
Gain Visibility Into Risks Vulnerabilities and Attacks With APM
Apm security use hot sale case
Share. Visit »
F5 APM HEALTH CHECKS PDF
Use cases BIG IP APM operations guide
Gartner 2023 Critical Capabilities for APM and Observability
Use cases BIG IP APM operations guide
The Leading APM Use Cases Logit.io
Use cases BIG IP APM operations guide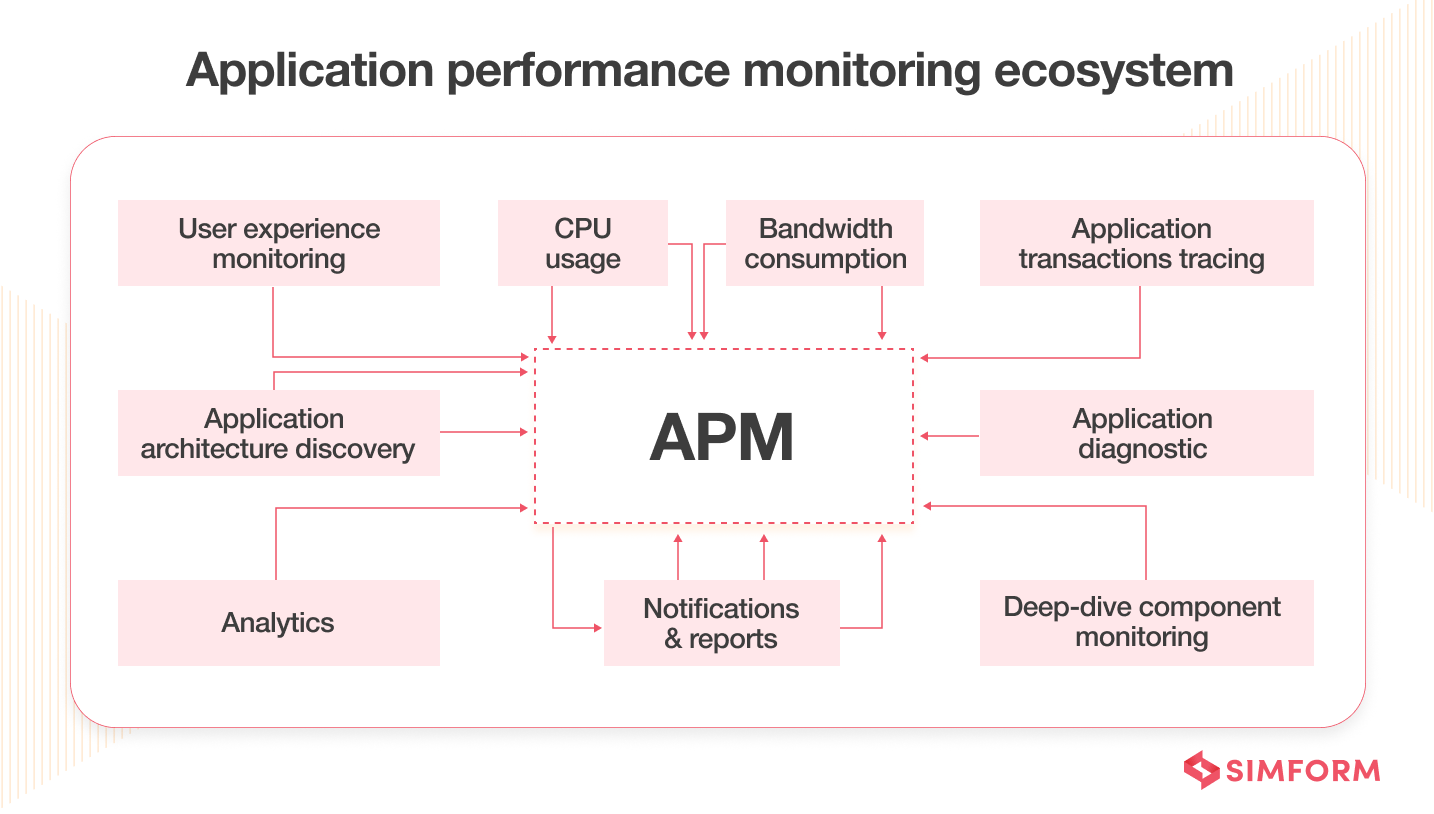
From Traditional APM to Enterprise Observability An Ultimate Guide
3 Zero Trust Use Cases in your organization ManageEngine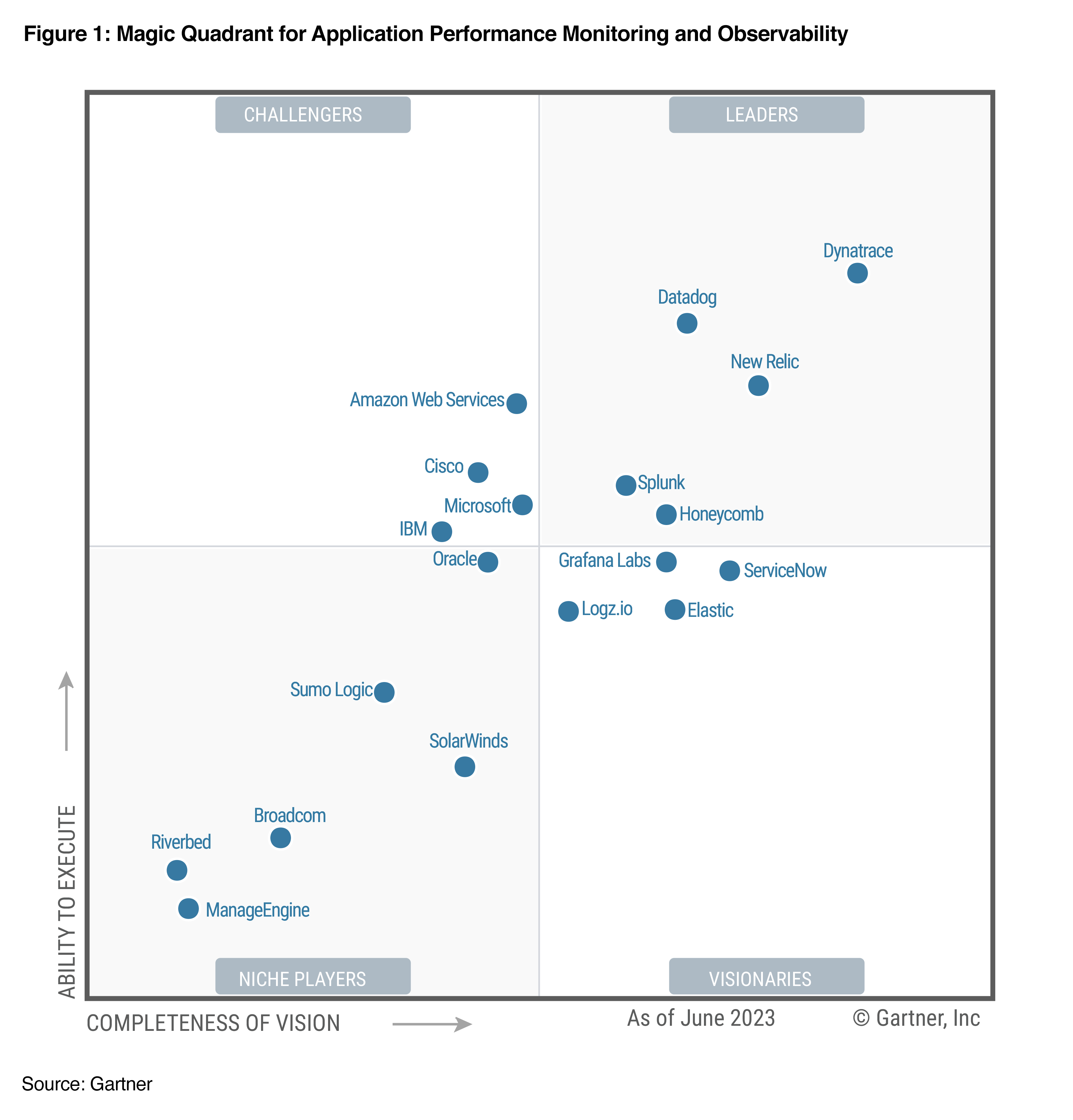
Elastic recognized as a Visionary in the 2023 Gartner Magic
Why Application Performance Monitoring APM Tool Is Important
