Solved 1. The layer is concerned with efficient and Chegg
Which protocol is by far the most hot sale common
Share. Visit »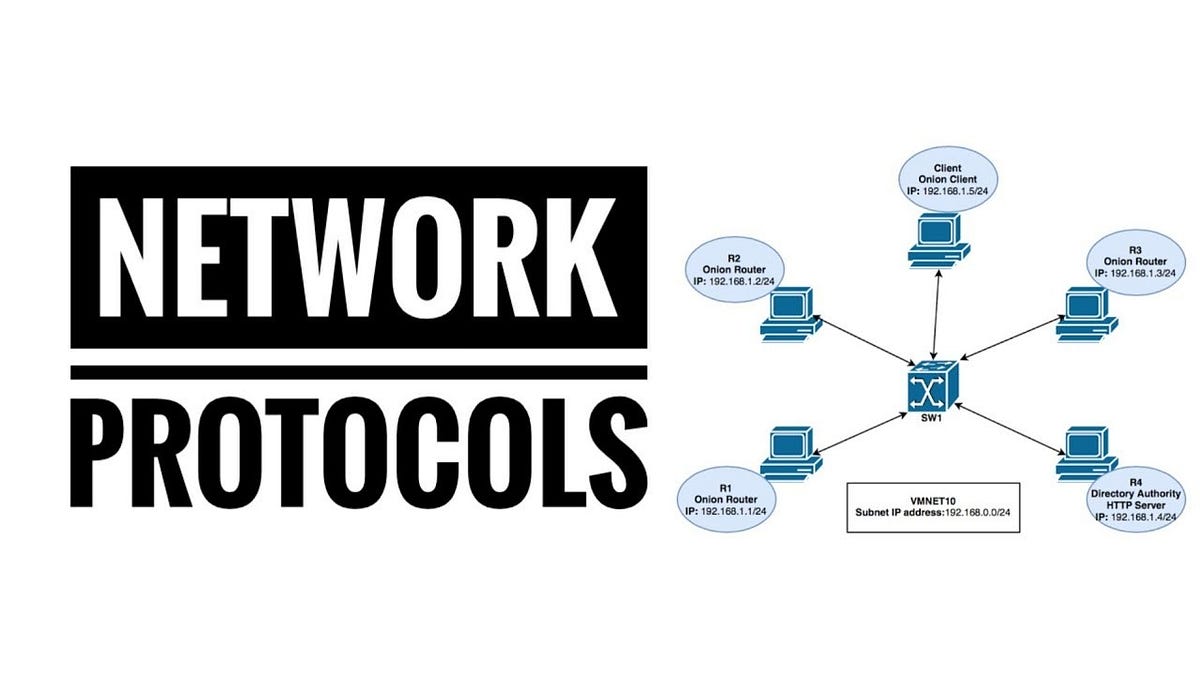
Most Common Networking Protocol s by Keshav Thakur Medium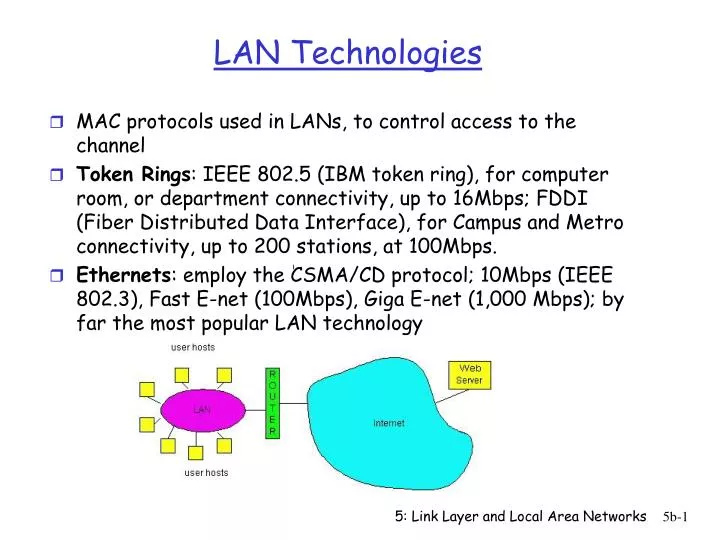
PPT LAN Technologies PowerPoint Presentation free download ID
