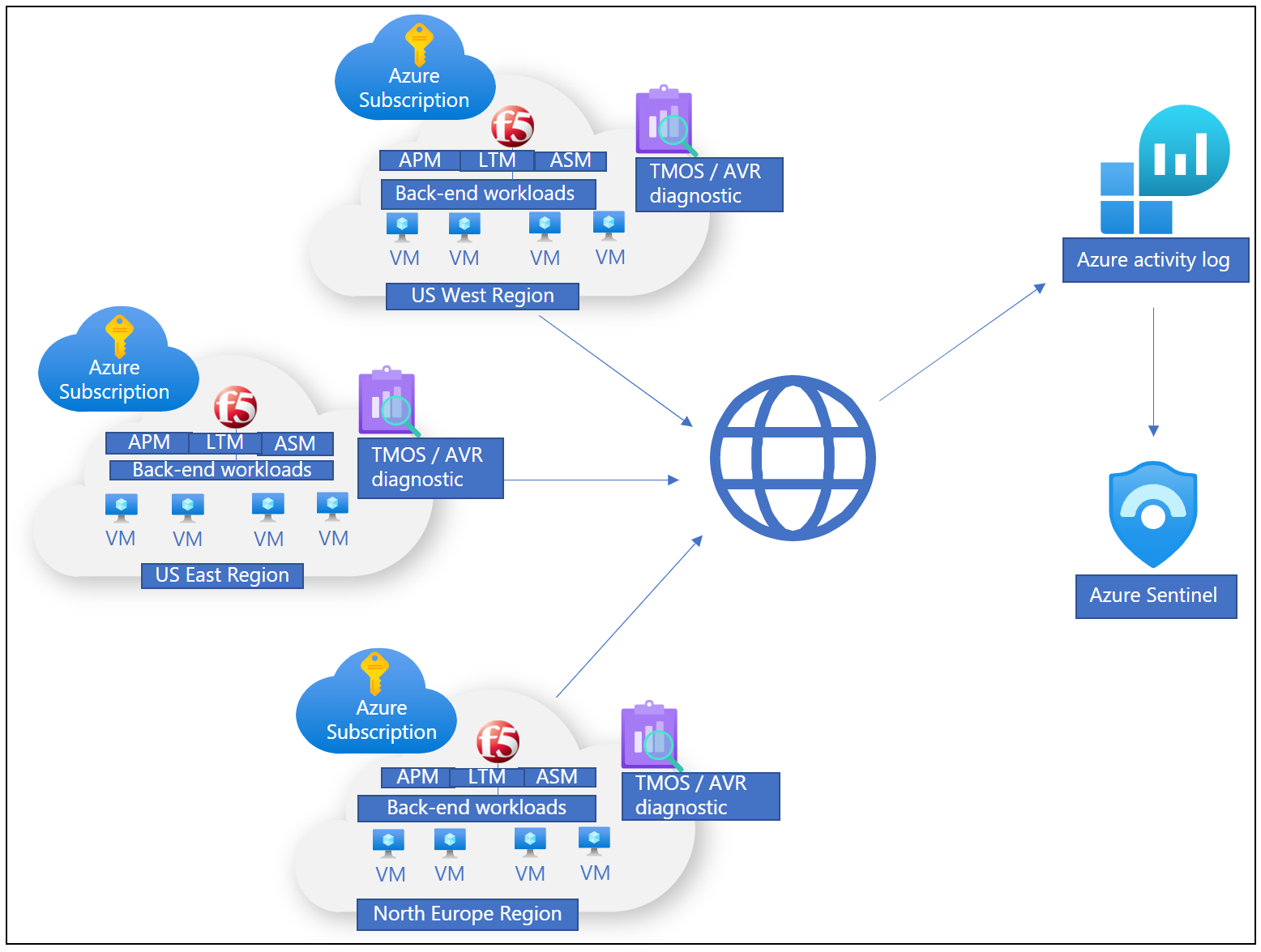
Secure hybrid access with F5 Microsoft Entra ID Microsoft Learn 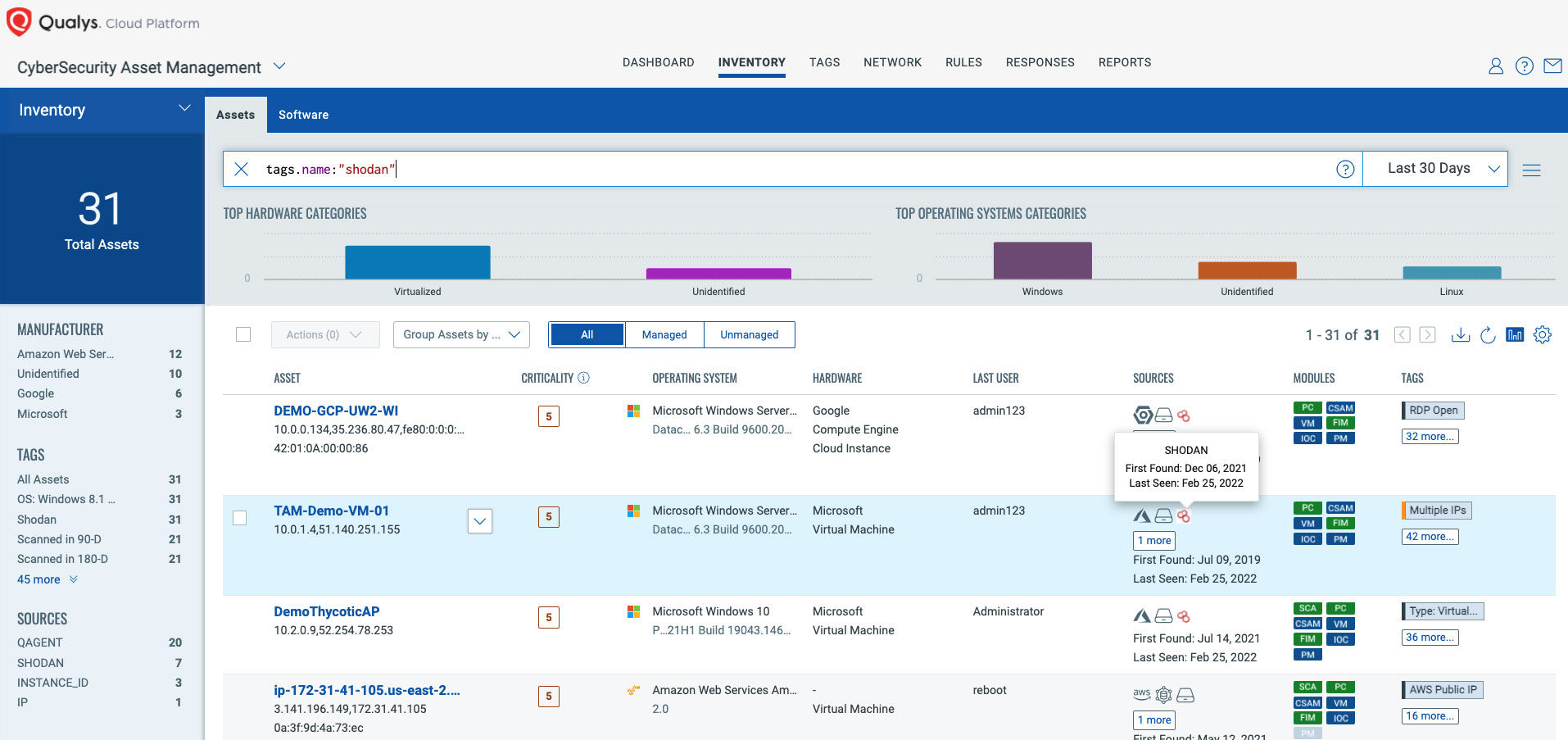
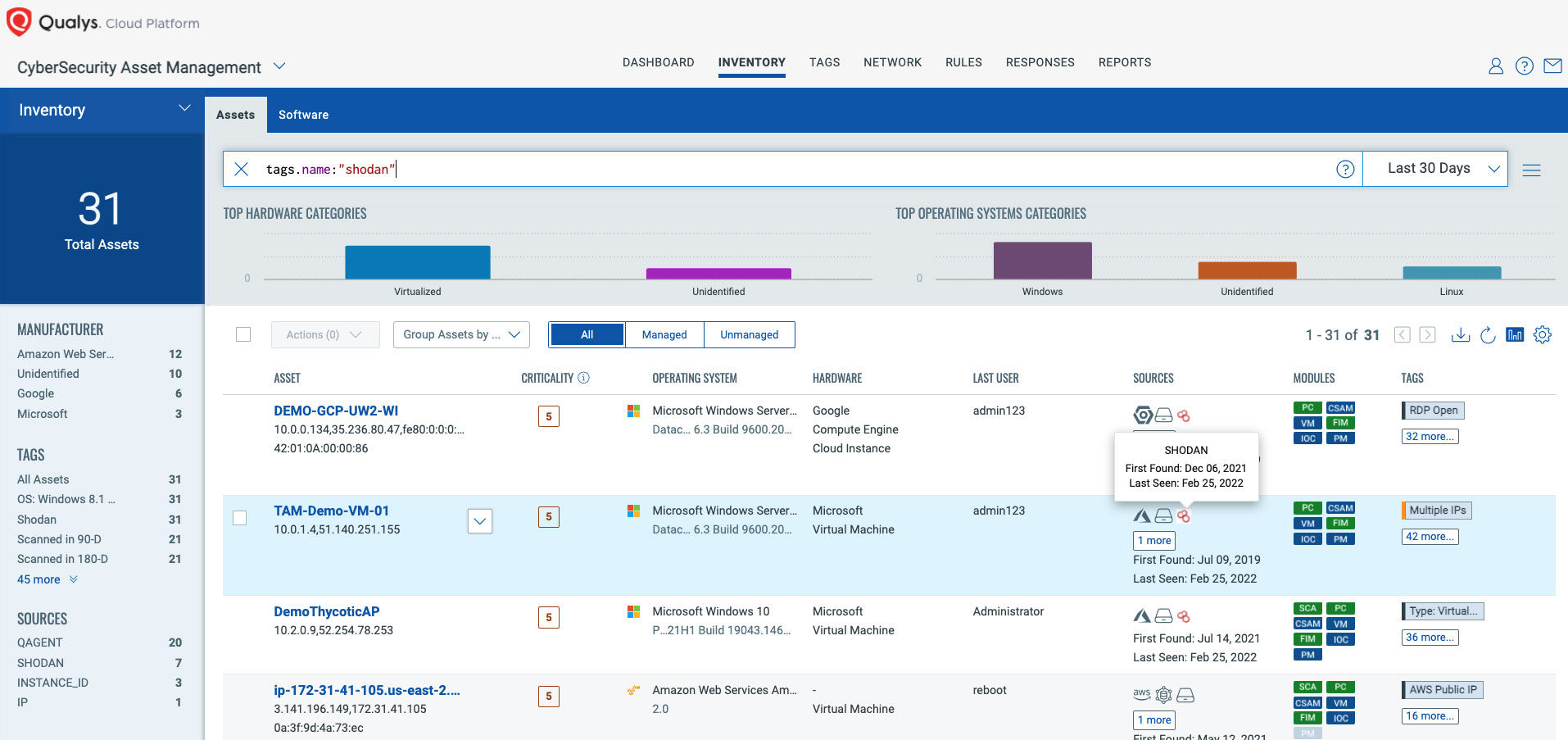
Russia Ukraine Crisis How to Strengthen Your Security Posture to 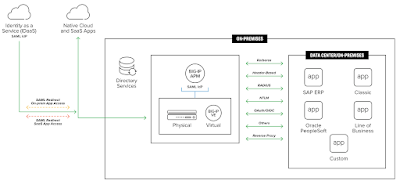
F5 BIG IP APM Identity aware proxy IAP 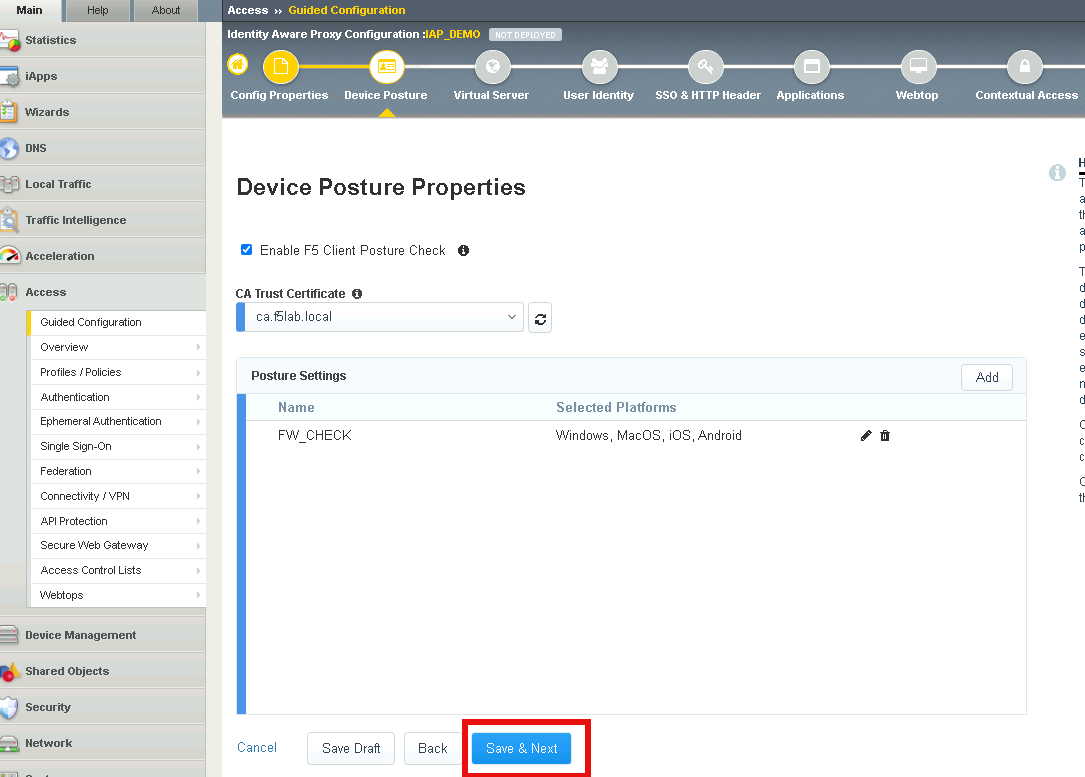
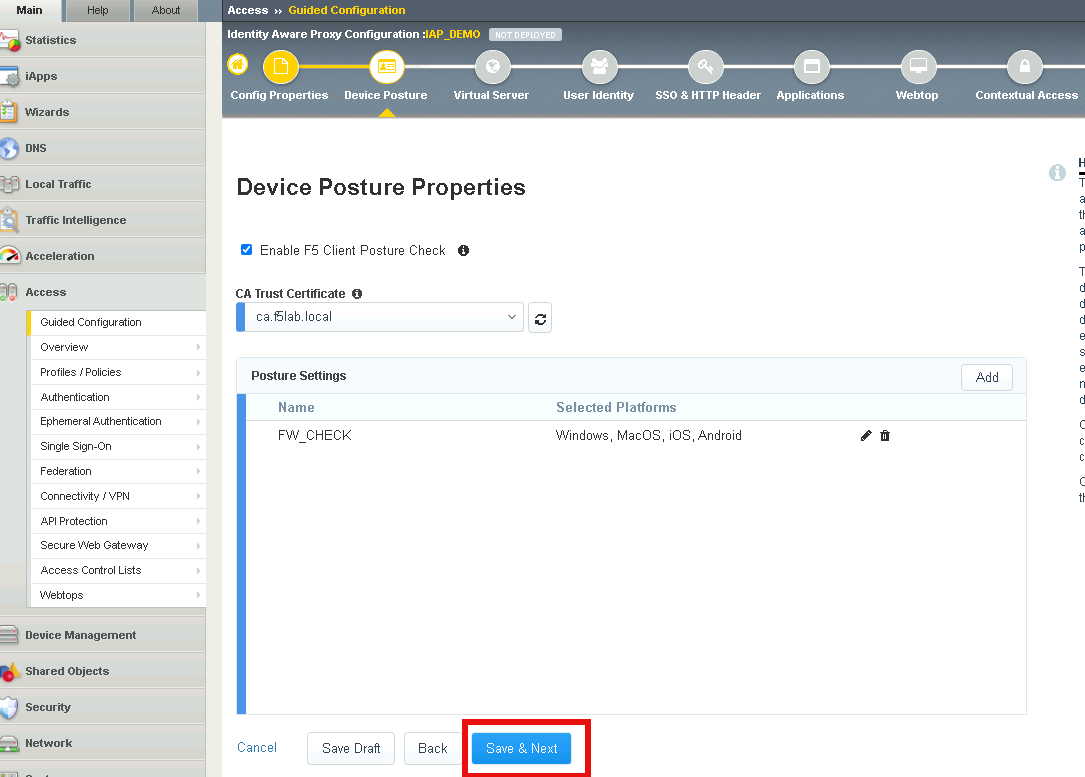