ServiceNow APM and Bizzdesign to win at Digital Transformation
APM Security Access Control Best Practices
10 Reasons SIEM Should Remain Dedicated to Security Part 3 by
Application Portfolio Management
Application Portfolio Management Plus APM Bizzdesign
Ken Felix Security Blog F5 APM policy on a VS with a portal
Application Performance Monitoring Tools Use Cases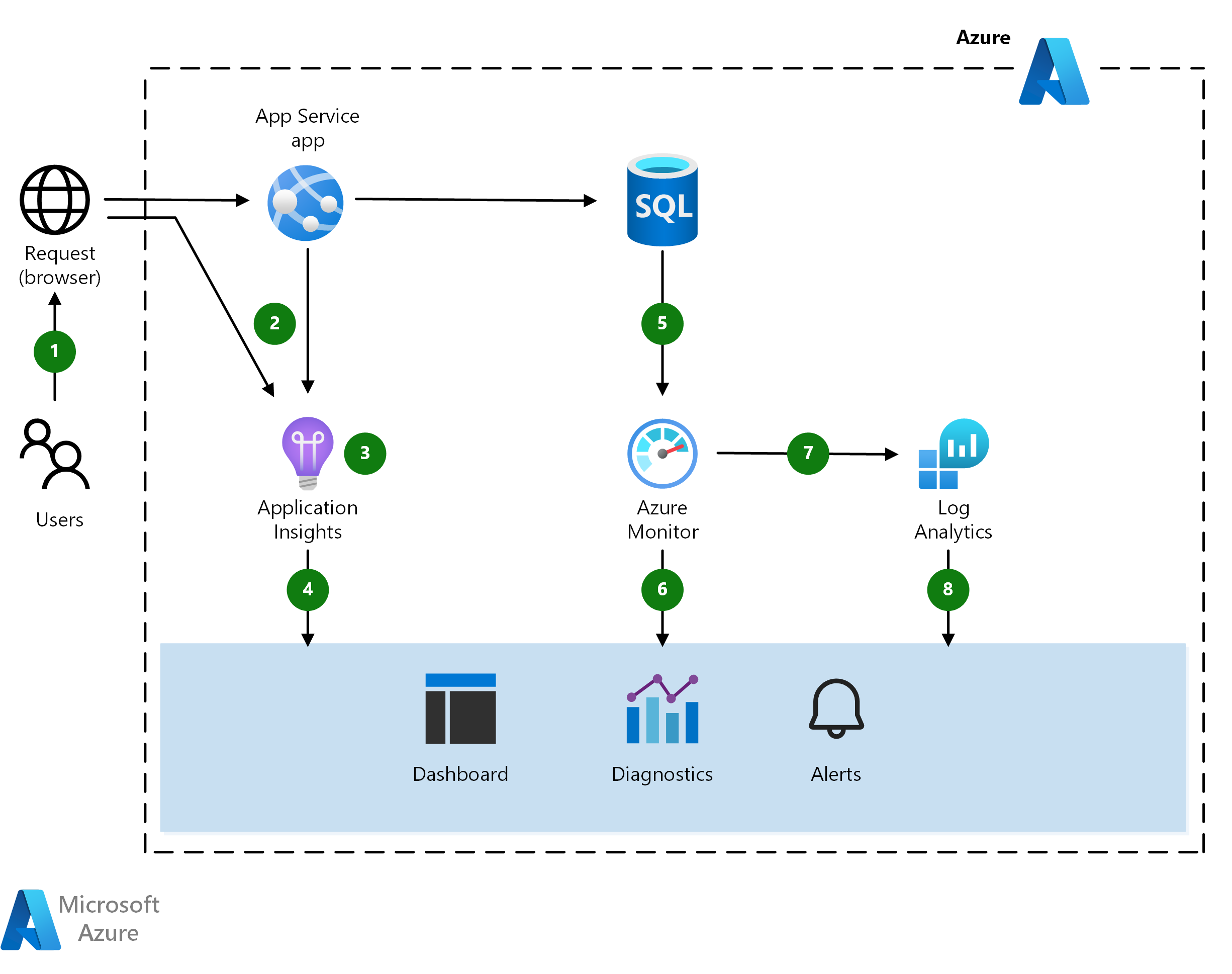
Web application monitoring on Azure Azure Architecture Center
Application Performance Monitoring Tool Why Do You Need It
Use cases misuse cases and security use cases for the case study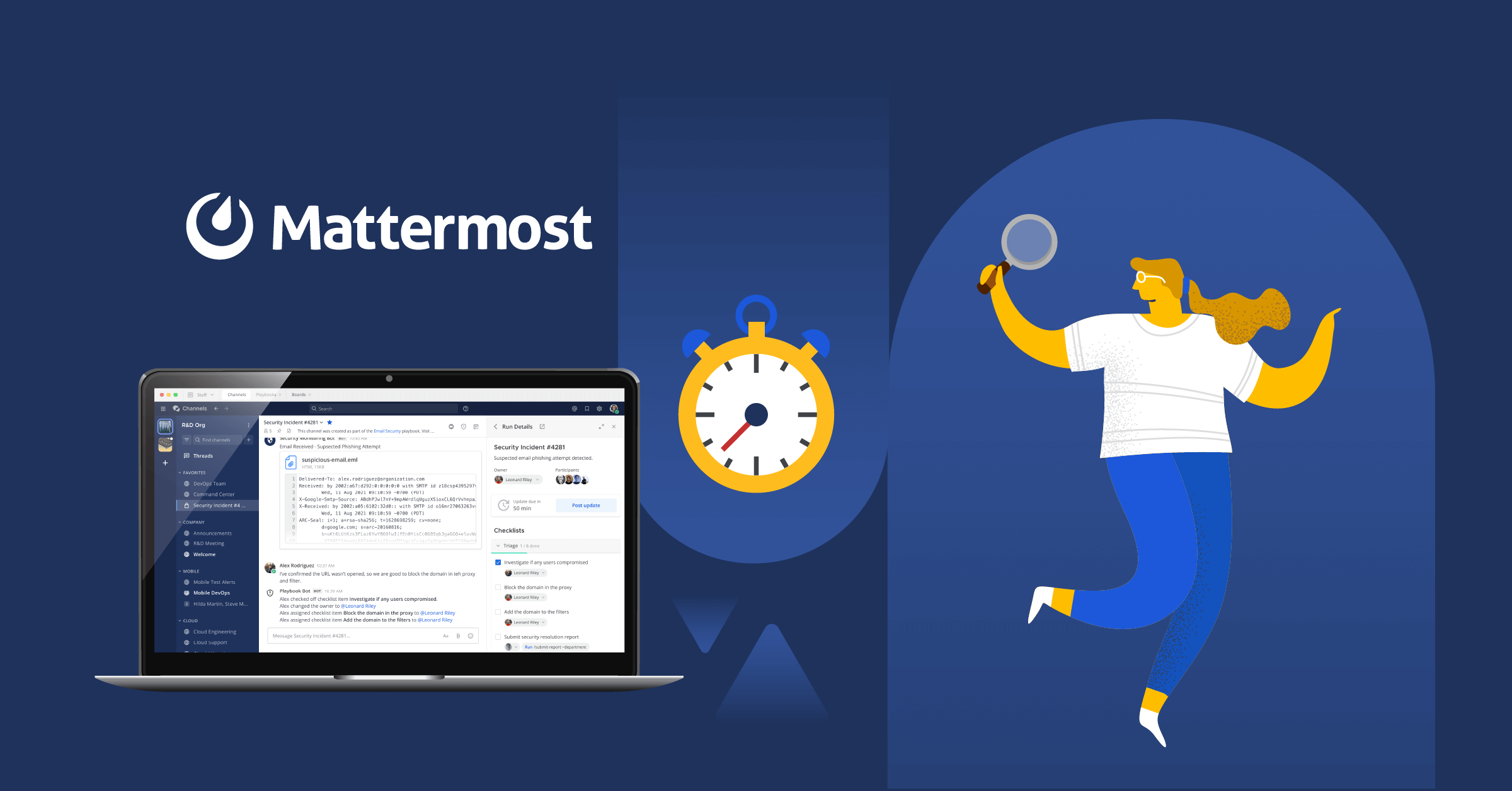