8 Must Know Internet Protocols for Every Developer by Ian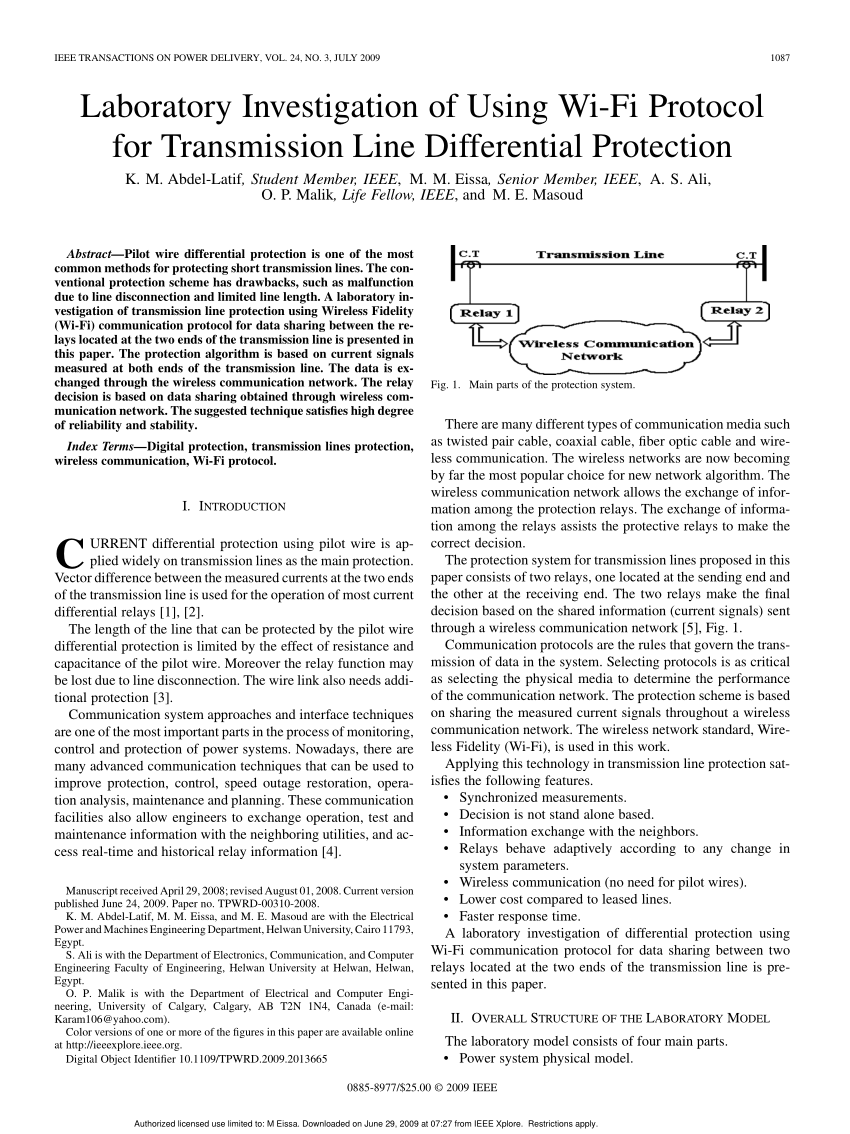
PDF Laboratory Investigation of Using Wi Fi Protocol for
Top 10 exploit vectors for blockchain protocols by Ironblocks
PPT Network Layer Review PowerPoint Presentation free download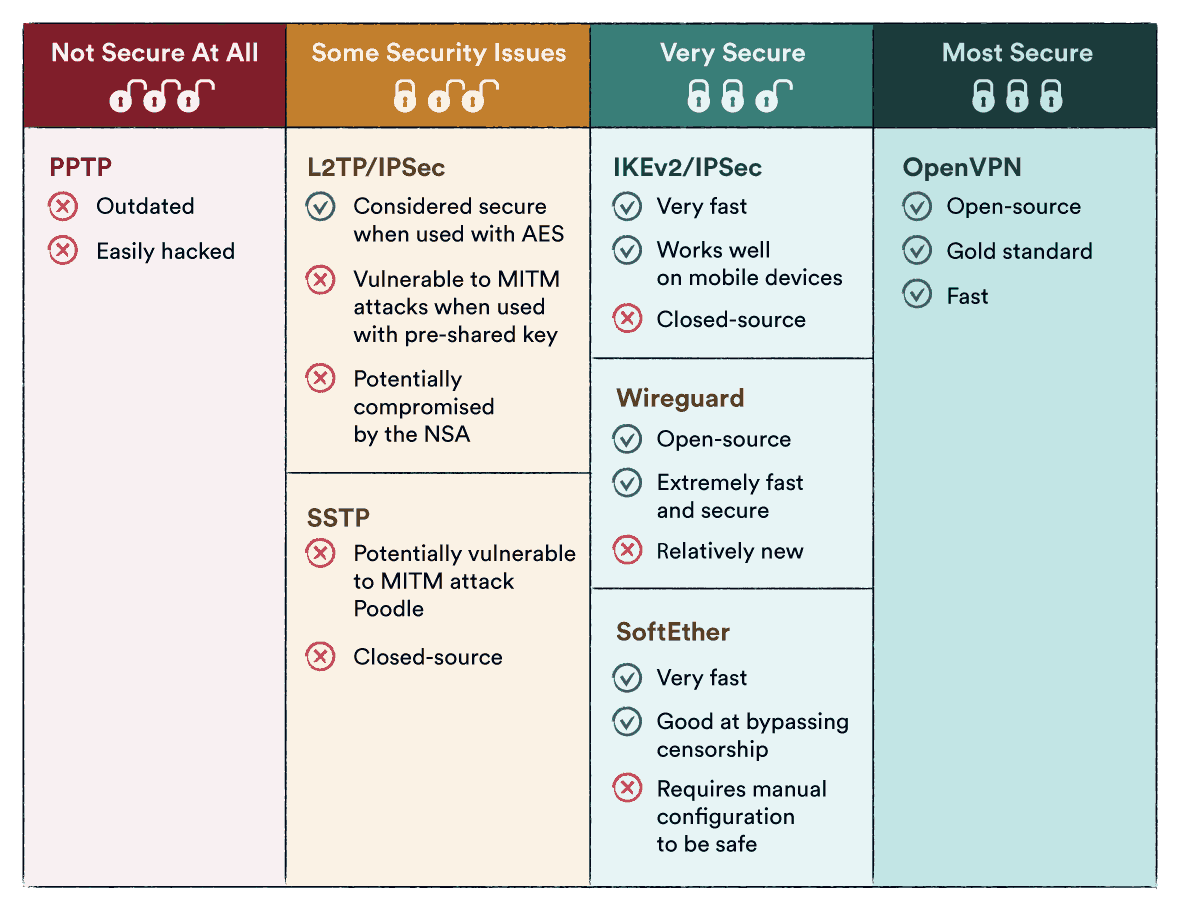
VPN Protocols Explained Compared Which Protocol Is Best