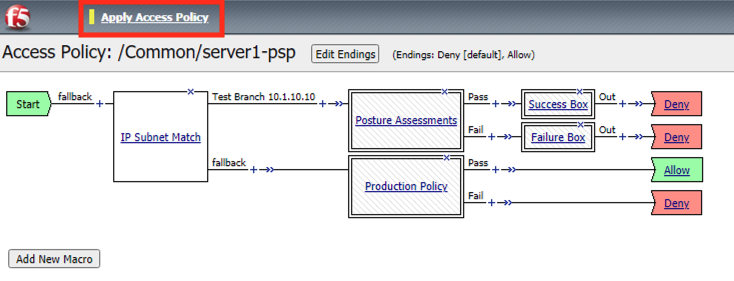
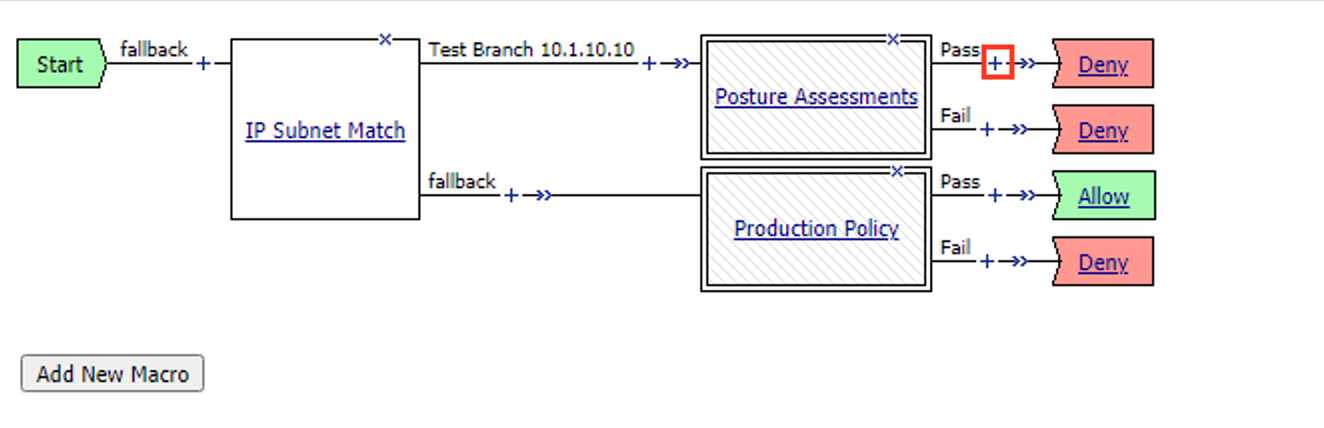
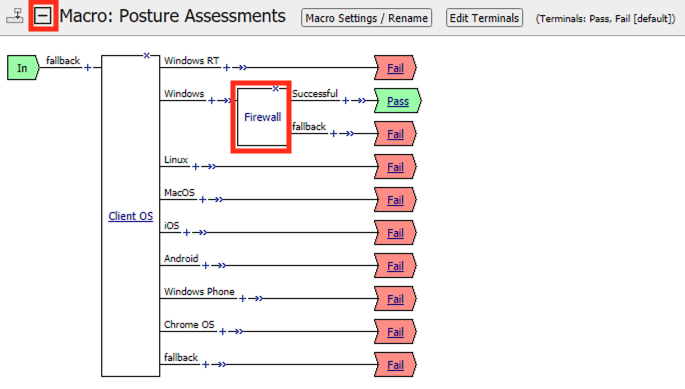
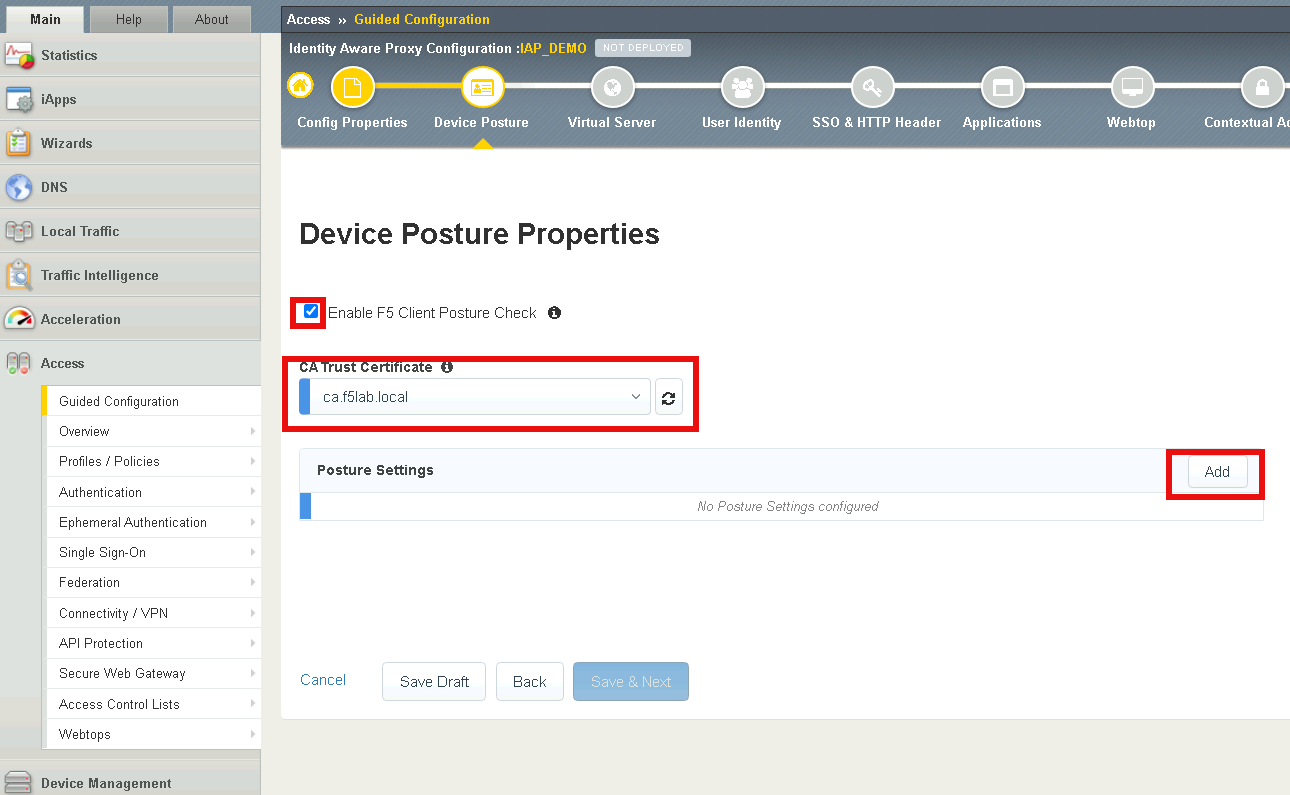
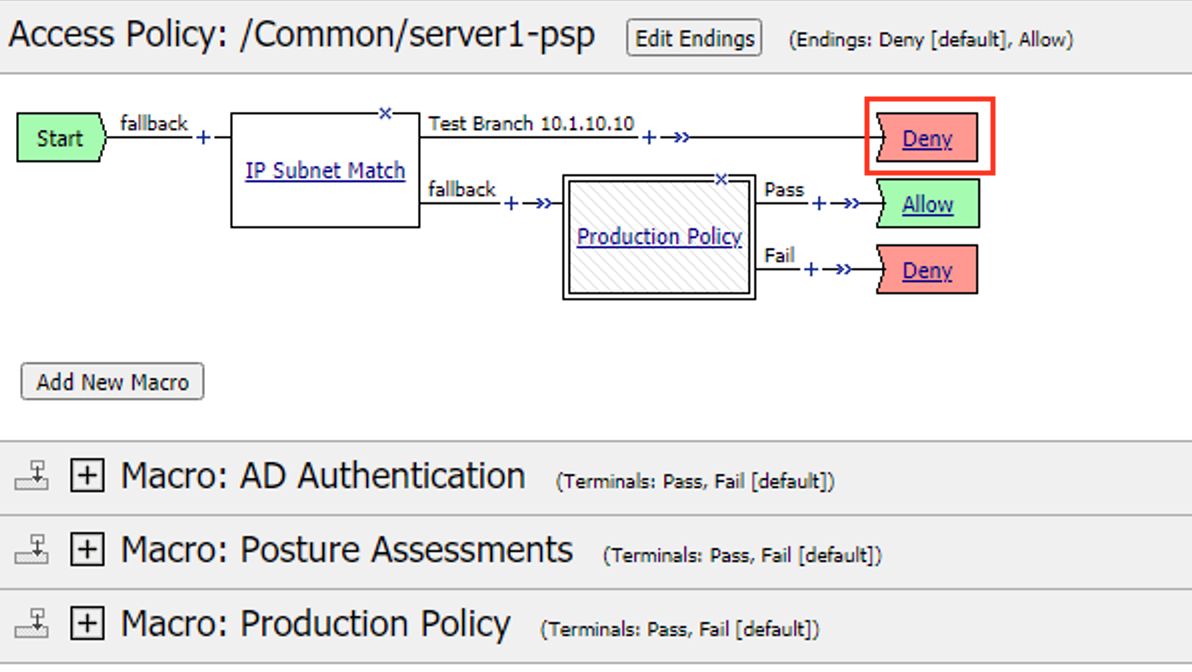
Lab 1 Configure Identity Aware Proxy 16.0 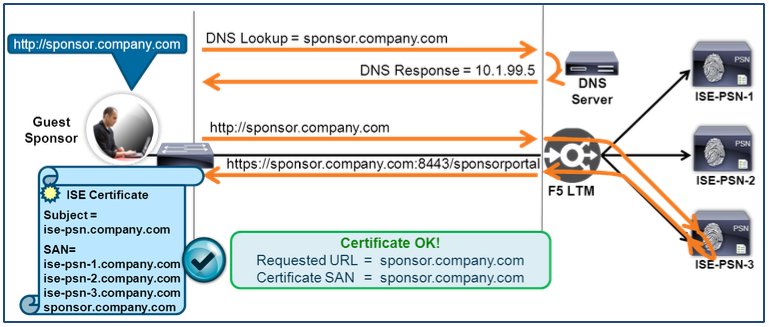
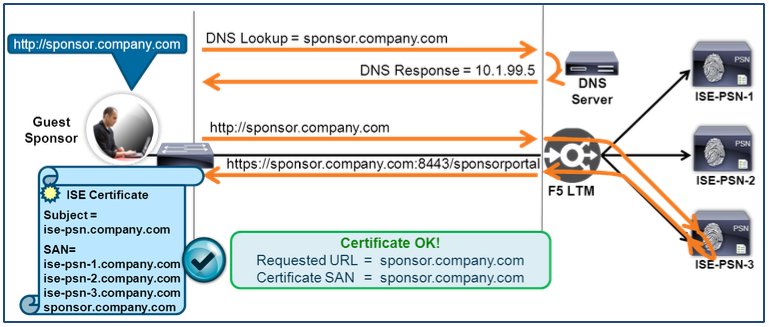
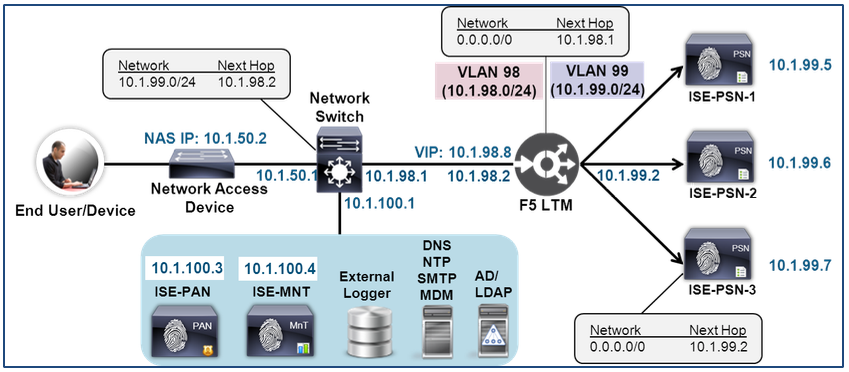
