Kerberos Authentication with End User Logons
F5 hot sale apm krb5.conf
Share.
Visit »

F5 Big IP Vulnerable to Security Bypass Bug Threatpost 
f5 Apm Operations Guide PDF PDF Command Line Interface 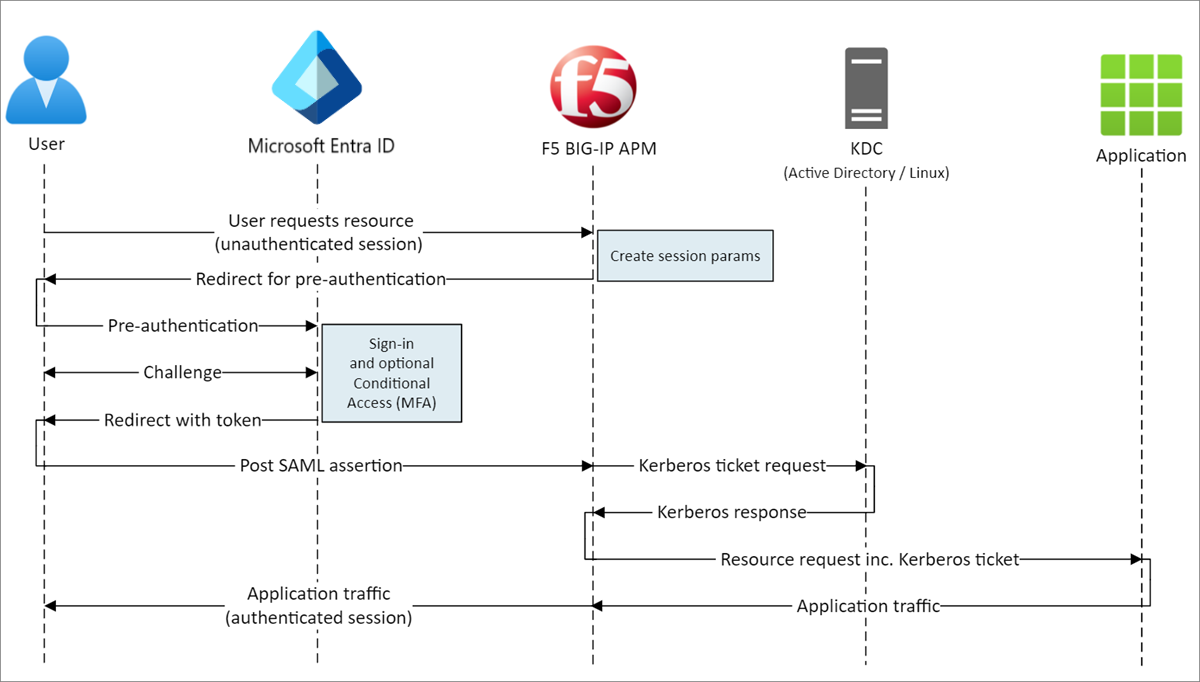
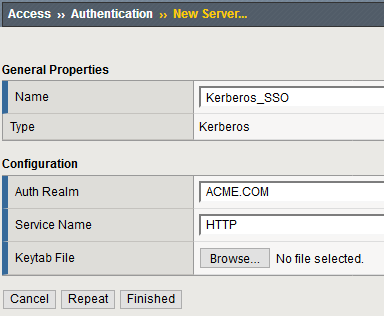
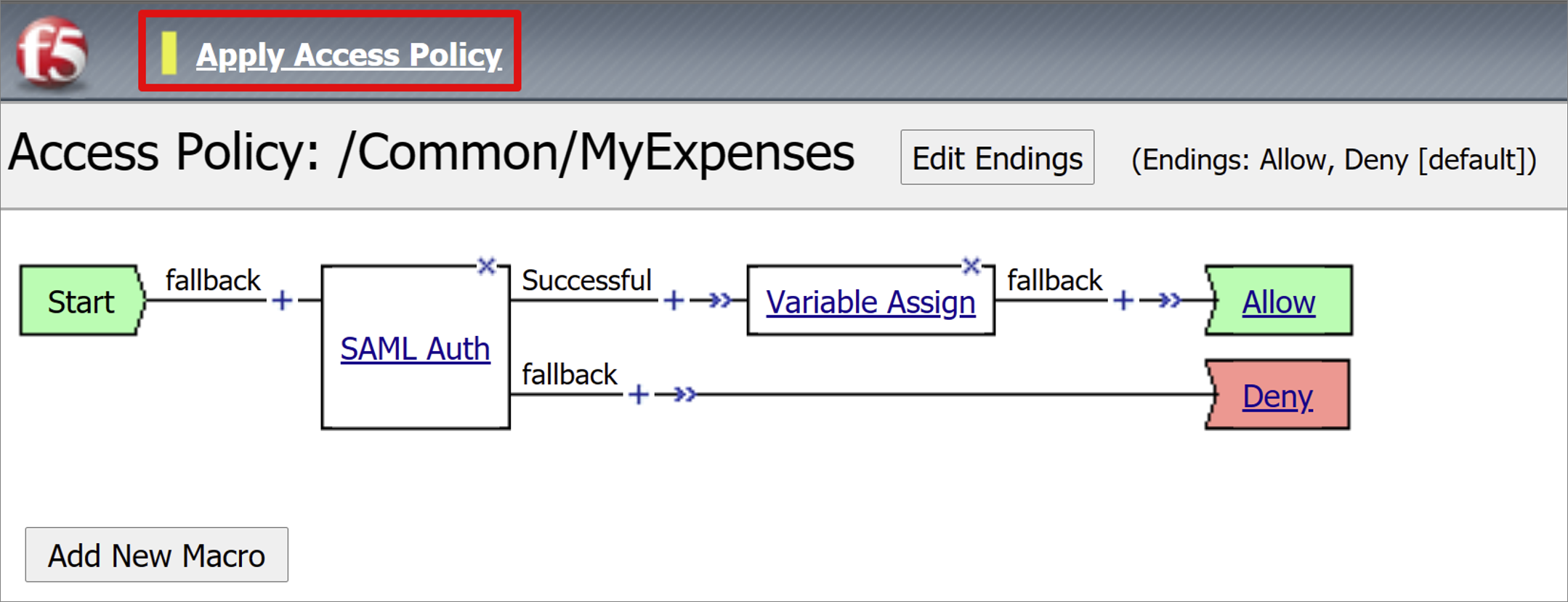
Configure F5 BIG IP Access Policy Manager for Kerberos 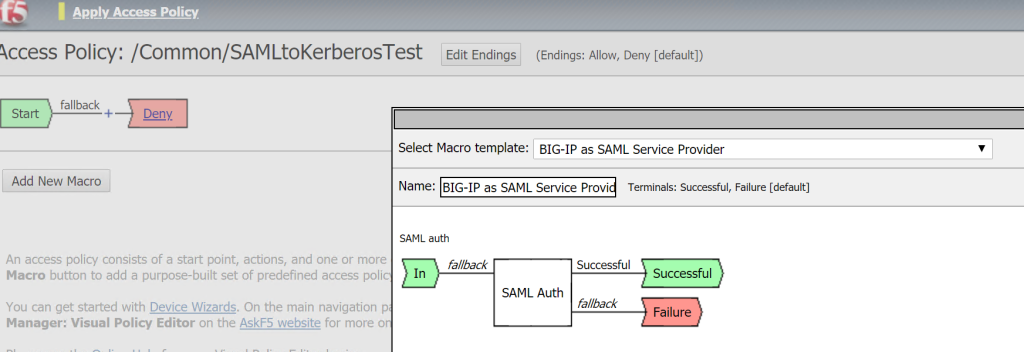