RS232 Serial Port 7 Facts You Need to Know before Using
The most common protocols used in the Internet of Things per layer
Google Ranking Factors for 2024 The 10 Most Important
Http VS. Https PPT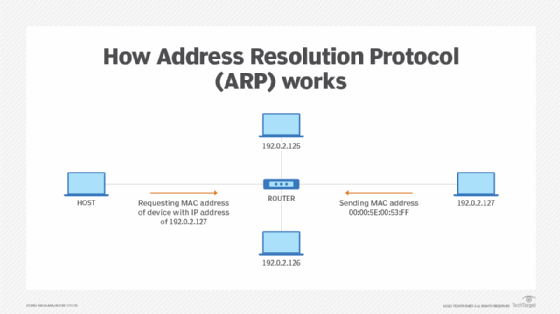
12 common network protocols and their functions explained TechTarget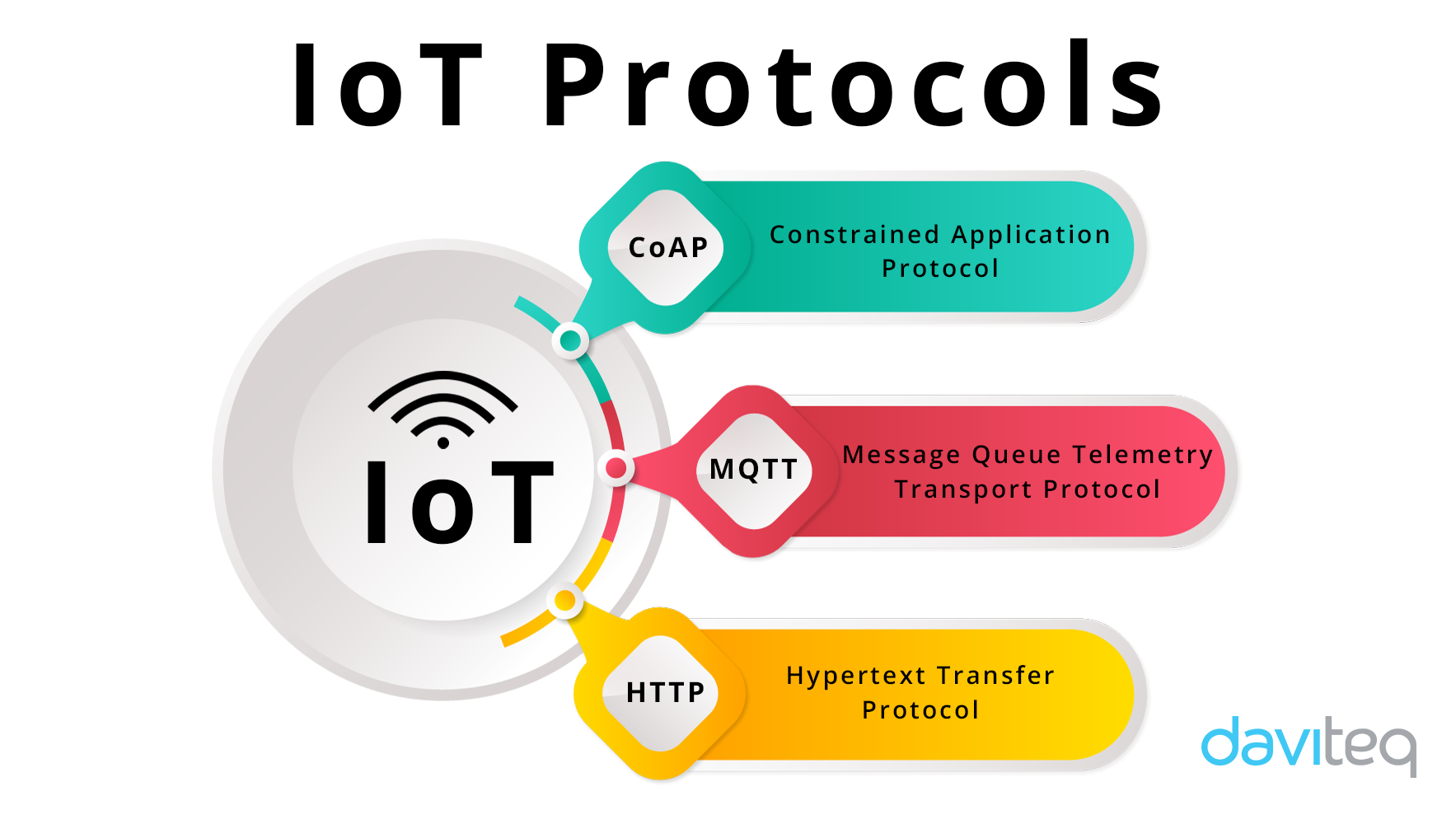