How To Cisco F5 Deployment Guide ISE Load Balancing Using BIG 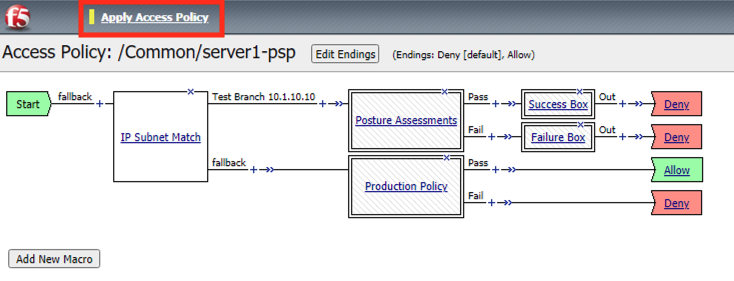
Lab 1 The Message Box 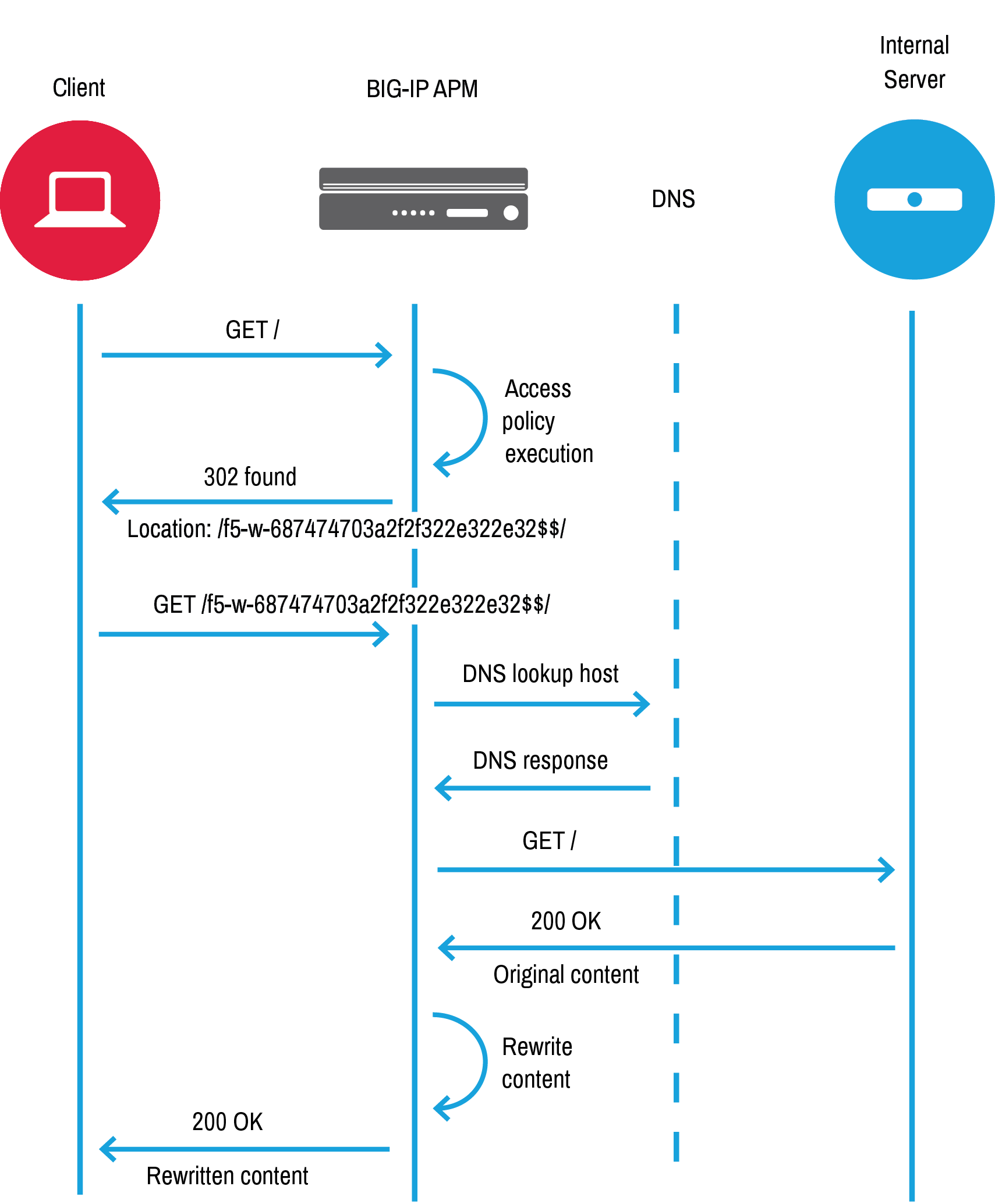
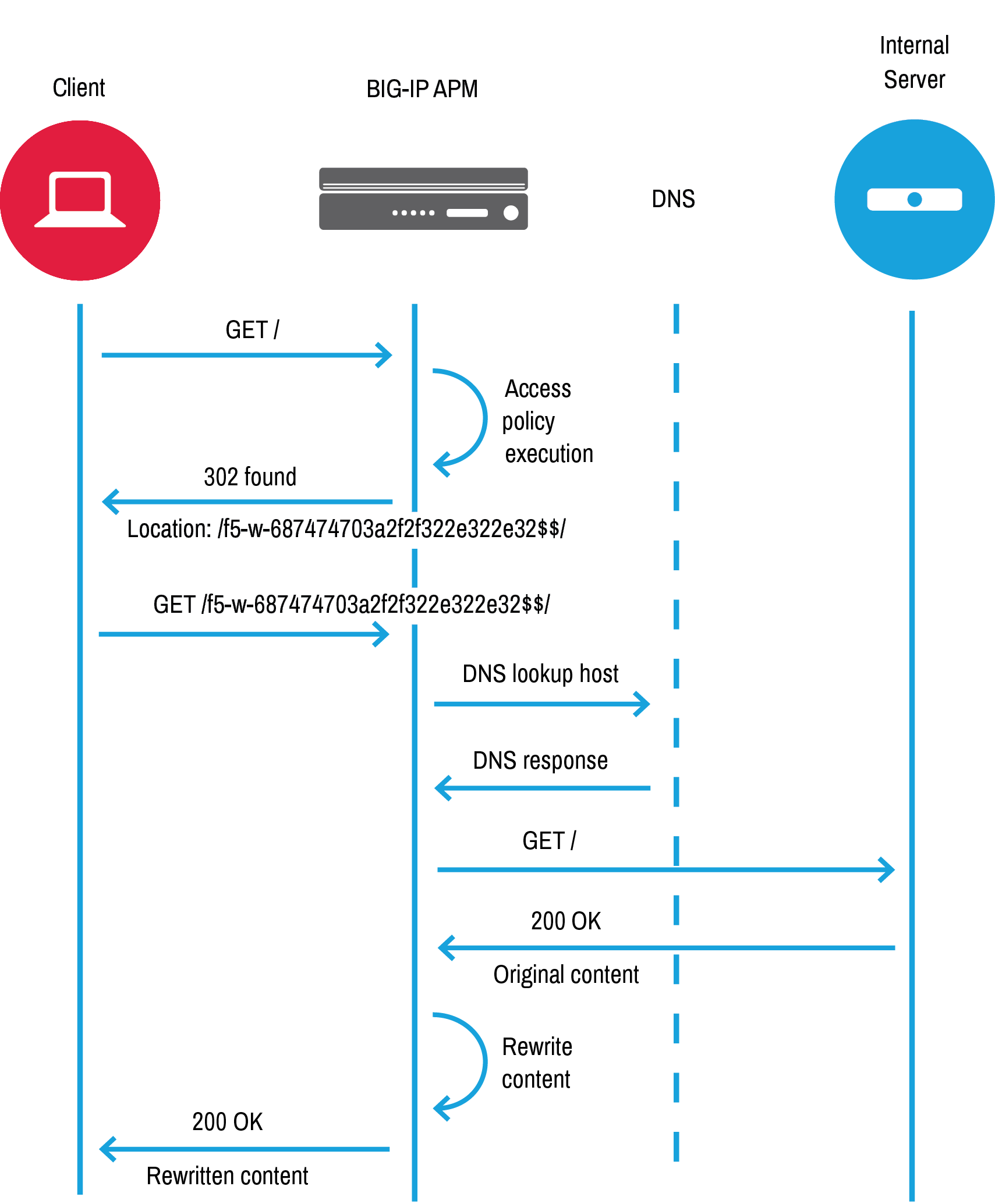
Use cases BIG IP APM operations guide 
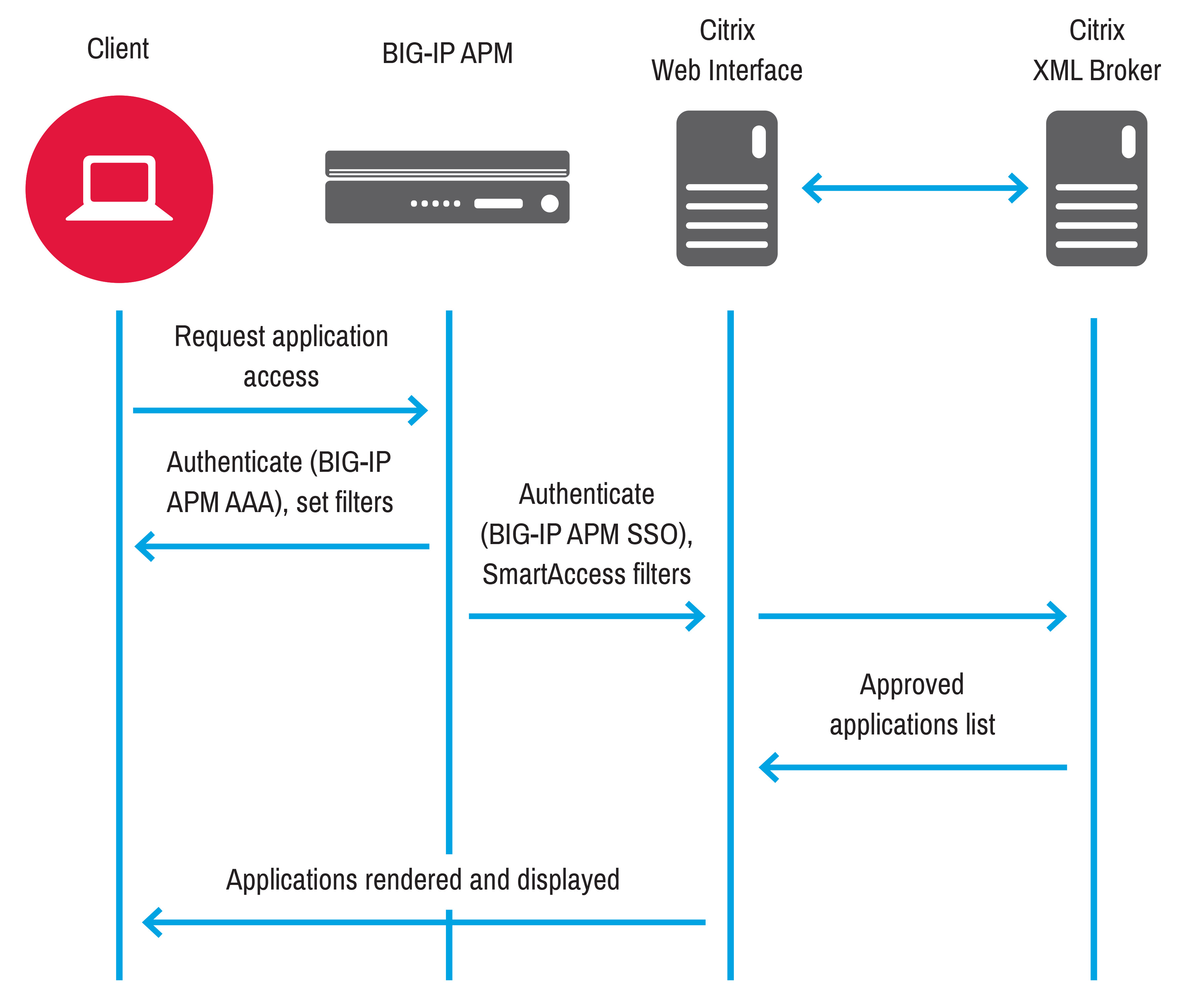
Migrating from Citrix NetScaler to F5 BIG IP History Migration 
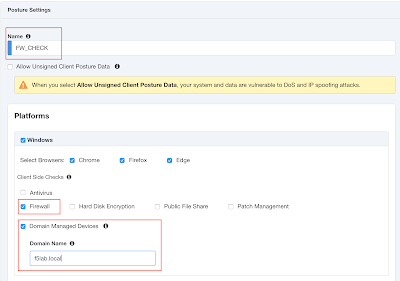
Sample Assessments Diagrams Remediations Wingspan IT 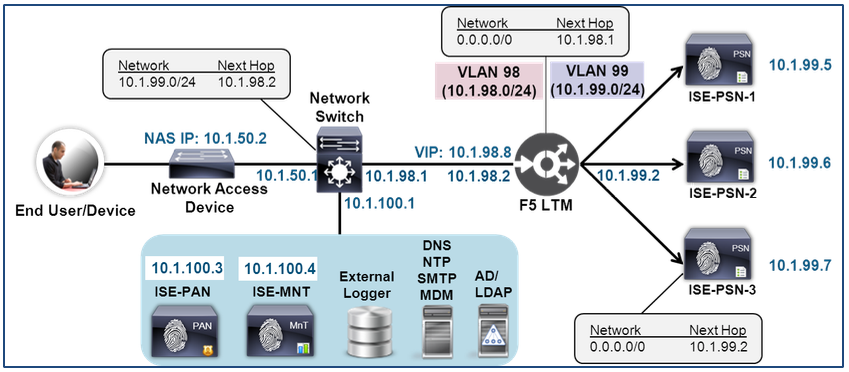