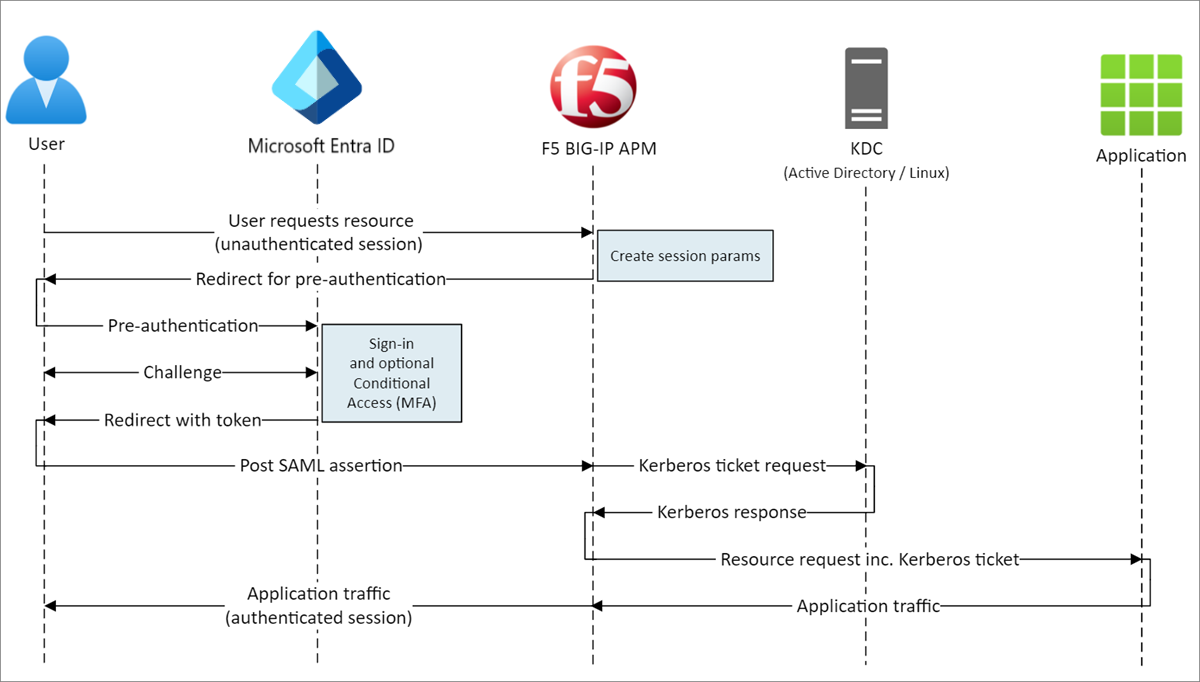
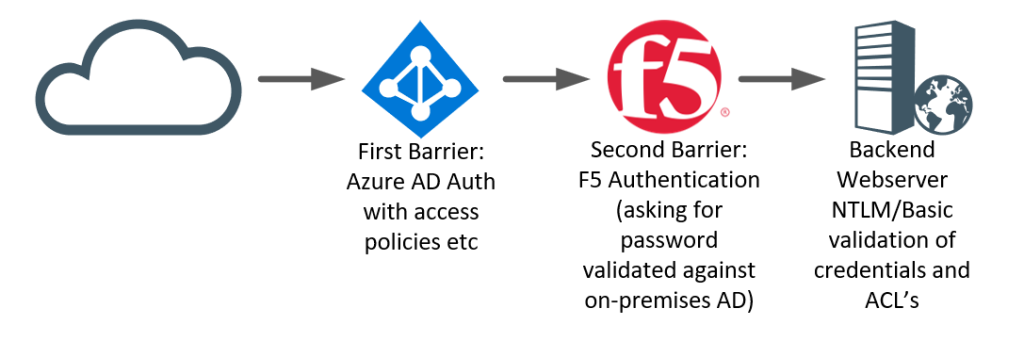
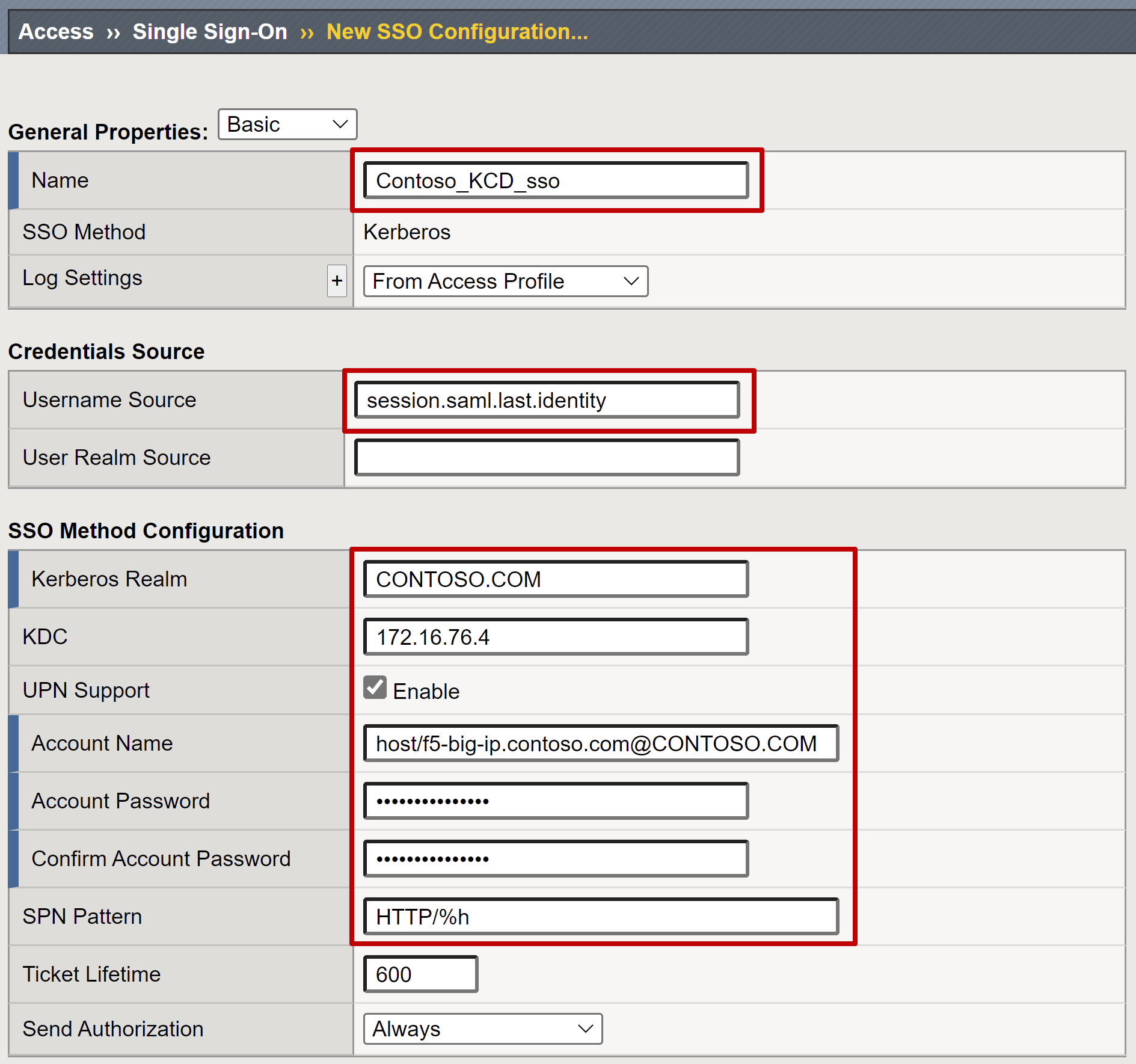
F5 Big IP AAD KCD 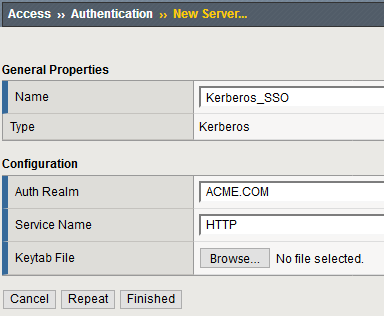
Reference Kerberos AAA Object 
Kerberos Authentication with End User Logons 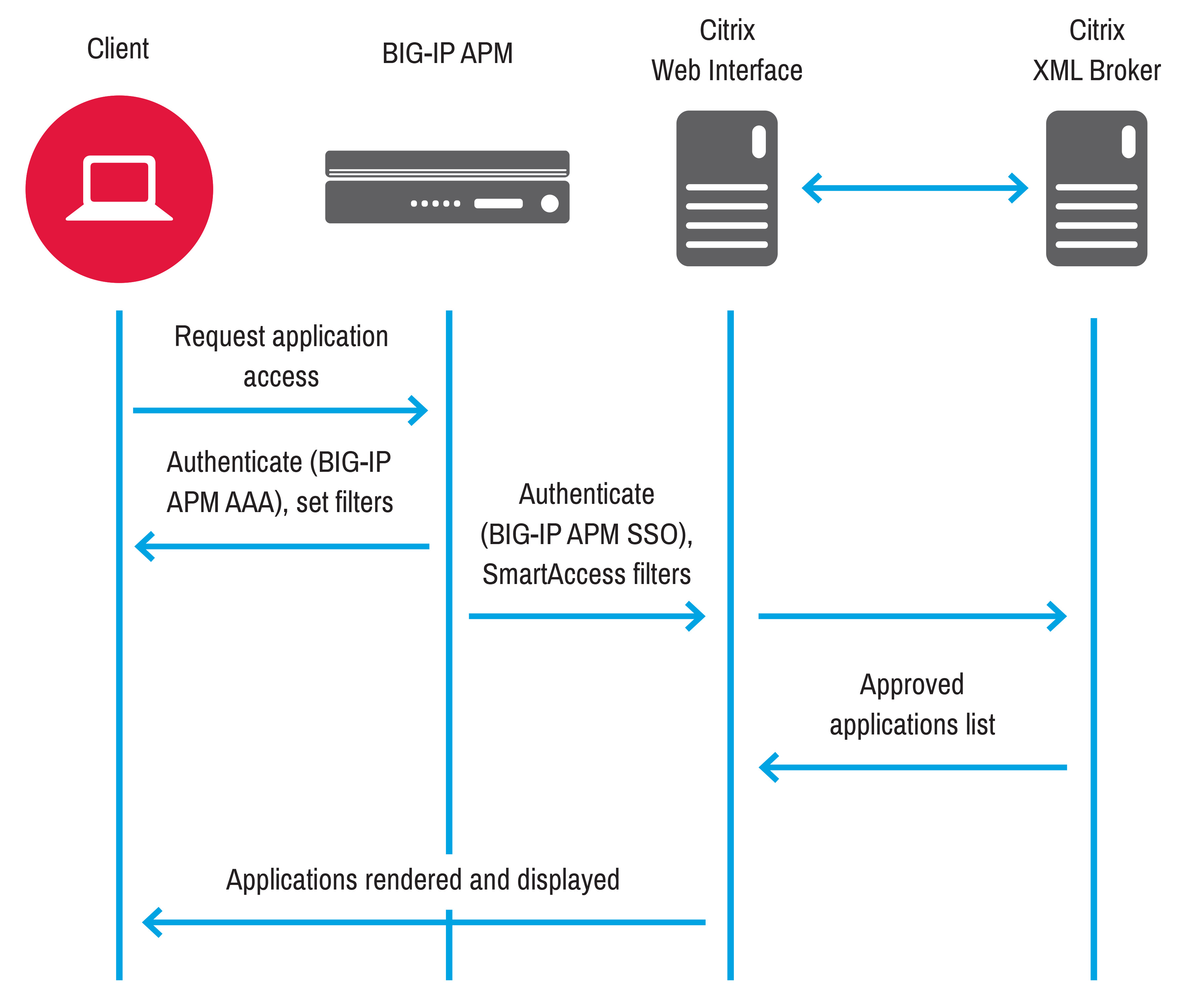
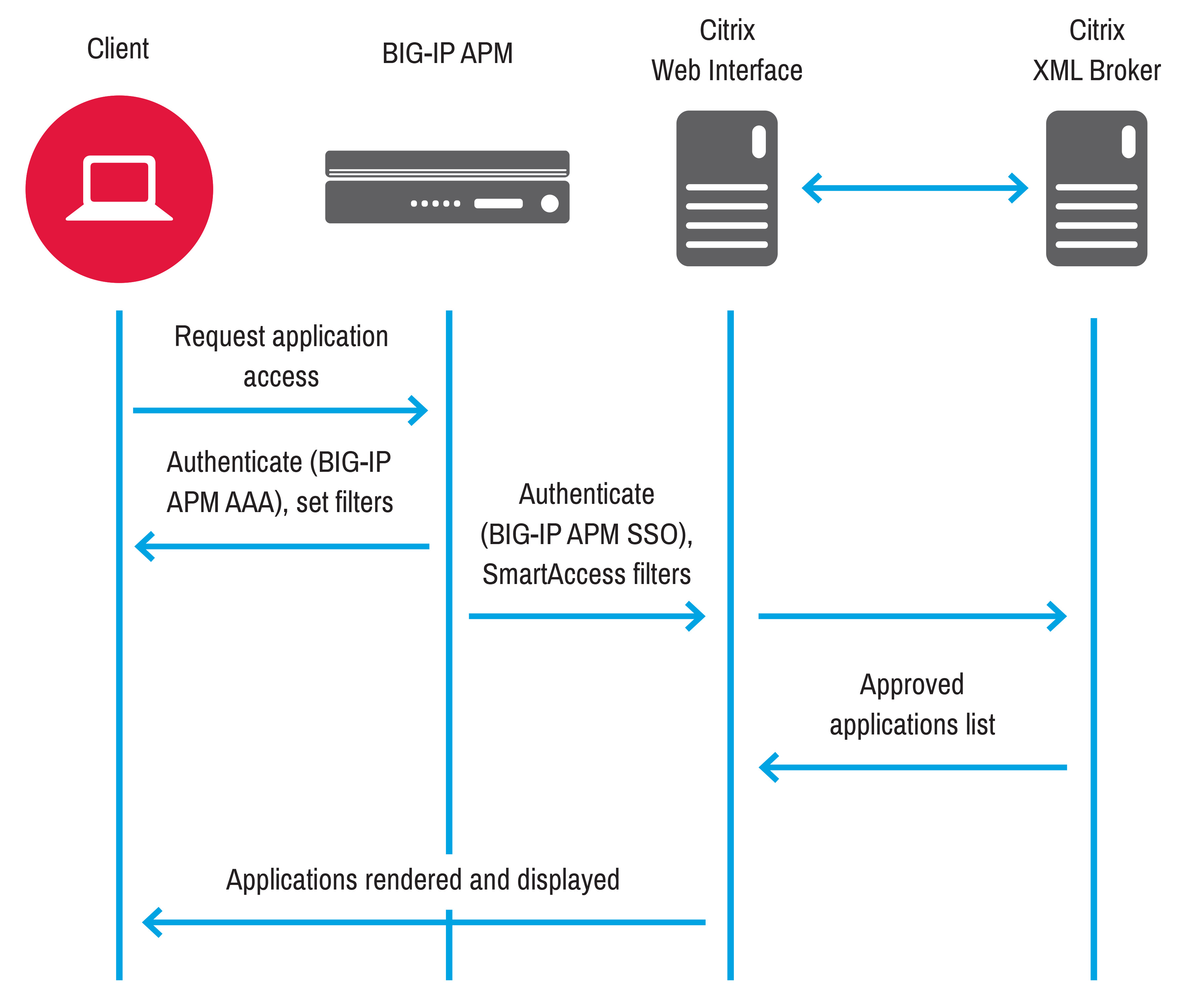
Use cases BIG IP APM operations guide 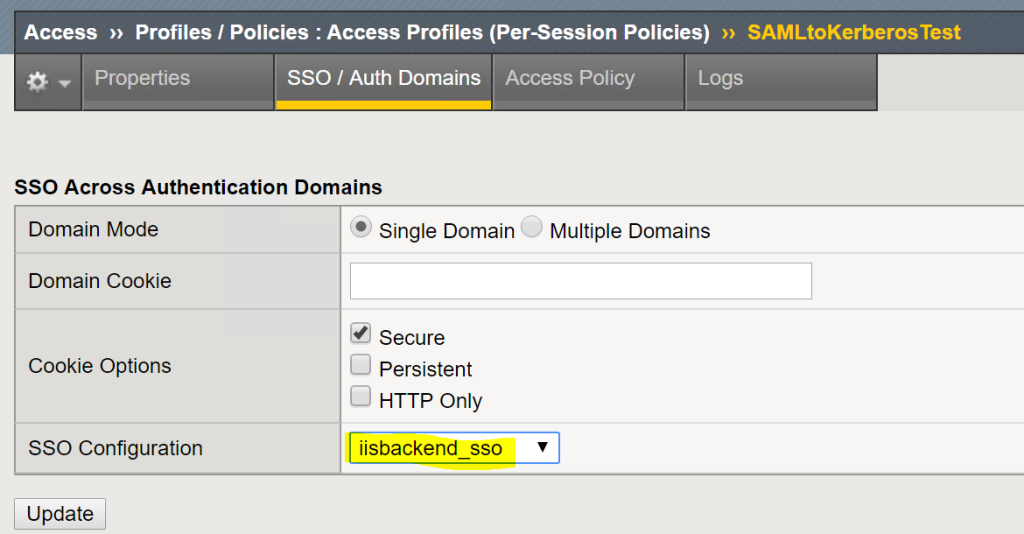