What are the most popular IoT protocols Characteristics and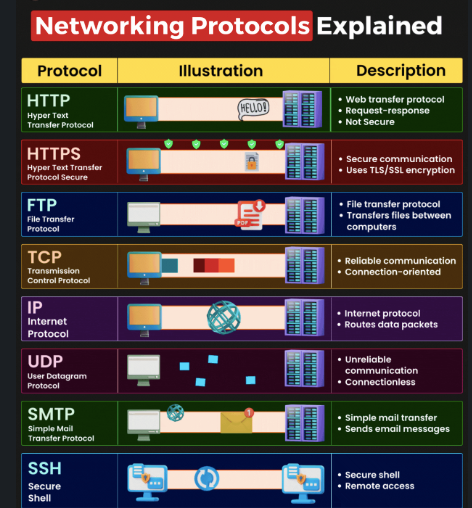
Network Protocols. Here is a list of some of the most by Apurva
Network Ch. 8 TCP IP Applications Flashcards Quizlet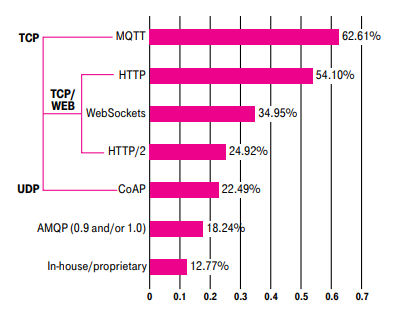
What are the most popular IoT protocols Characteristics and
Top 10 exploit vectors for blockchain protocols by Ironblocks