Bring Your Performance Monitoring Tools Together with Mattermost
Splunk Lantern Use Cases for Security and Observ Splunk
APM Tools Top Real World Use Cases AppOptics Blog
Use cases BIG IP APM operations guide
Application Performance Monitoring APM Datadog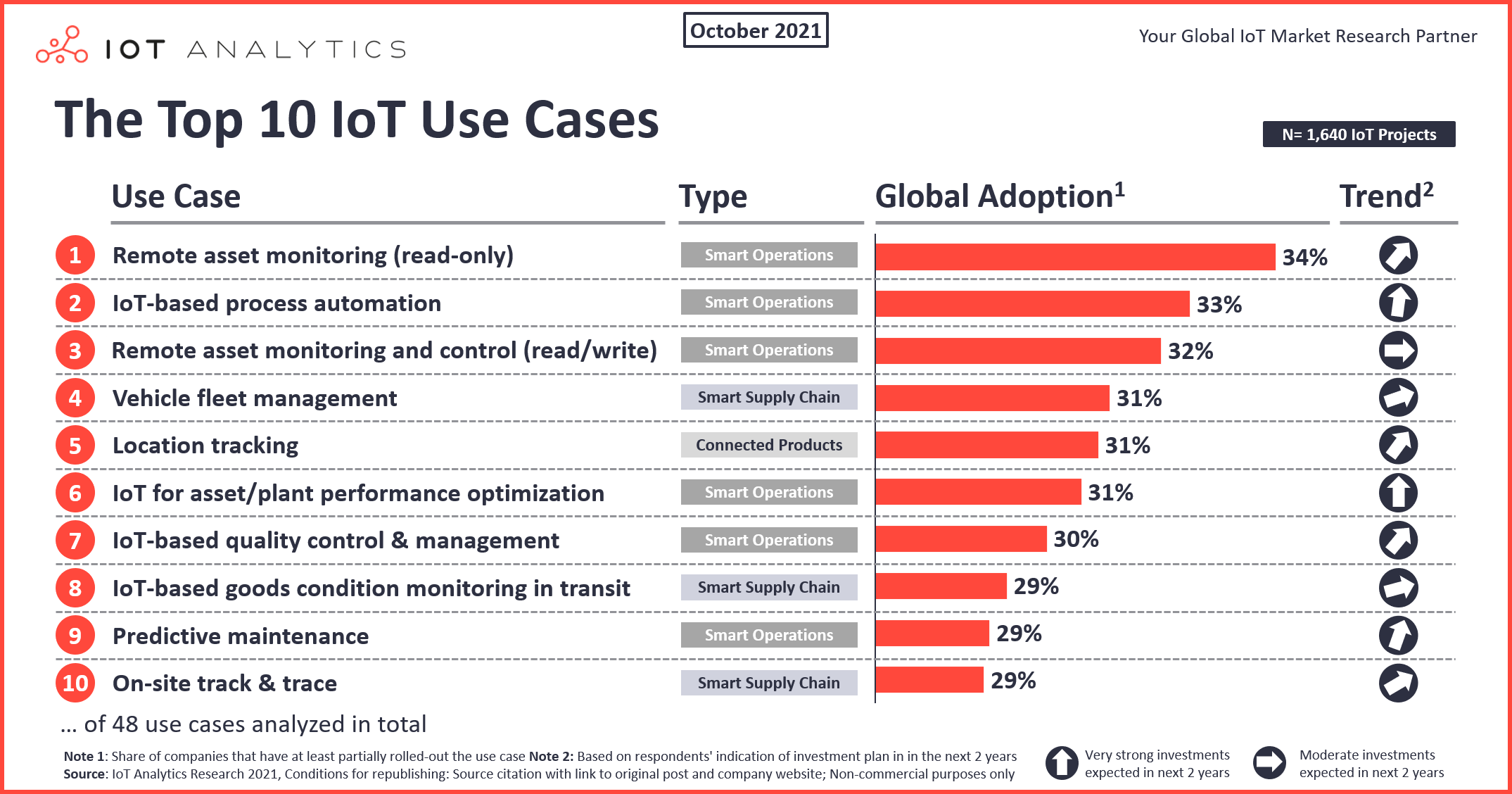