F5 Big IP AAD KCD 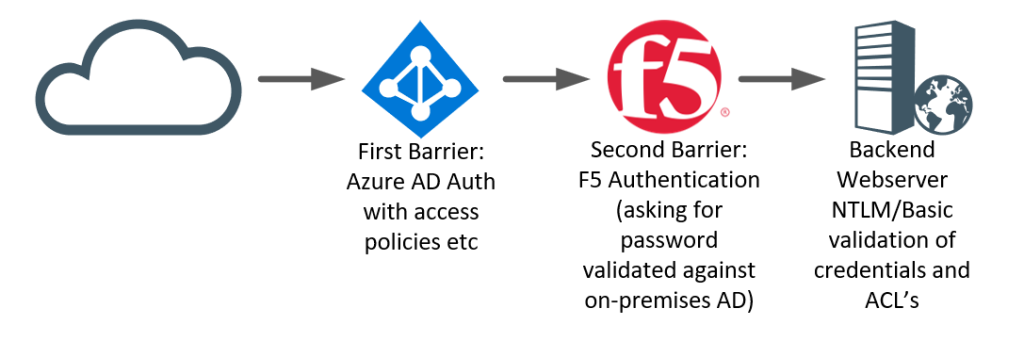
F5 Big IP AAD BASIC NTLM 
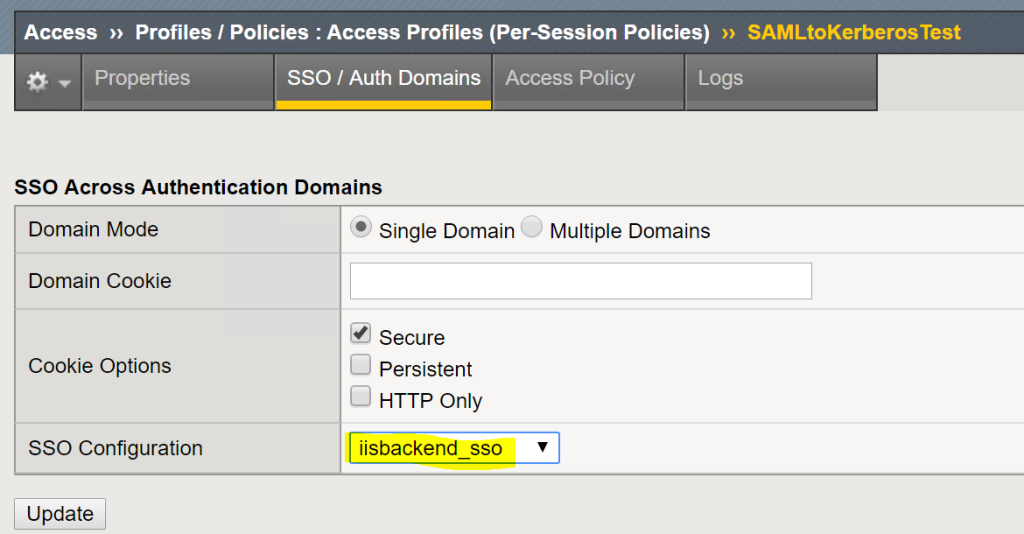
F5 BIG IP APM SSO via NTLM 
F5 BIG IP APM SSO via Kerberos 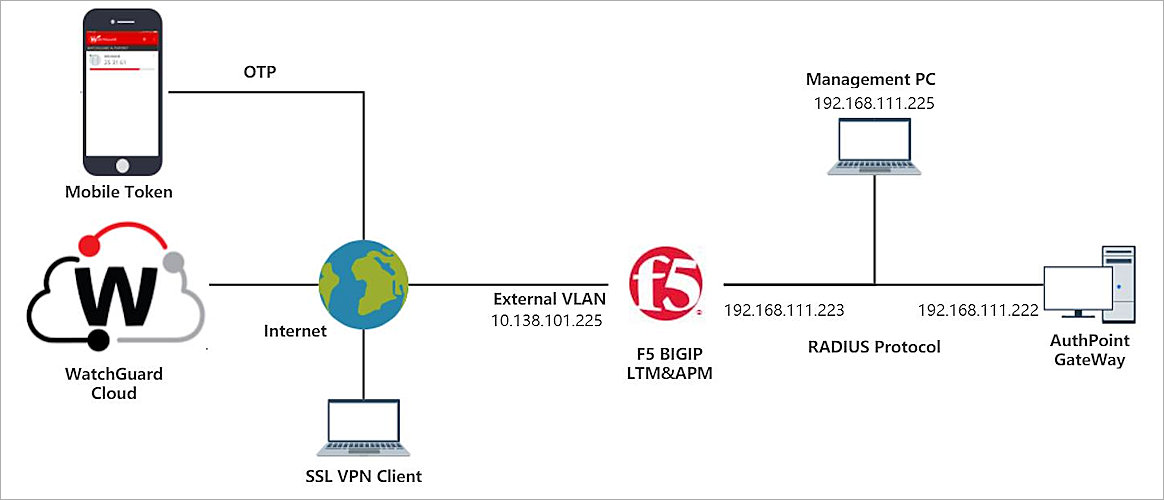
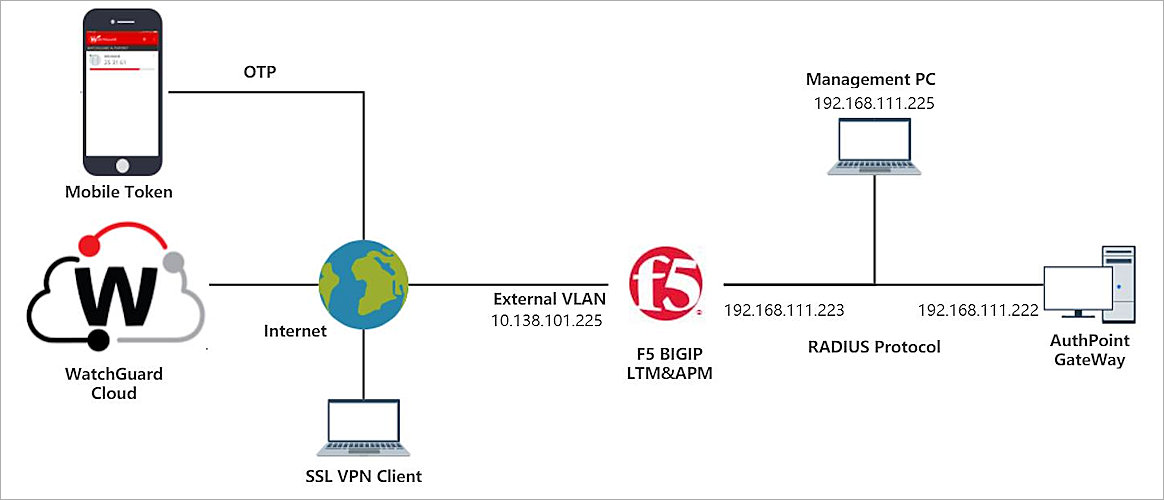
F5 BIG IP APM RADIUS Integration with AuthPoint 
F5 BIG IP APM IdP Initiated for Office 365 