How To Cisco F5 Deployment Guide ISE Load Balancing Using BIG 
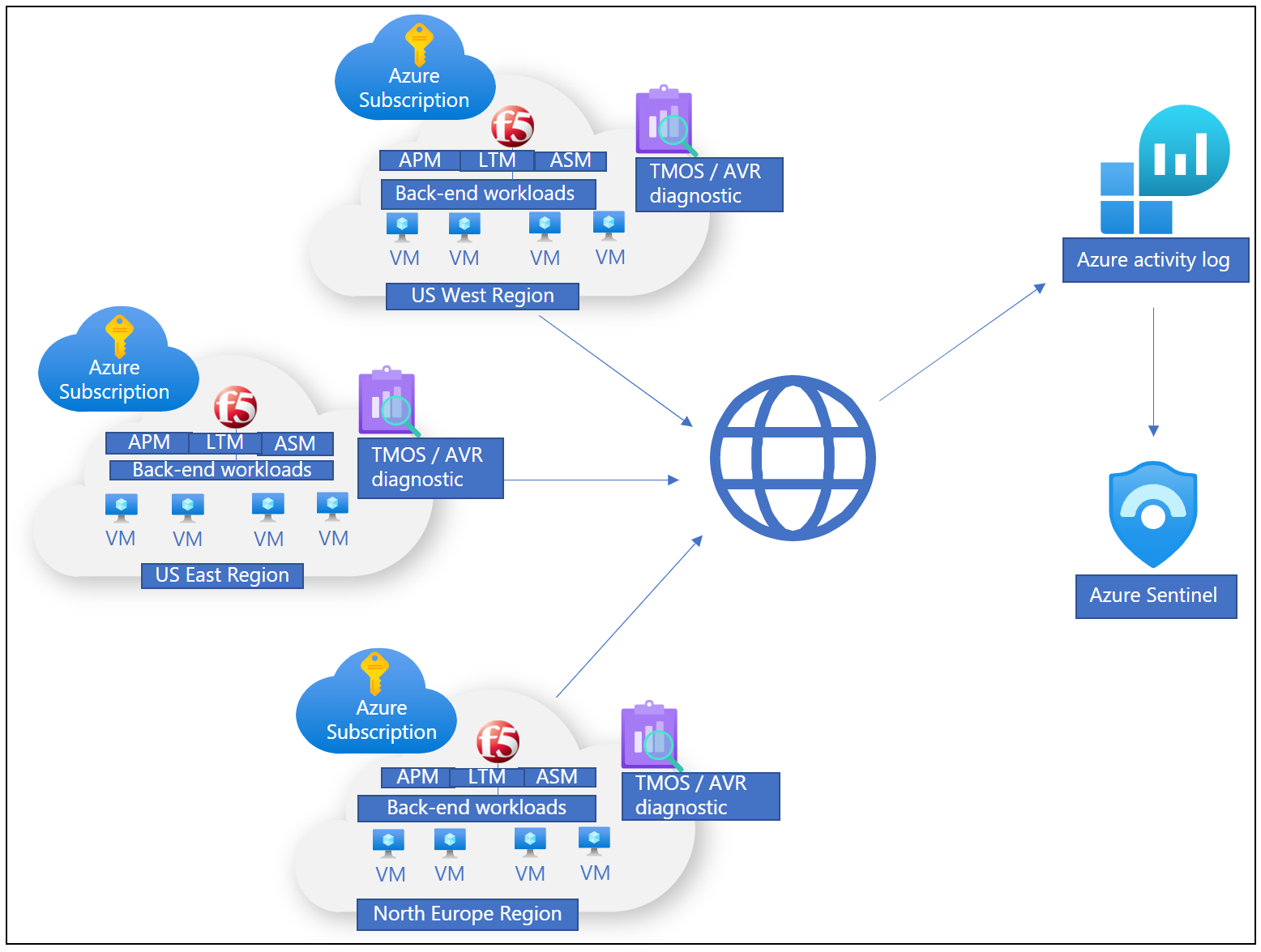
Improving your Defense Posture on Azure with F5 and HashiCorp 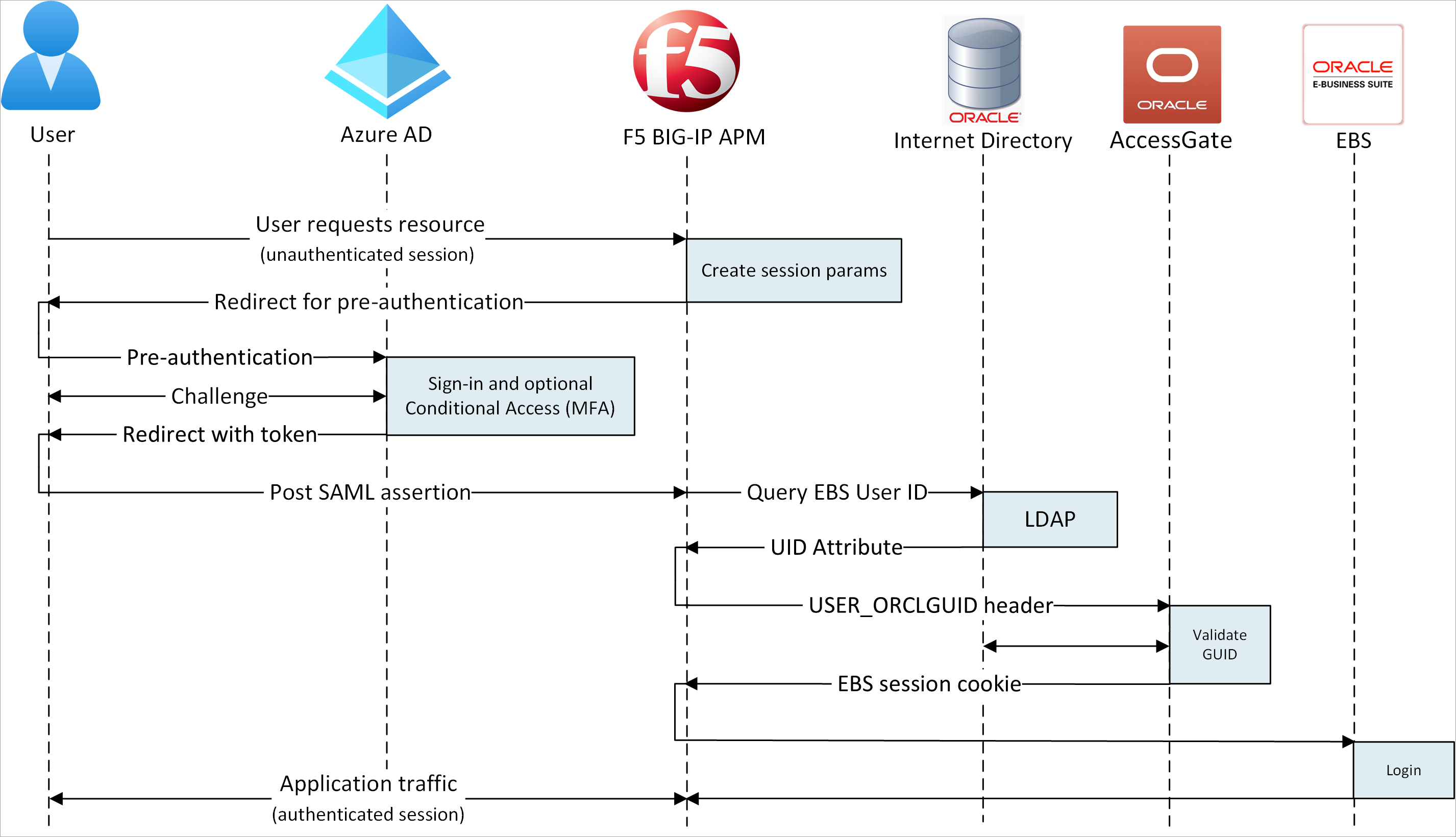
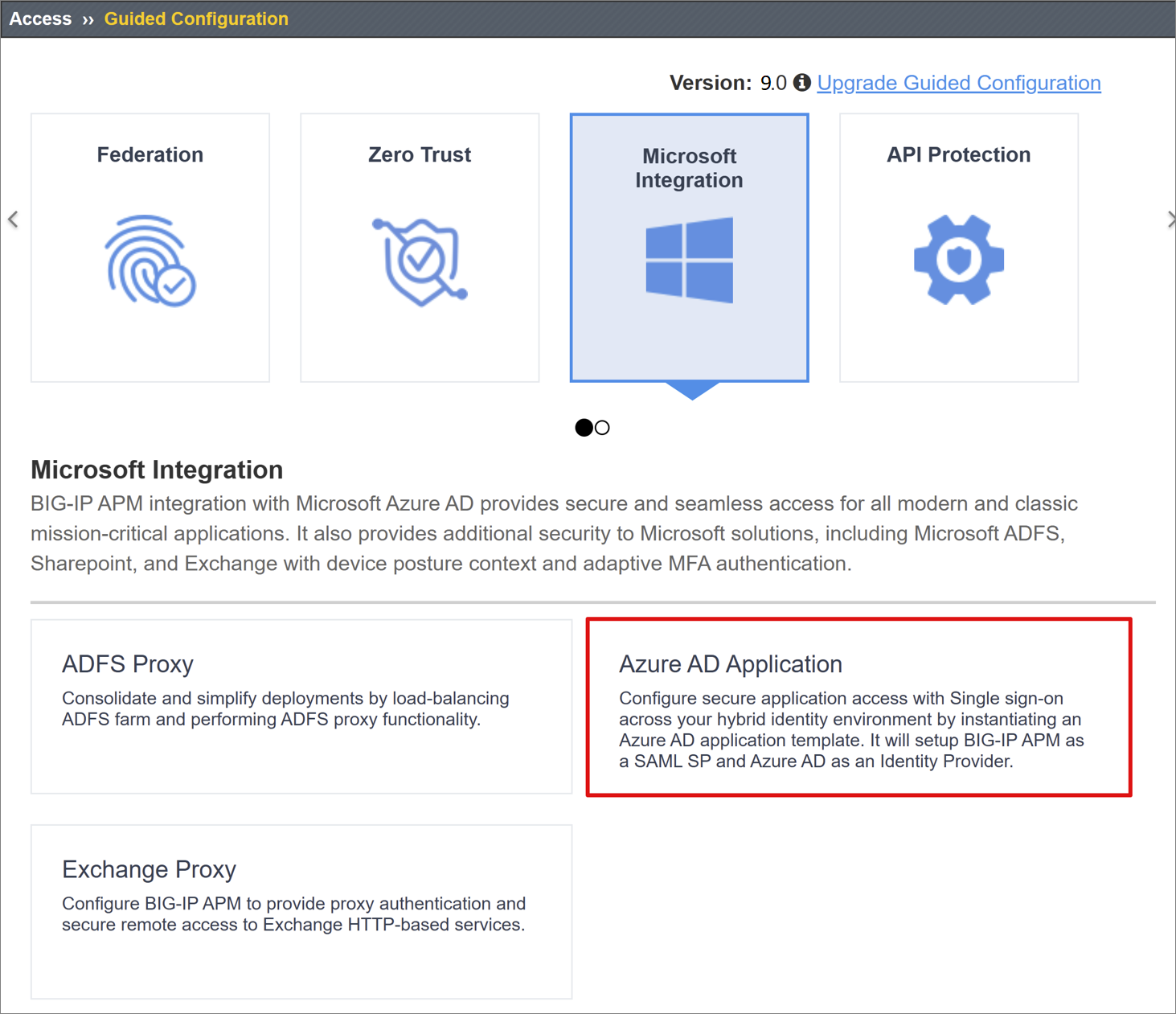
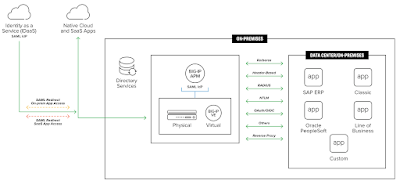
Configure F5 BIG IP Easy Button for SSO to SAP ERP using Microsoft 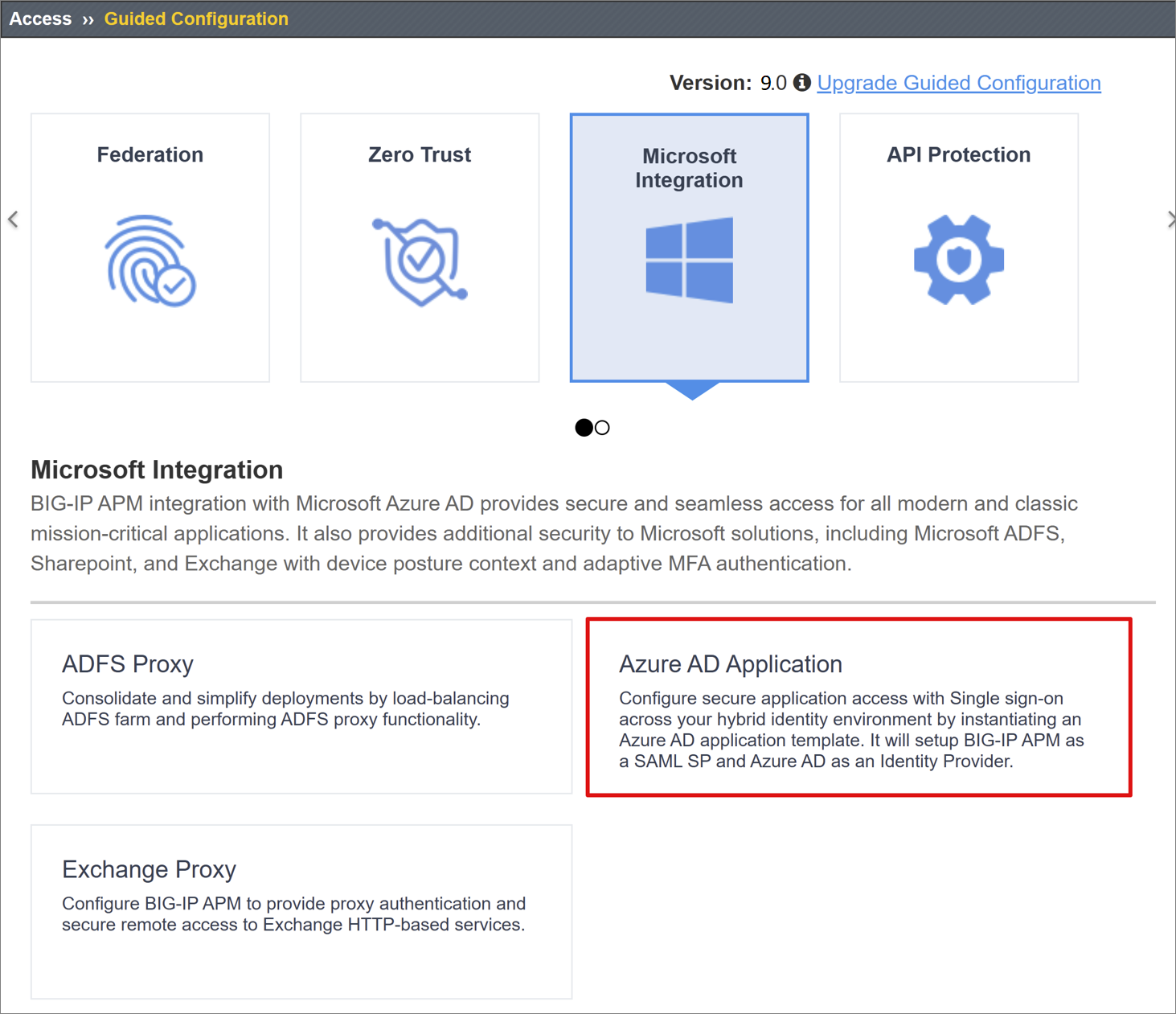