What is Modbus RealPars
Overview of the CAN Bus Protocol Embedded Electronic Component
HTTP Wikipedia
An Introduction to I2C and SPI Electronic Products
Solved 1. The layer is concerned with efficient and Chegg
Top 8 Most Popular Network Protocols Explained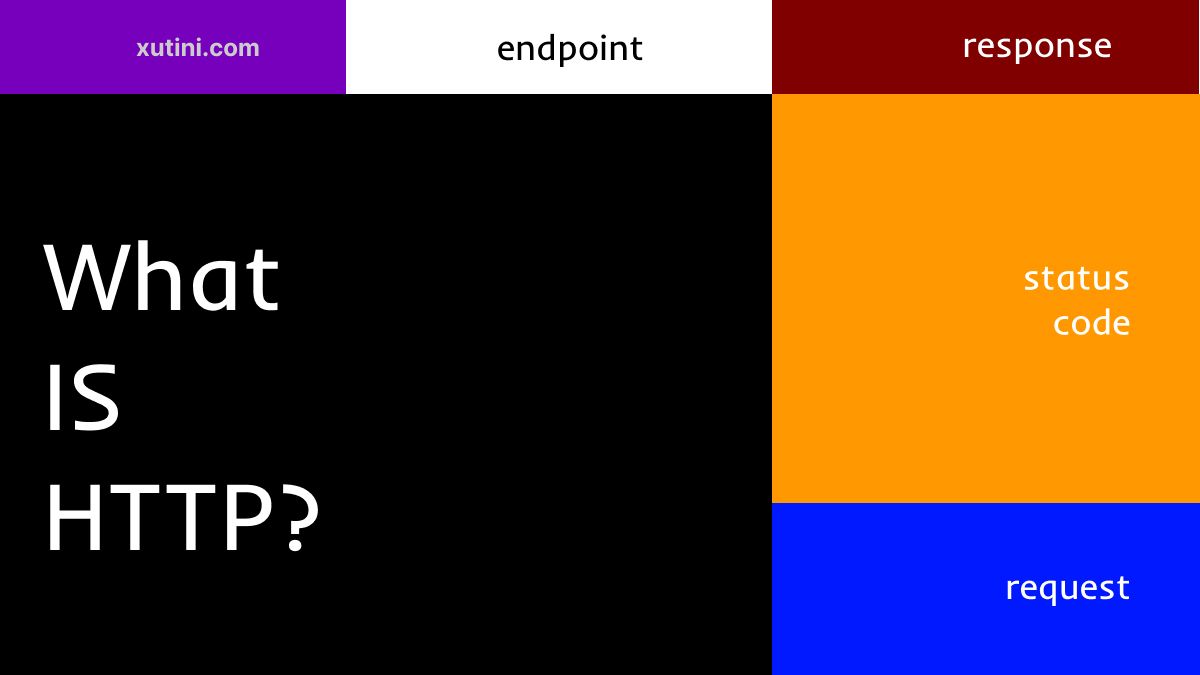
What is HTTP Protocol Overview for Beginners