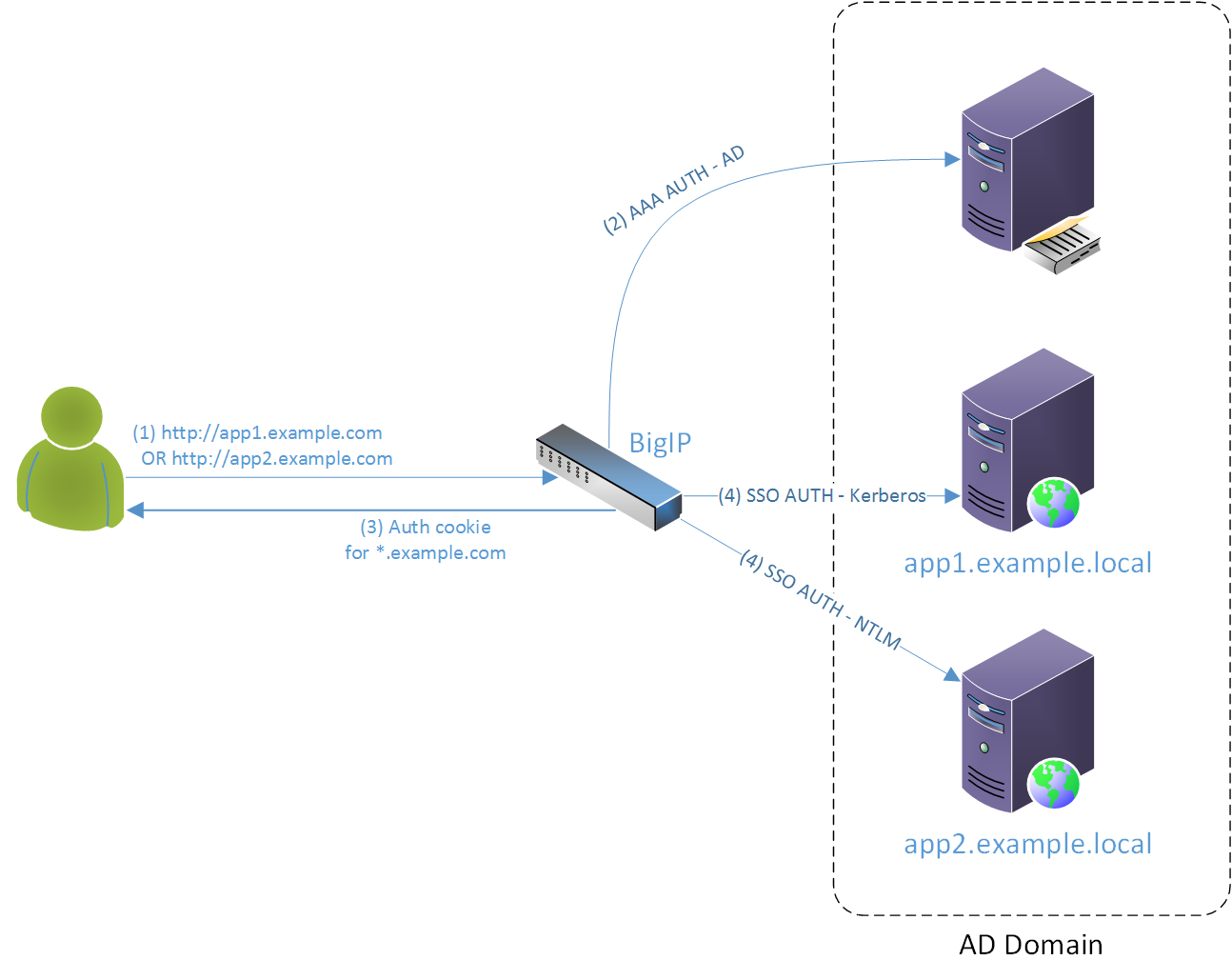
IMPLEMENTING SINGLE SIGN ON SSO TO KERBEROS CONSTRAINED 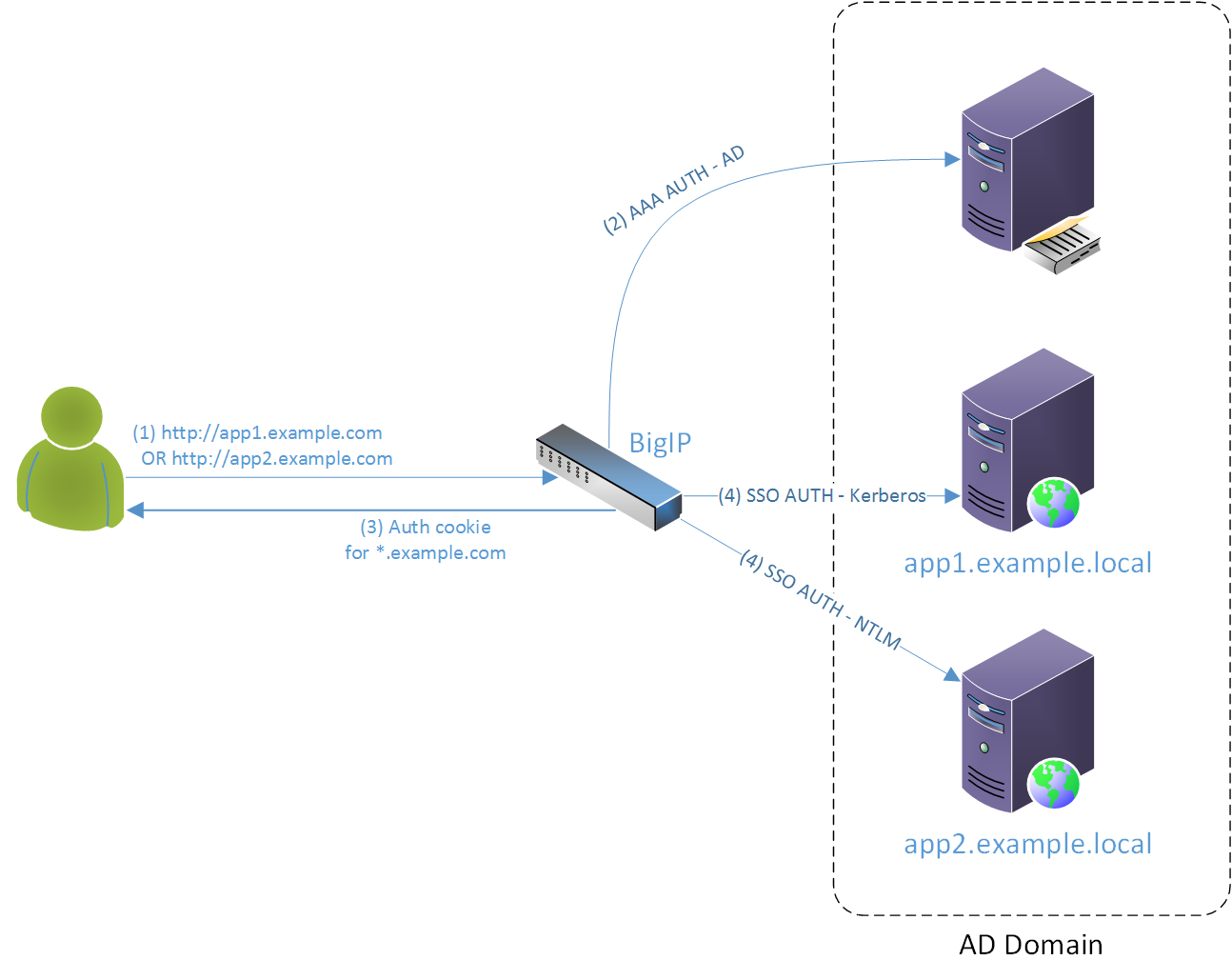
F5 BigIP APM v.12 SSO using AD Kerberos Quick How To 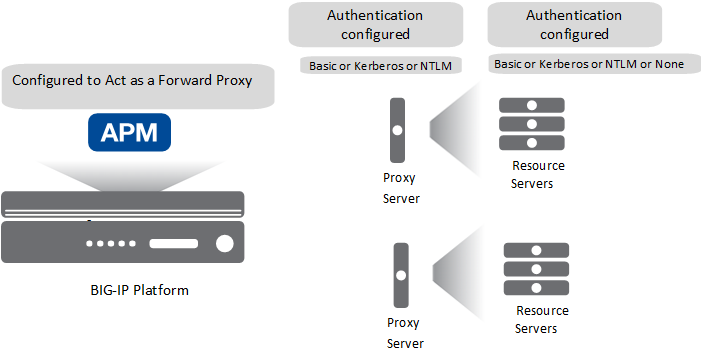
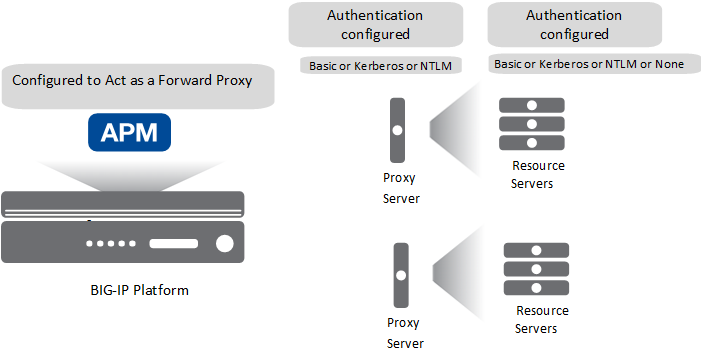
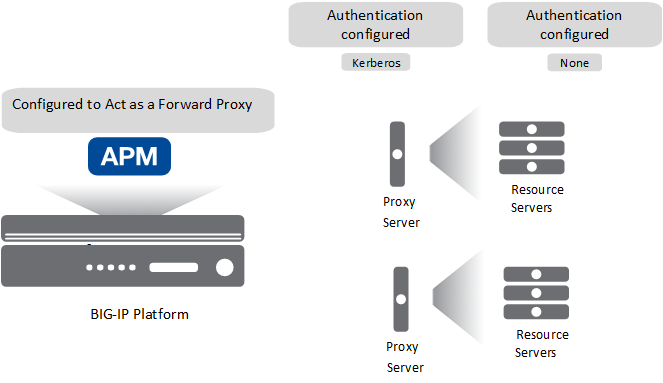
Forward Proxy Chaining with APM 
F5 APM SSO Forms Client Initiated Configuration YouTube 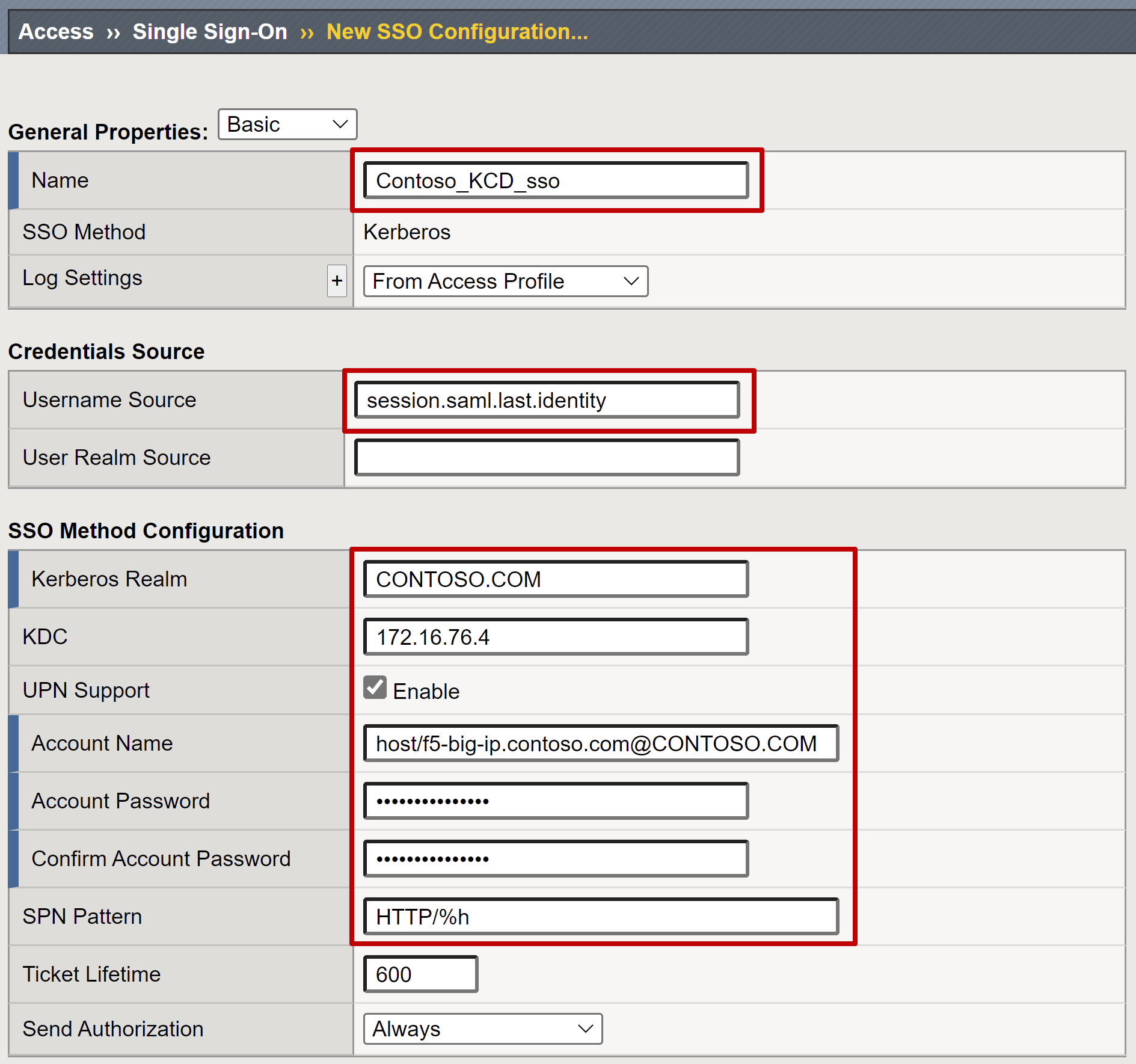