Configure F5 BIG IP Easy Button for SSO to SAP ERP using Microsoft 
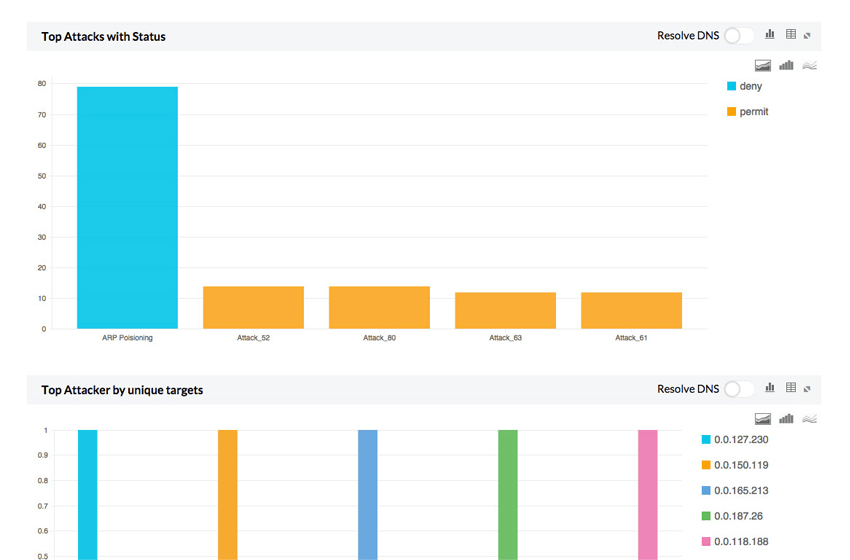
f5 Afm Operations Guide PDF Denial Of Service Attack Port 
F5 BIG IP APM Identity aware proxy IAP 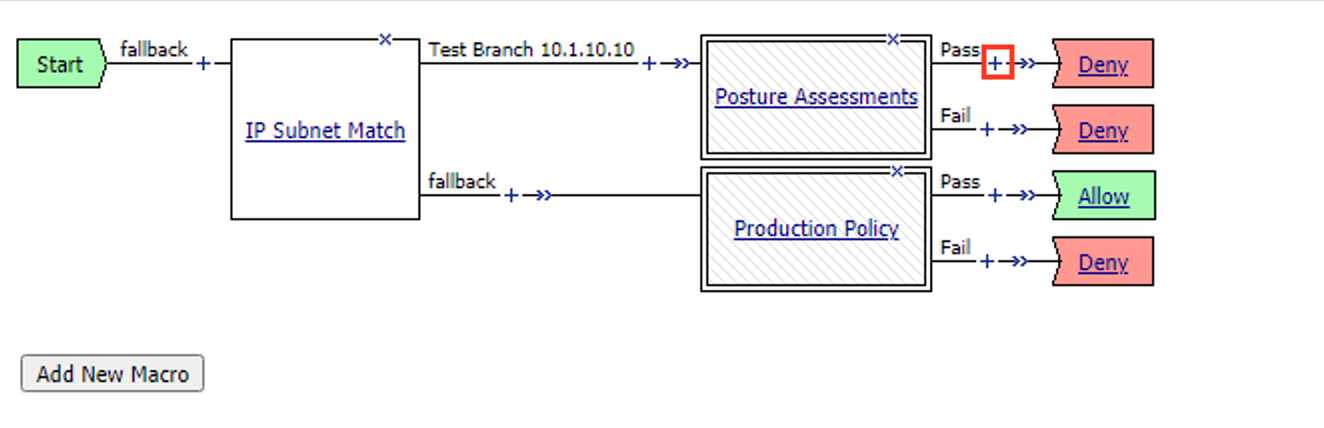
Lab 1 The Message Box 
BIG IP Access Policy Manager 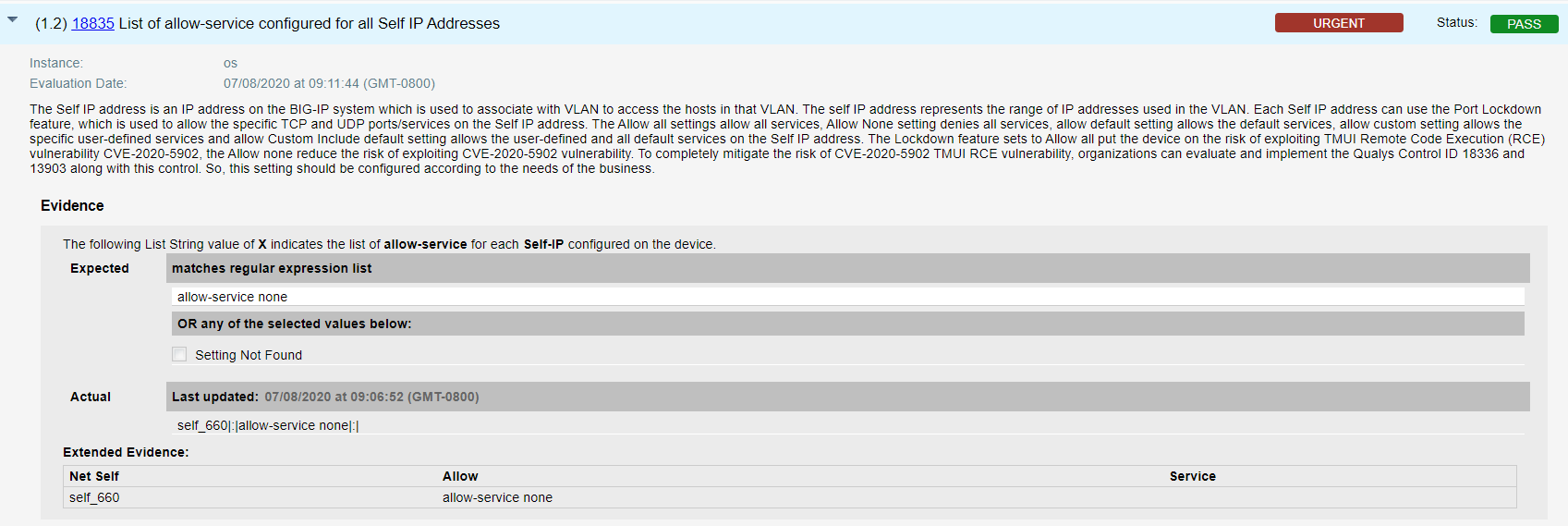
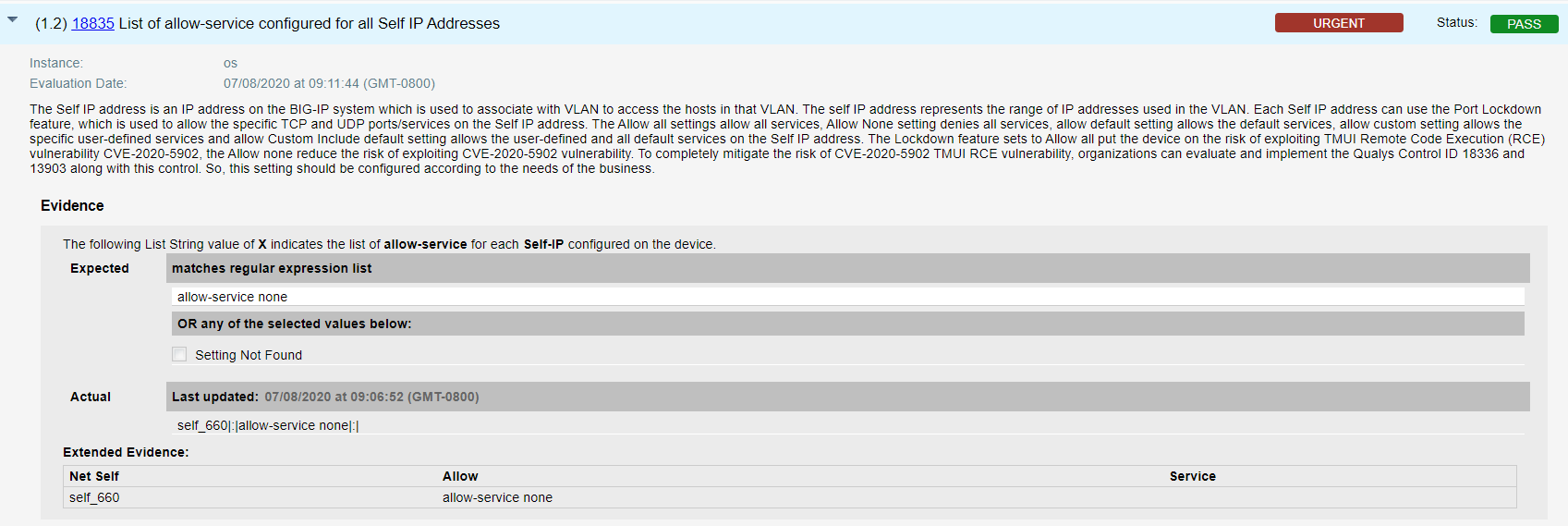