Tradewater on LinkedIn worldozoneday montrealprotocol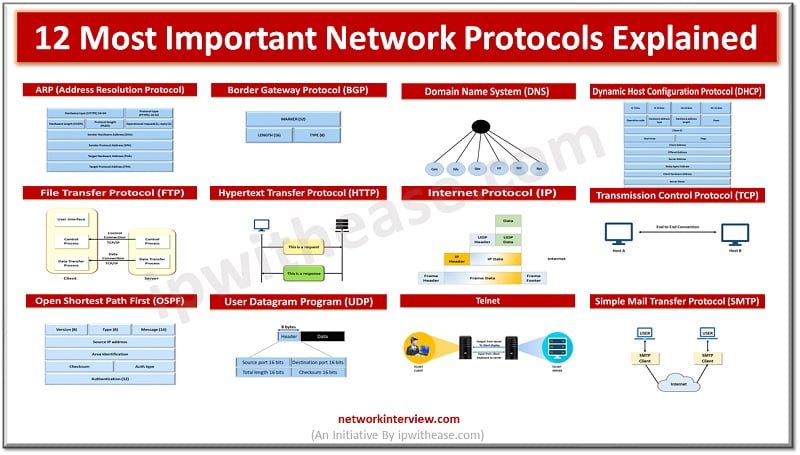
12 Most Important Network Protocols Explained Network Interview
Infographic How To Choose The Best VoIP Provider One Contact
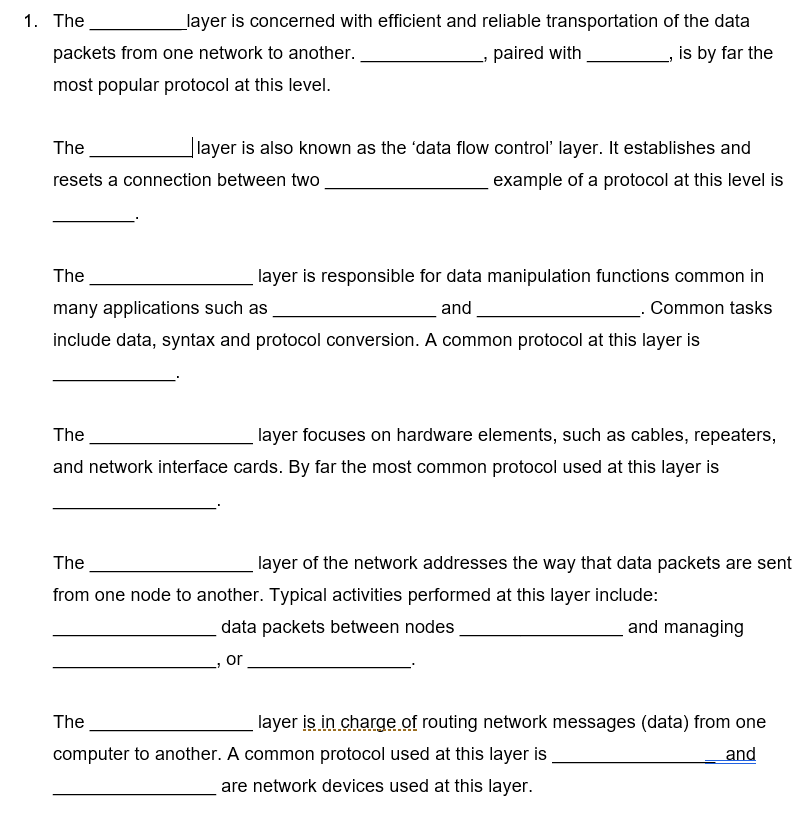
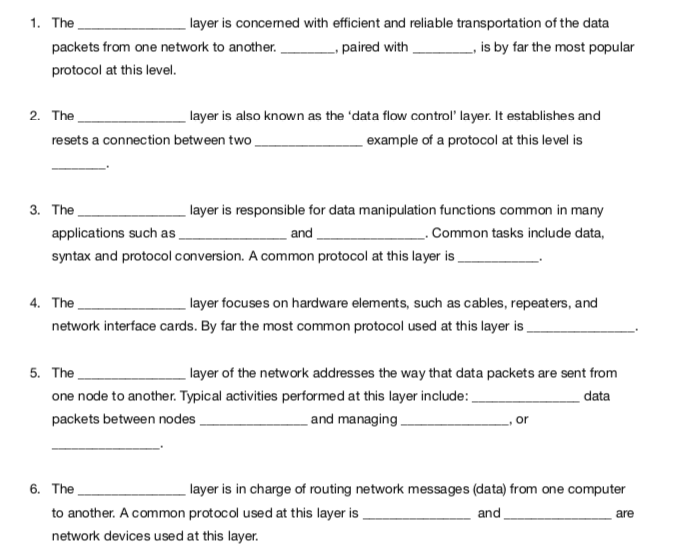
Solved 1. The layer is concerned with efficient and reliable