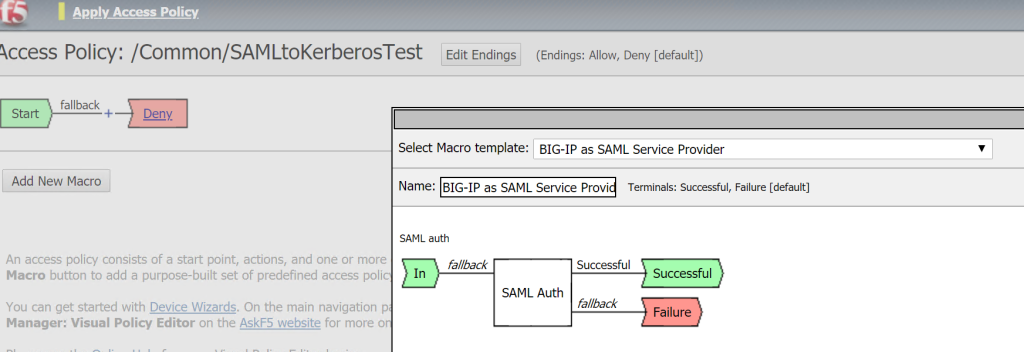
Configure F5 BIG IP Access Policy Manager for Kerberos 
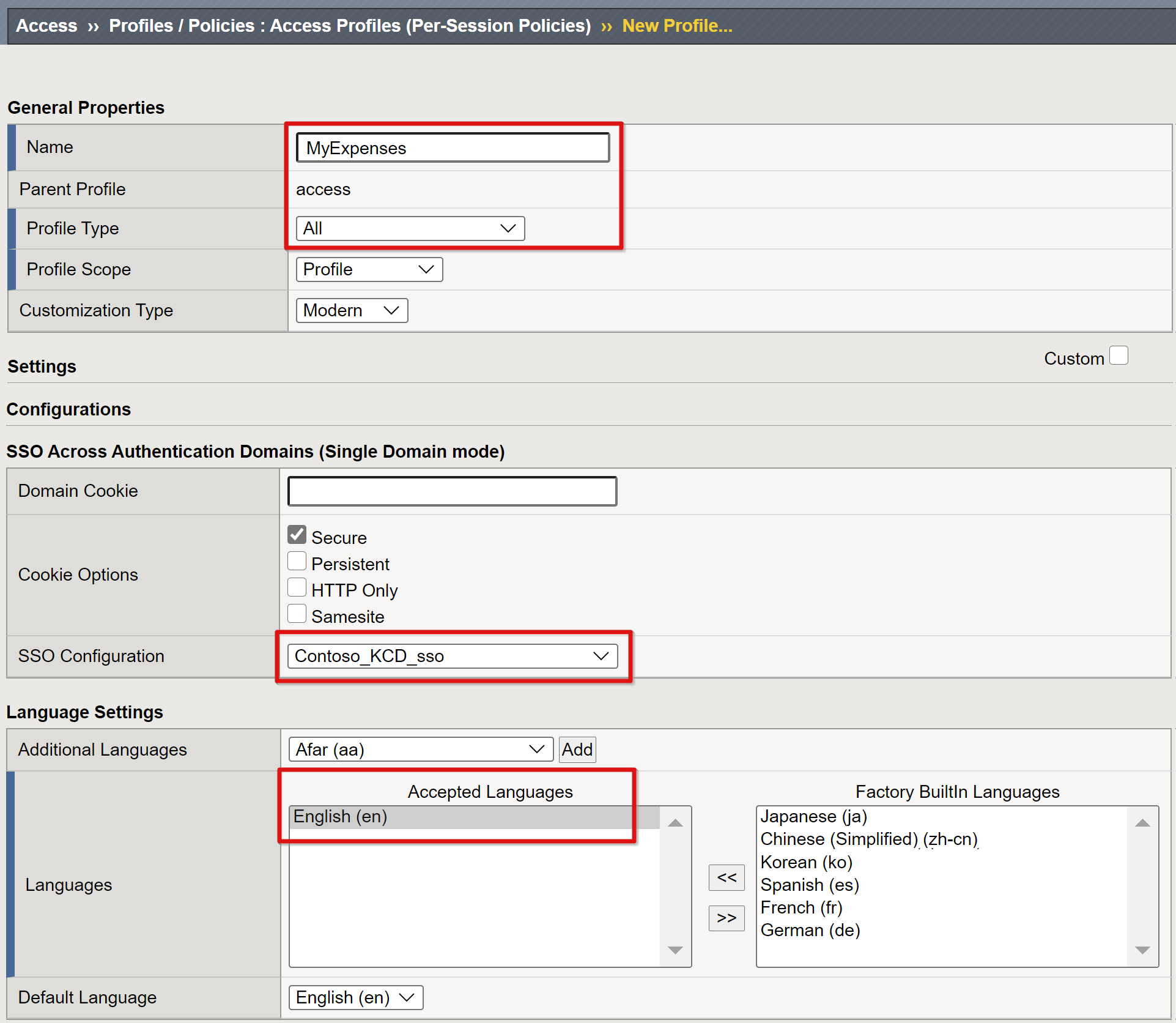
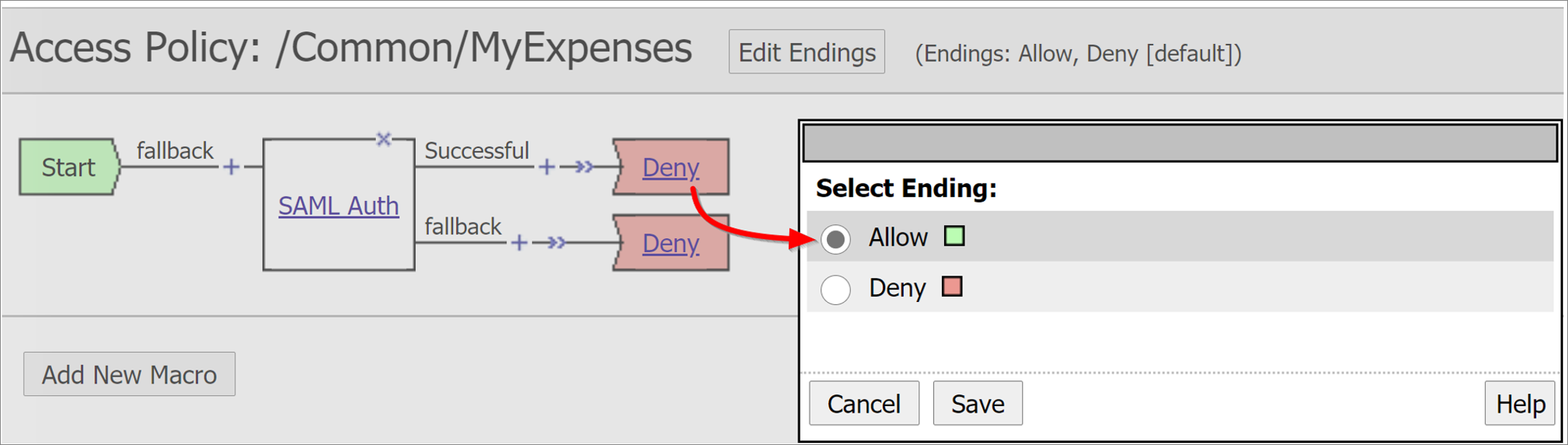
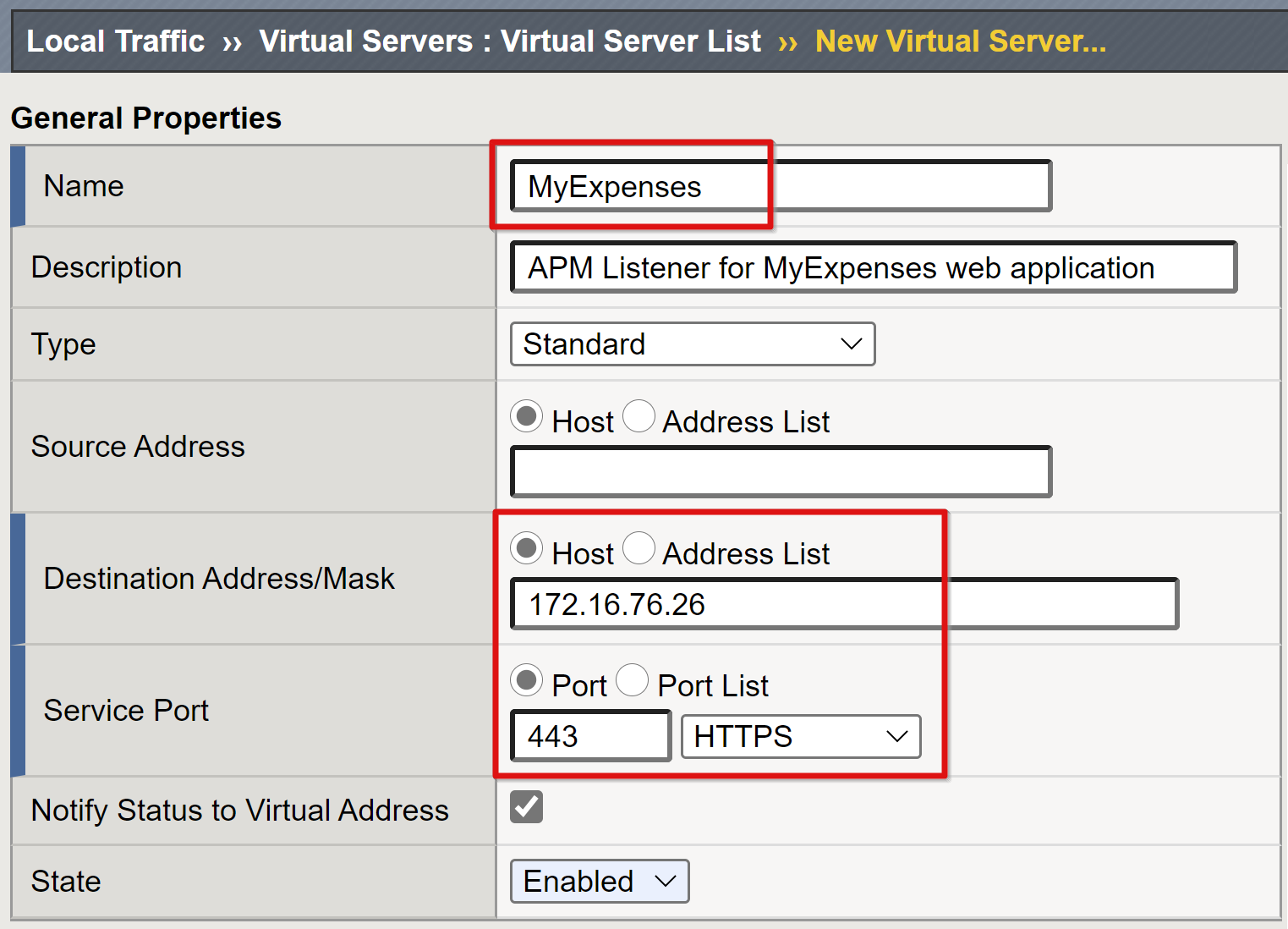
F5 BIG IP AAD KCD Simplified 
Use cases BIG IP APM operations guide 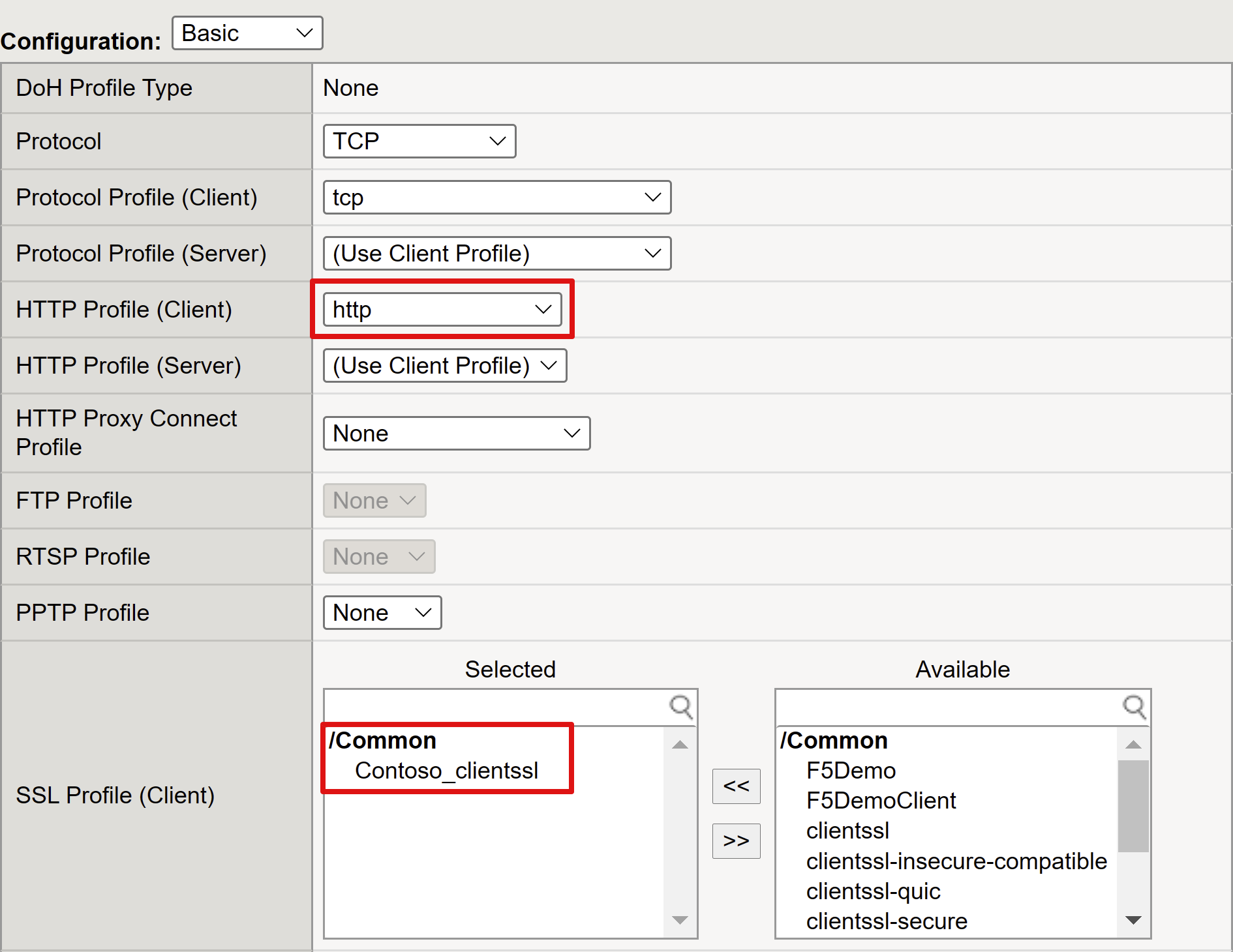
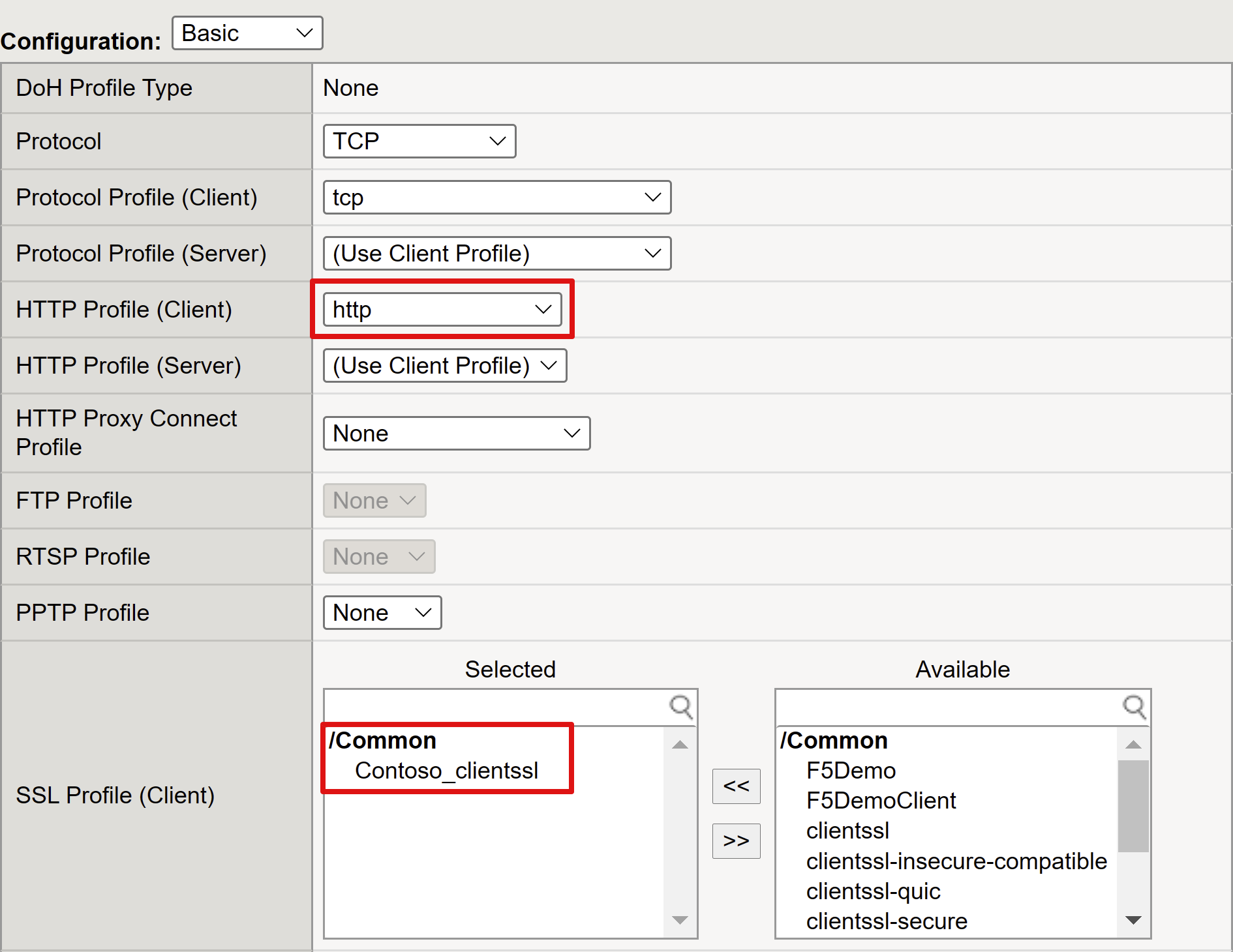