F5 BIG IP Remote Code Execution Vulnerability CVE 2020 5902 
Yasser Elmashad on LinkedIn zerotrust accesscontrol f5 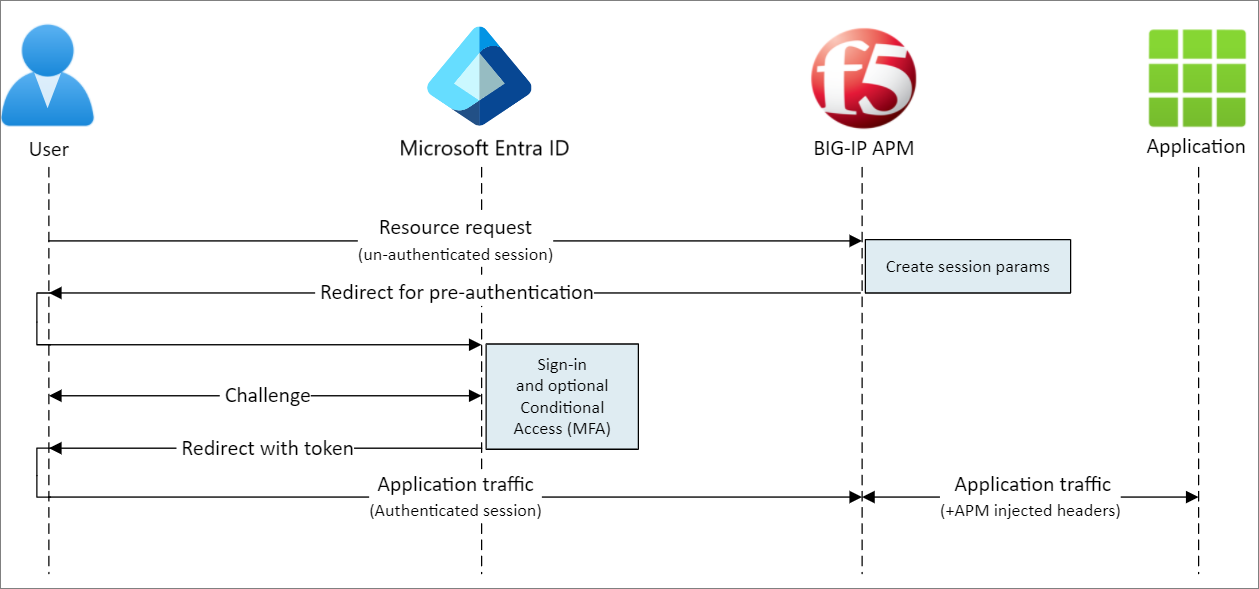
Configure F5 BIG IP Access Policy Manager for header based single 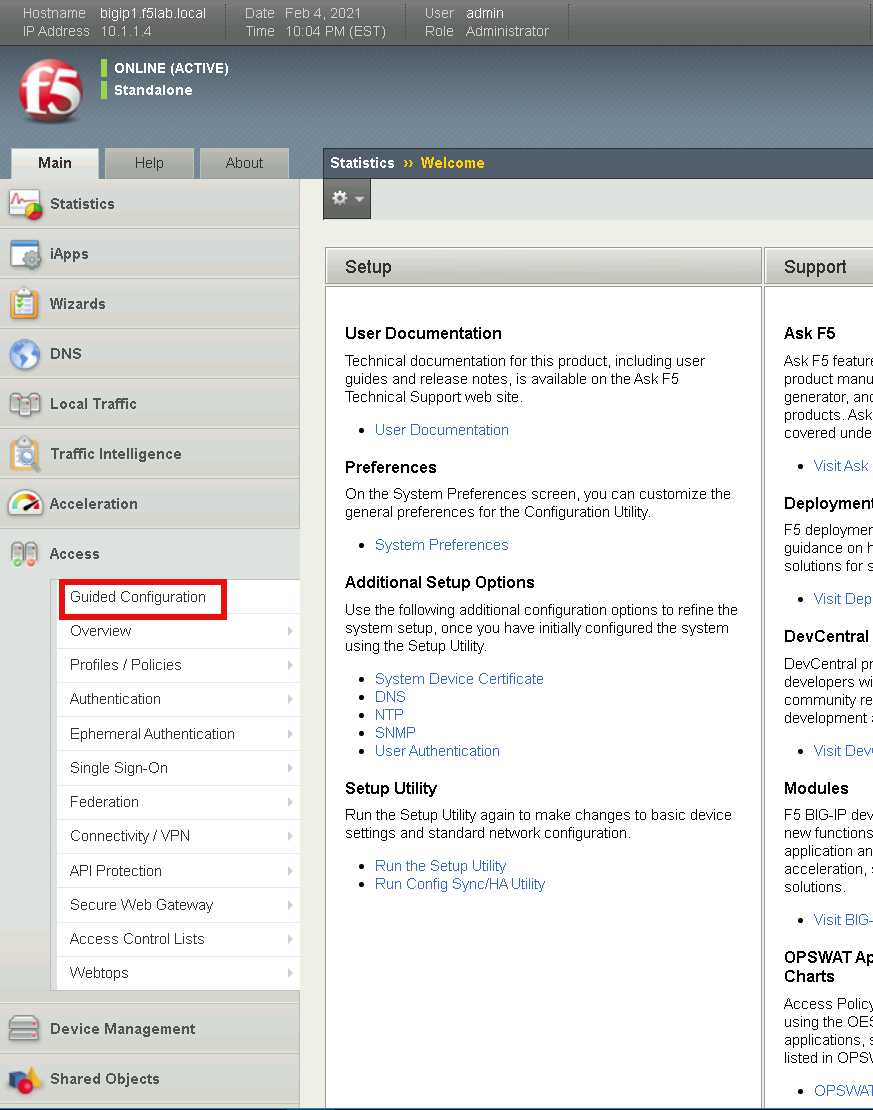
Lab 1 Configure Identity Aware Proxy 16.0 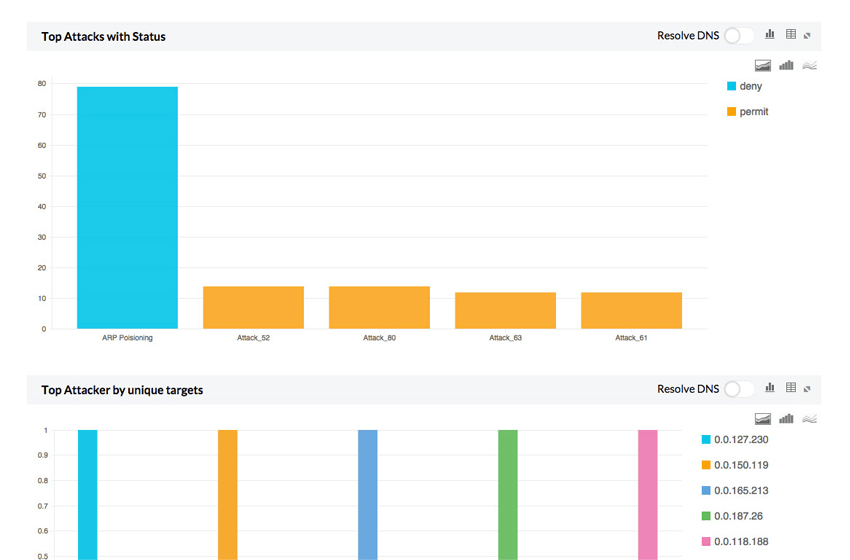
F5 Big IP Firewall Logs F5 Big IP Log Analyzer ManageEngine 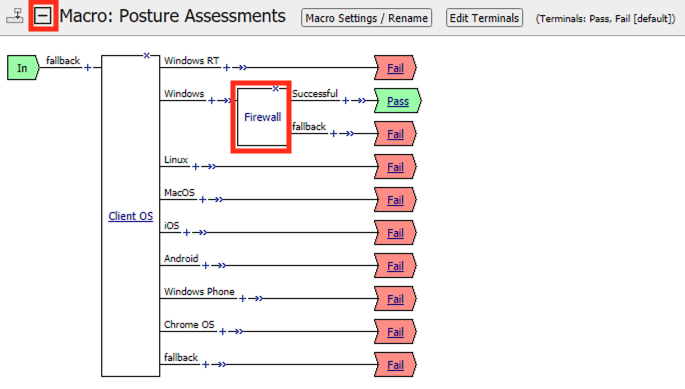