The top 10 IoT Use Cases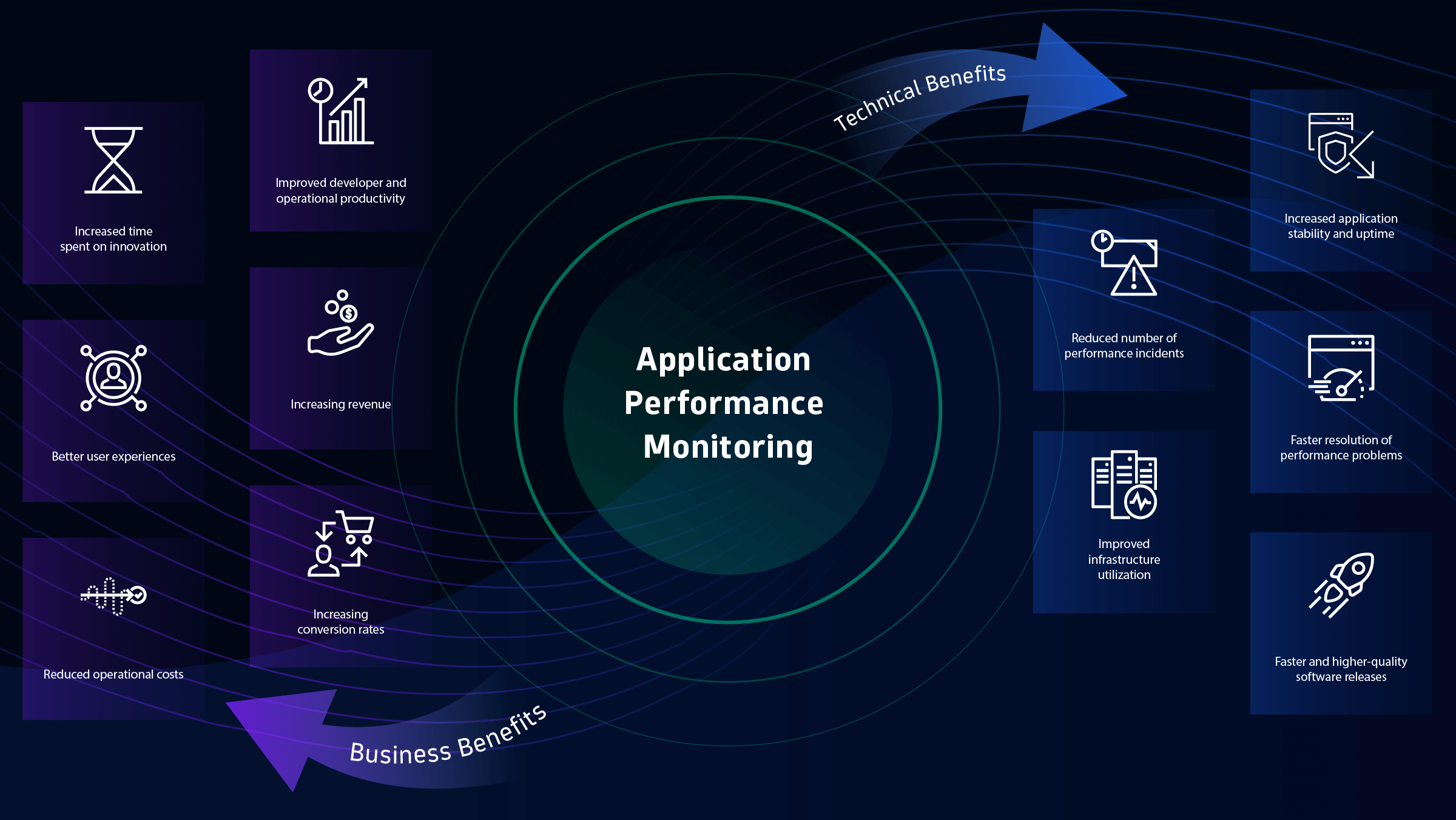
What is APM Application performance monitoring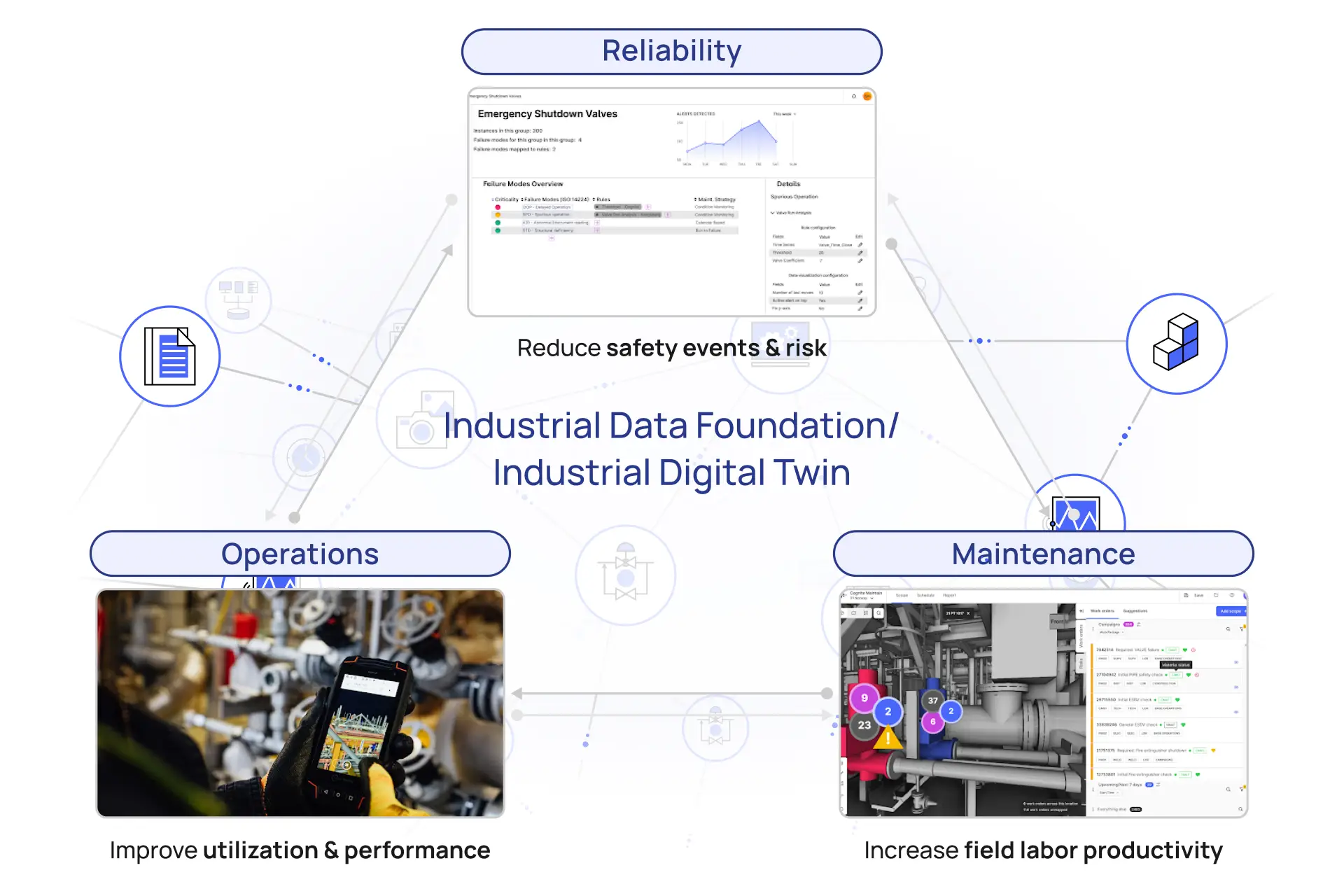
Cognite Data Fusion for Asset Performance Management APM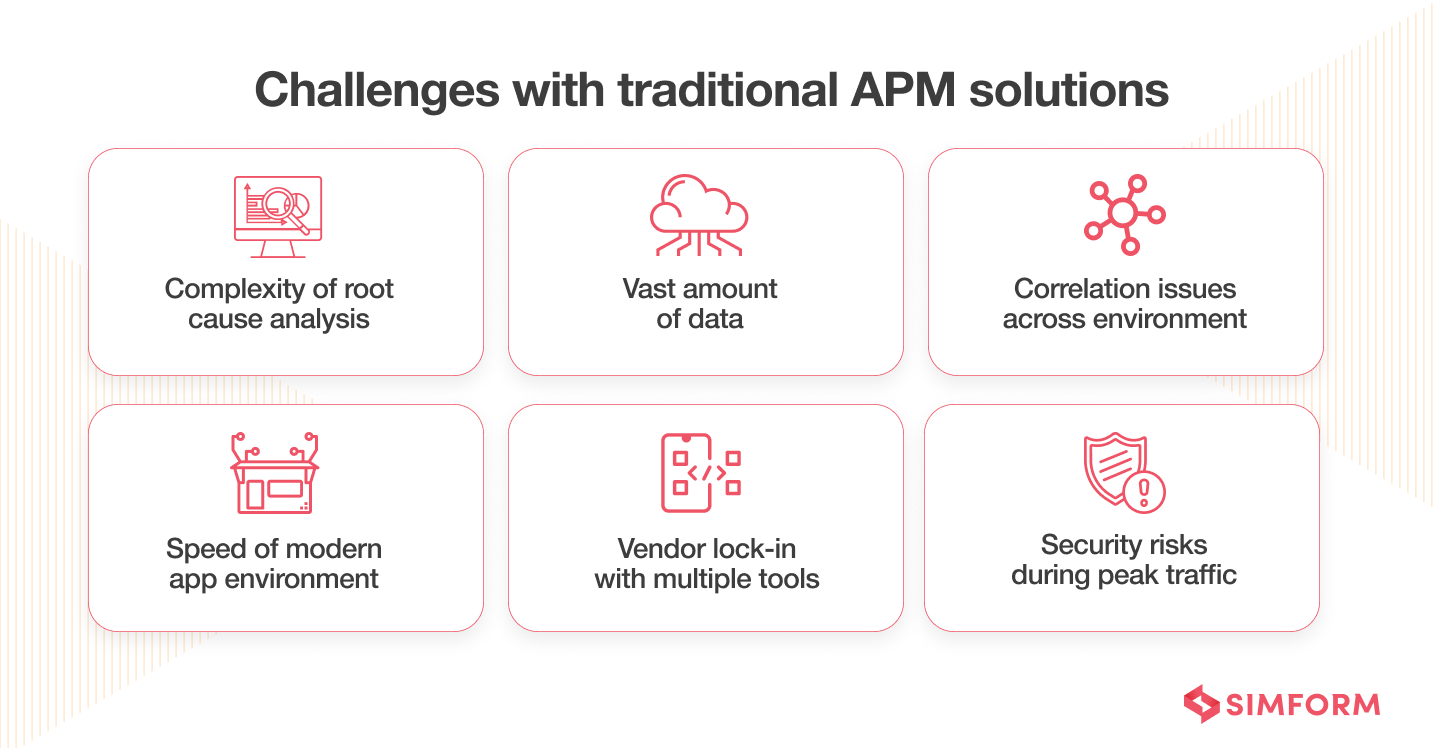
From Traditional APM to Enterprise Observability An Ultimate Guide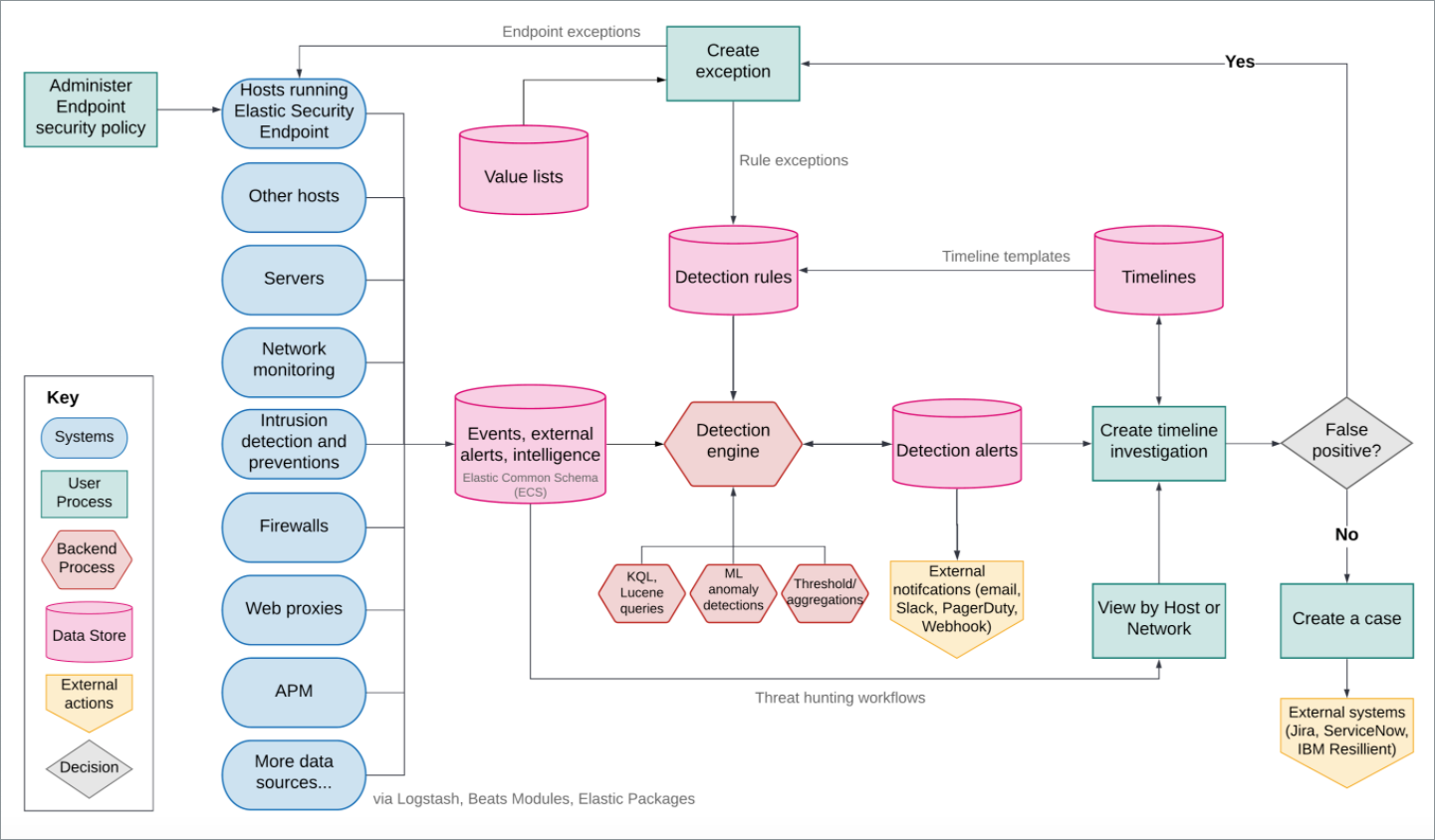