Configure F5 BIG IP Access Policy Manager for Kerberos 
Kerberos Single Sign On Method 
Kerberos Authentication with End User Logons 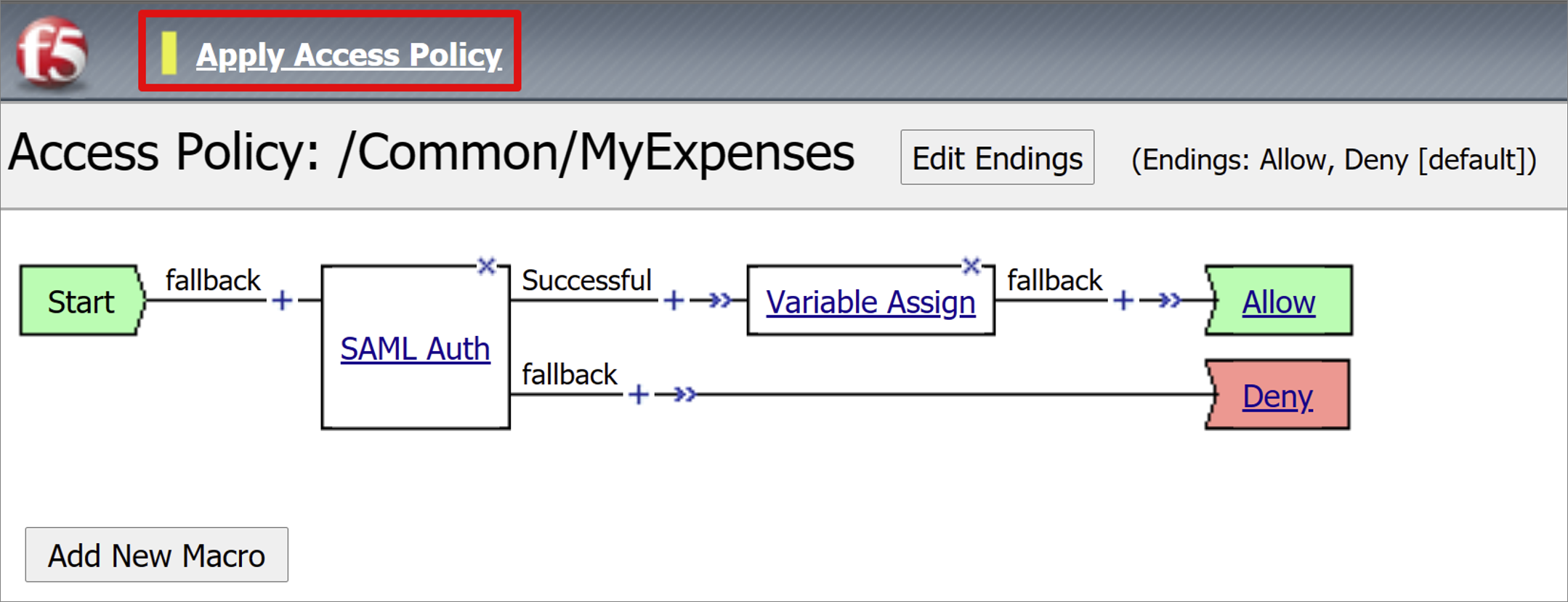
Configure F5 BIG IP Access Policy Manager for Kerberos 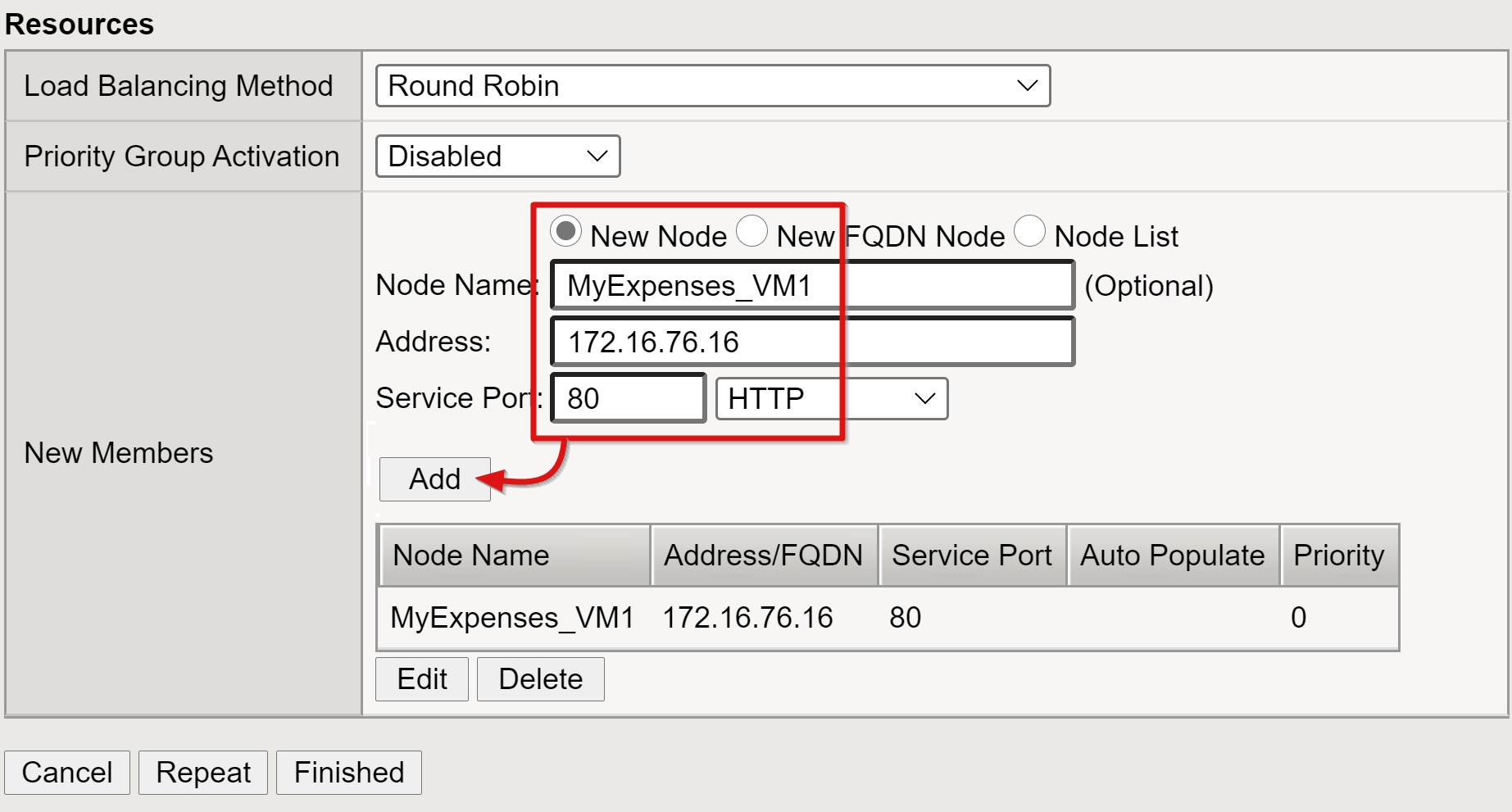
Configure F5 BIG IP Access Policy Manager for Kerberos 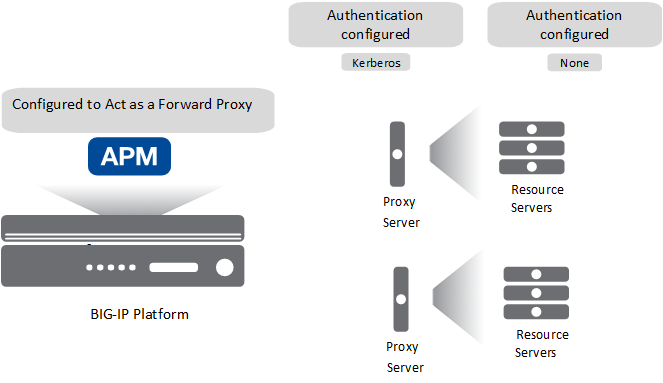
Forward Proxy Chaining with APM 