Lab 1 The Message Box 
Access Manager F5 APM Udemy 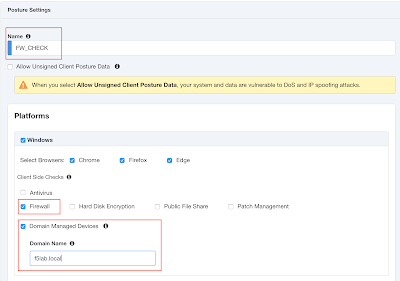
F5 BIG IP APM Identity aware proxy IAP 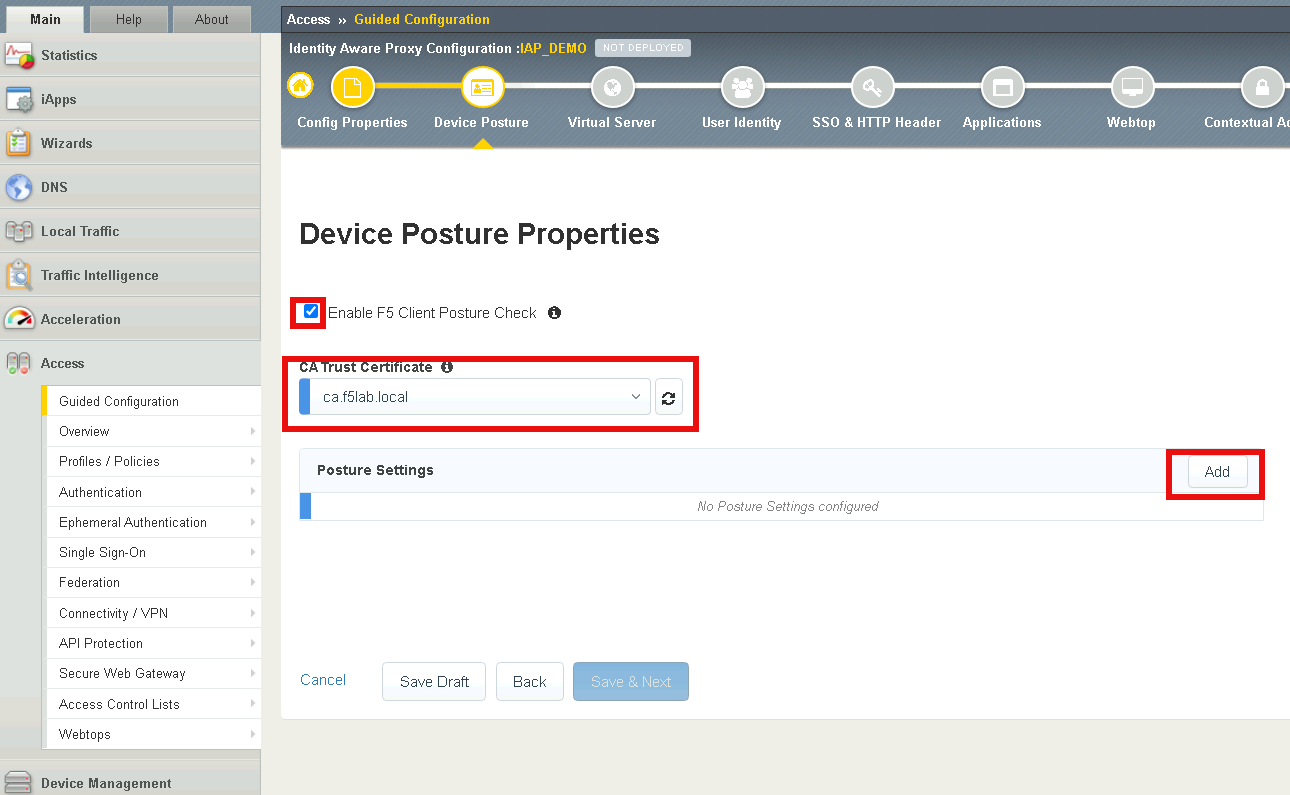
Lab 1 Configure Identity Aware Proxy 16.0 
F5 BIG IP APM Identity Aware Proxy IAP and Zero Trust F5 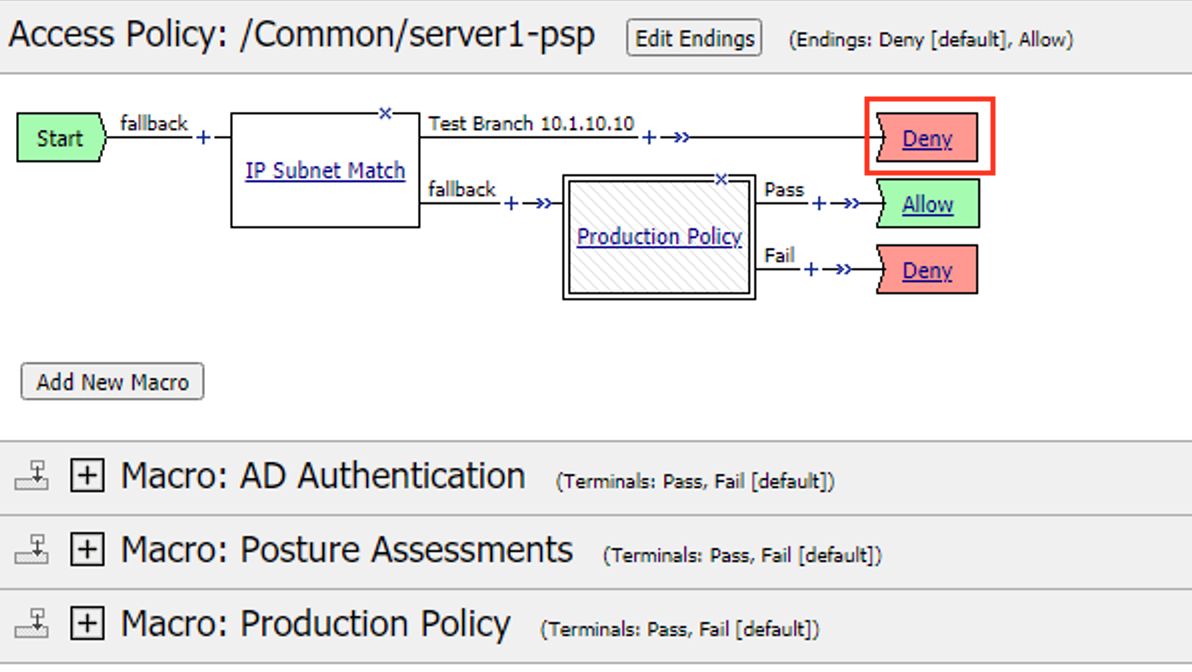
Lab 1 The Message Box 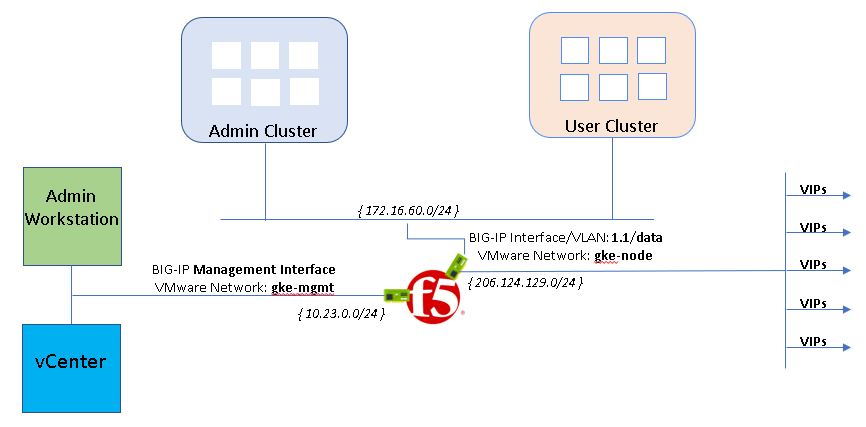