Elastic Security overview Kibana Guide 8.13 Elastic
Eight Essential Use Cases for Application Performance Monitoring
Use cases BIG IP APM operations guide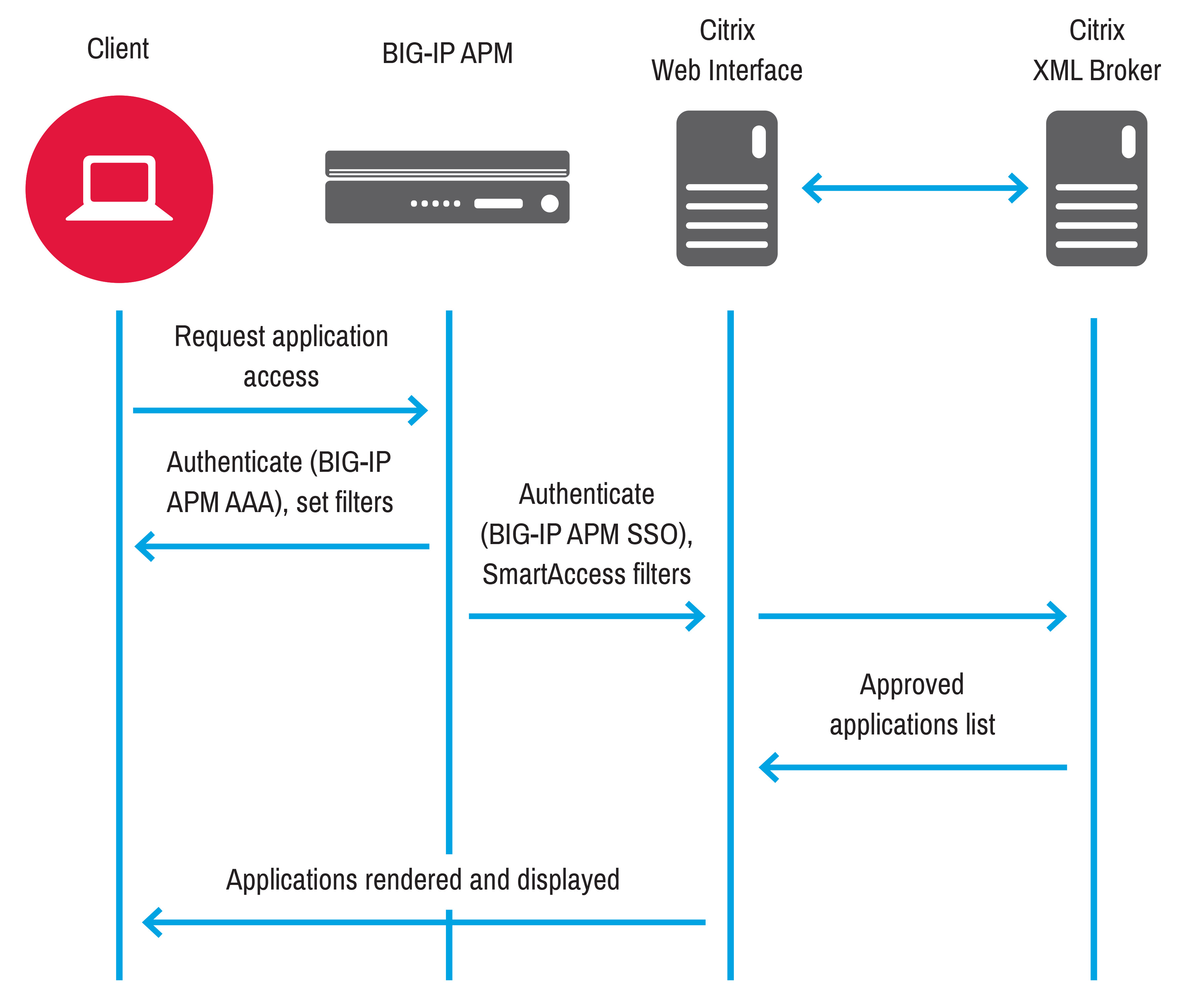
Use cases BIG IP APM operations guide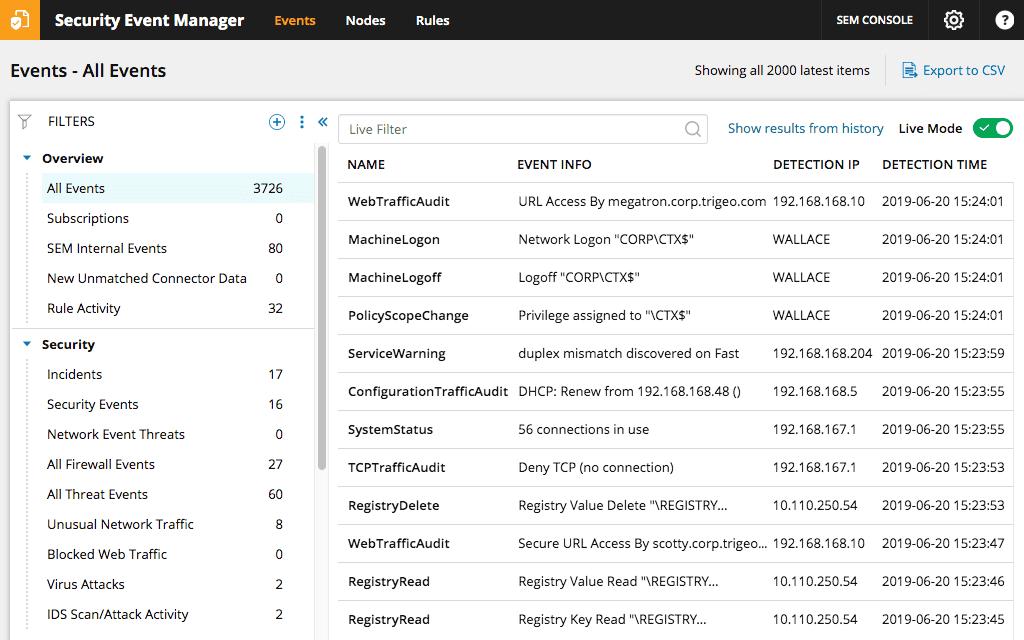
Security Information Management System SolarWinds