IMPLEMENTING SINGLE SIGN ON SSO TO KERBEROS CONSTRAINED 
IMPLEMENTING SINGLE SIGN ON SSO TO KERBEROS CONSTRAINED 
F5 BigIP APM v.12 SSO using AD Kerberos Quick How To 
F5 APM Kerberos AUTH 
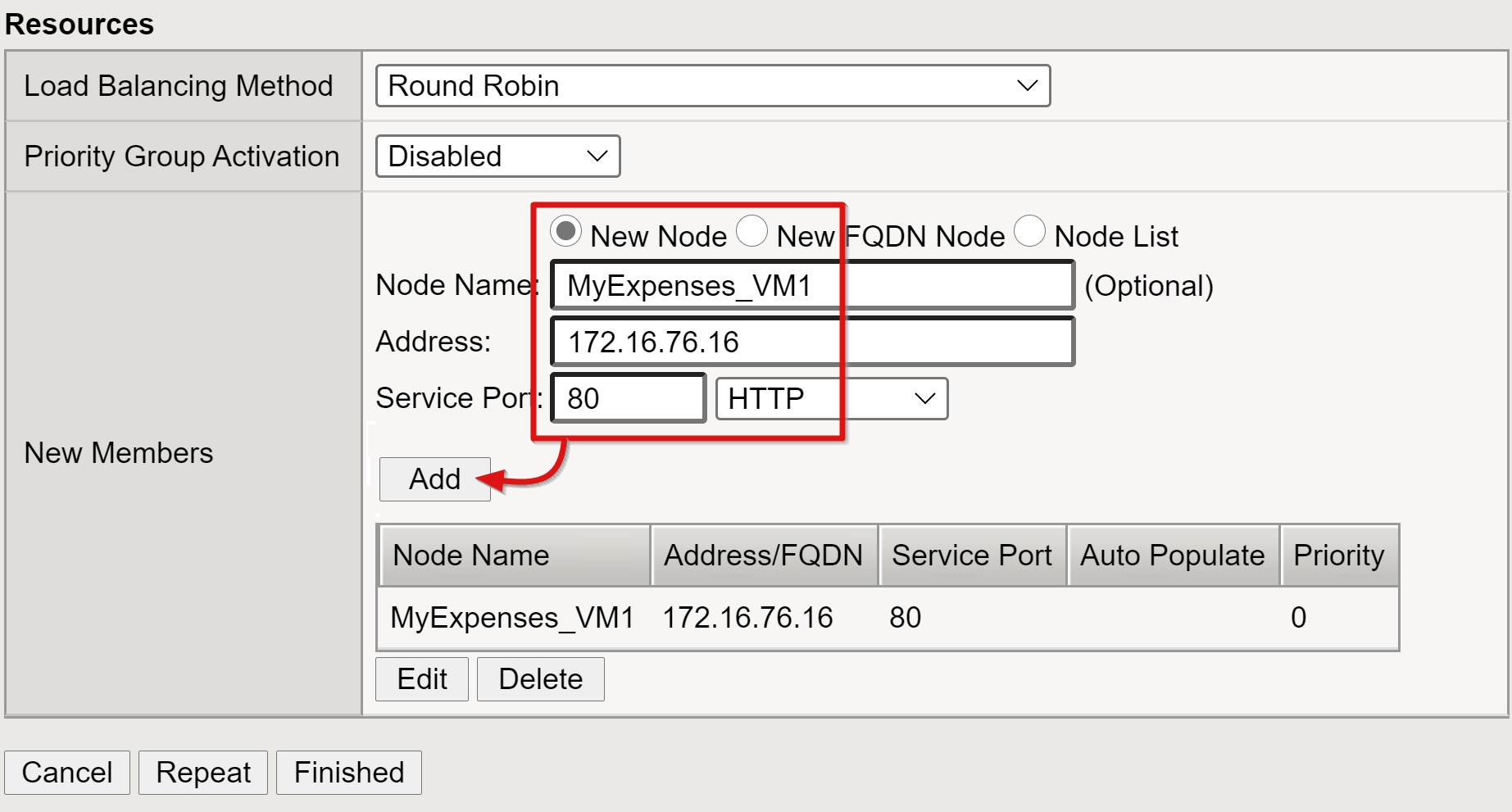
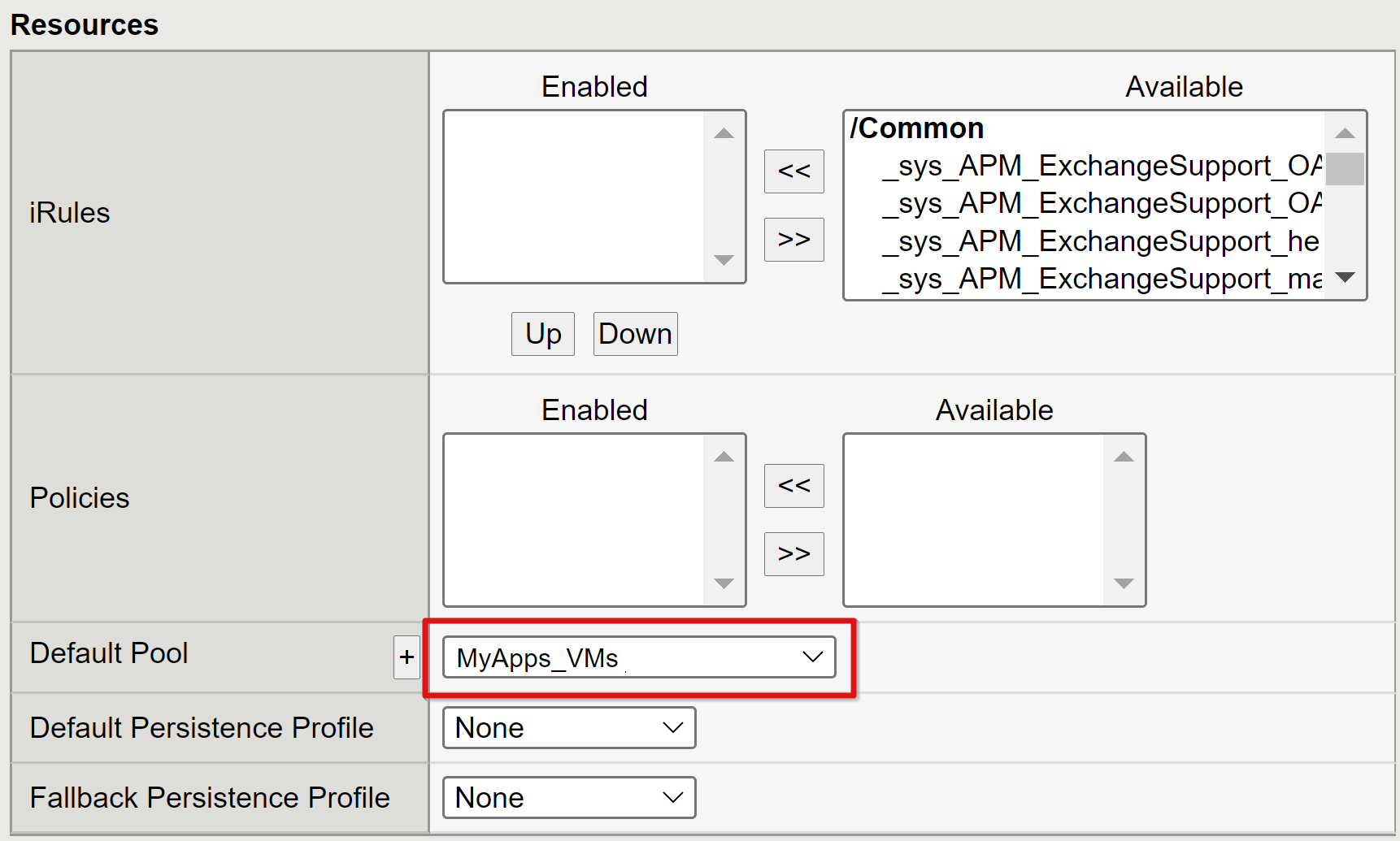
F5 APM SSO Forms Client Initiated Configuration 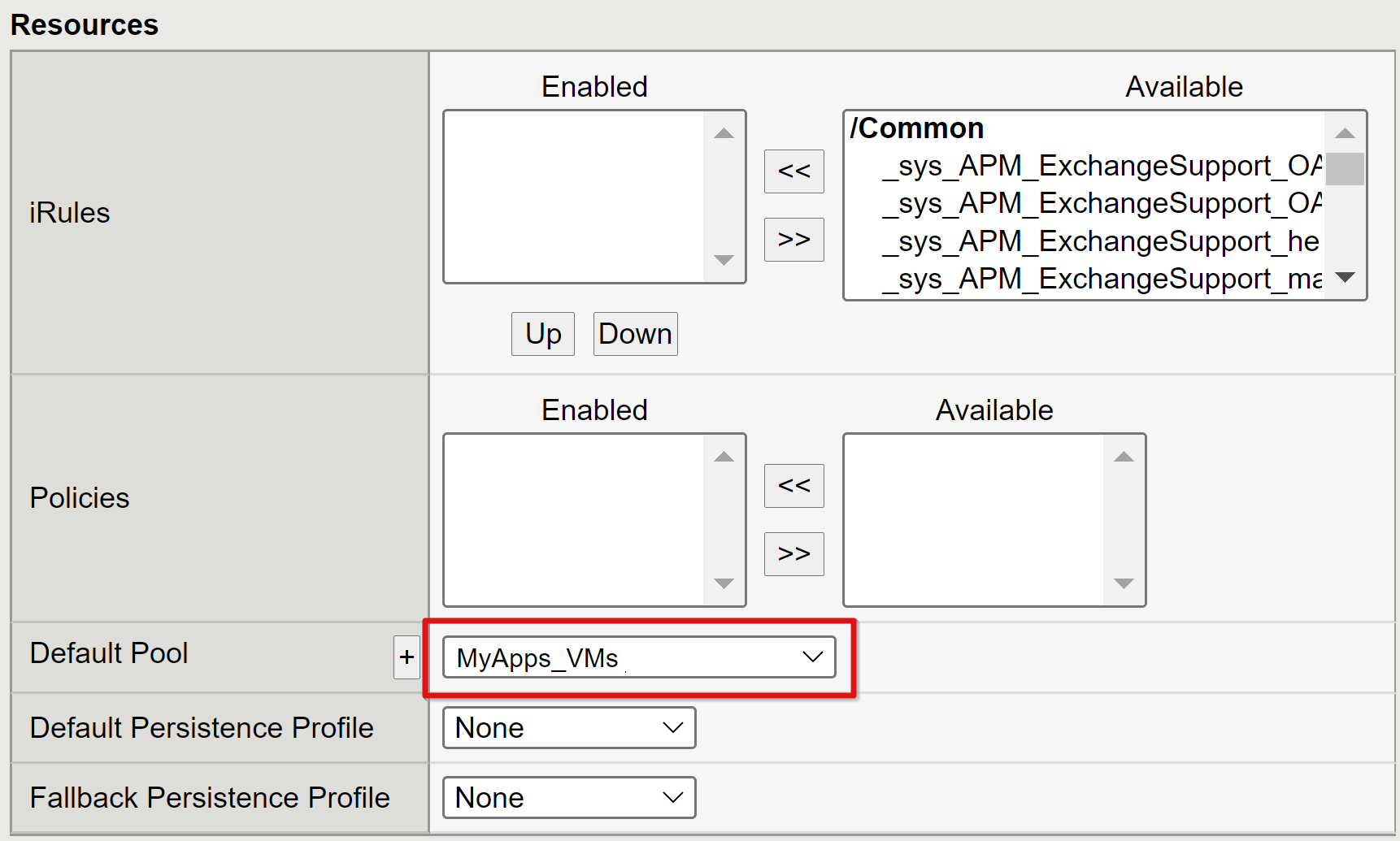
Configure F5 BIG IP Access Policy Manager for Kerberos 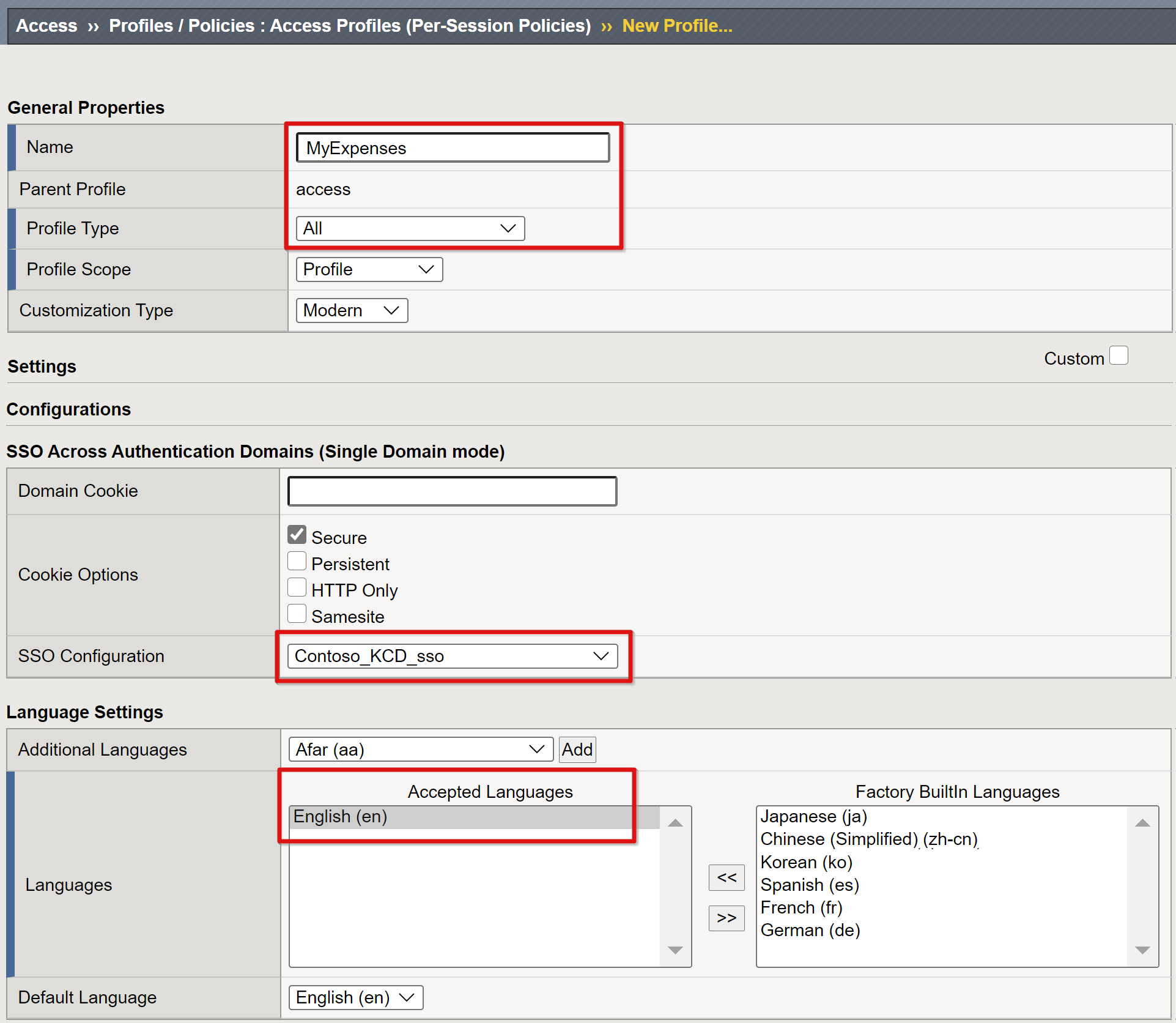
Configure F5 BIG IP Access Policy Manager for Kerberos 
Configure F5 BIG IP Access Policy Manager for Kerberos 
F5 Networks BIG IP Access Policy Manager AppDeliveryWorks 
Configure F5 BIG IP Access Policy Manager for Kerberos 
Thoughts from an F5 APM Multi Factor implementation James Westall 
F5 Big IP AAD KCD 
Kerberos Authentication with End User Logons