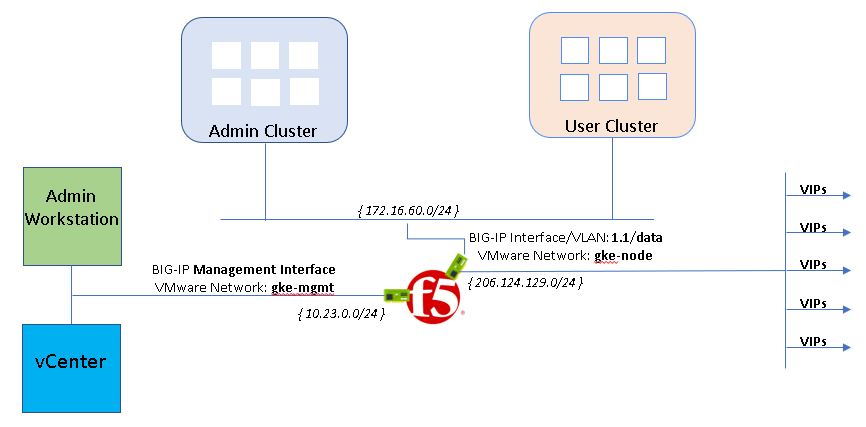
Installing F5 BIG IP ADC for GKE on VMware using manual load 
F5 BIG IP APM Identity aware proxy IAP 
Migrating from Citrix NetScaler to F5 BIG IP History Migration 
BIG IP Access Policy Manager 
Use cases BIG IP APM operations guide 
F5 ASM HEALTH CHECKS PDF 
F5 BIG IP APM Identity aware proxy IAP 
What is BIG IP Understanding F5 s Software Products WorldTech IT