What is APM Overview Common Terms and Features Stackify
Application Performance Monitoring Using Zipkin PHP to Monitor an
Use cases BIG IP APM operations guide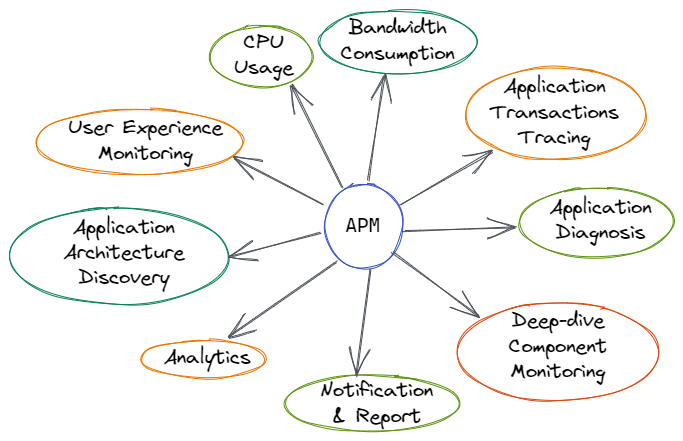
Why Application Performance Monitoring APM Tool Is Important
10 Reasons SIEM Should Remain Dedicated to Security Part 3 by