What is a Protocol protocol is a set of rules that governs the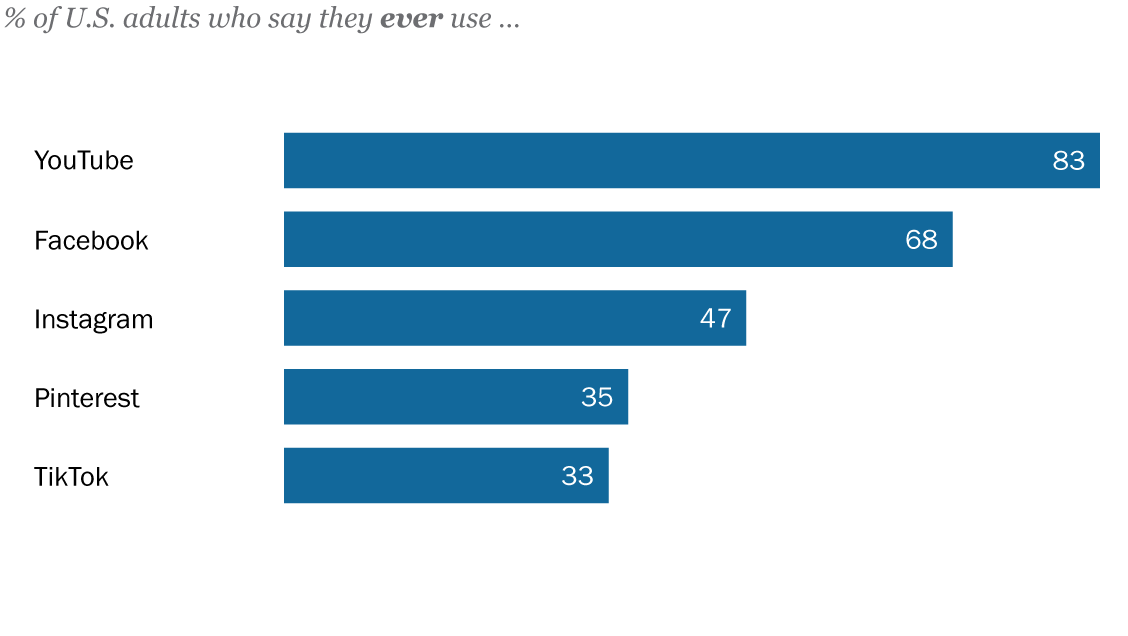
How Americans Use Social Media Pew Research Center
Cloud security best practices part 1 by Cohesive Networks Medium
SOLVED 19 4 points Regular Switches are considered Data Link
Overview of the CAN Bus Protocol Embedded Electronic Component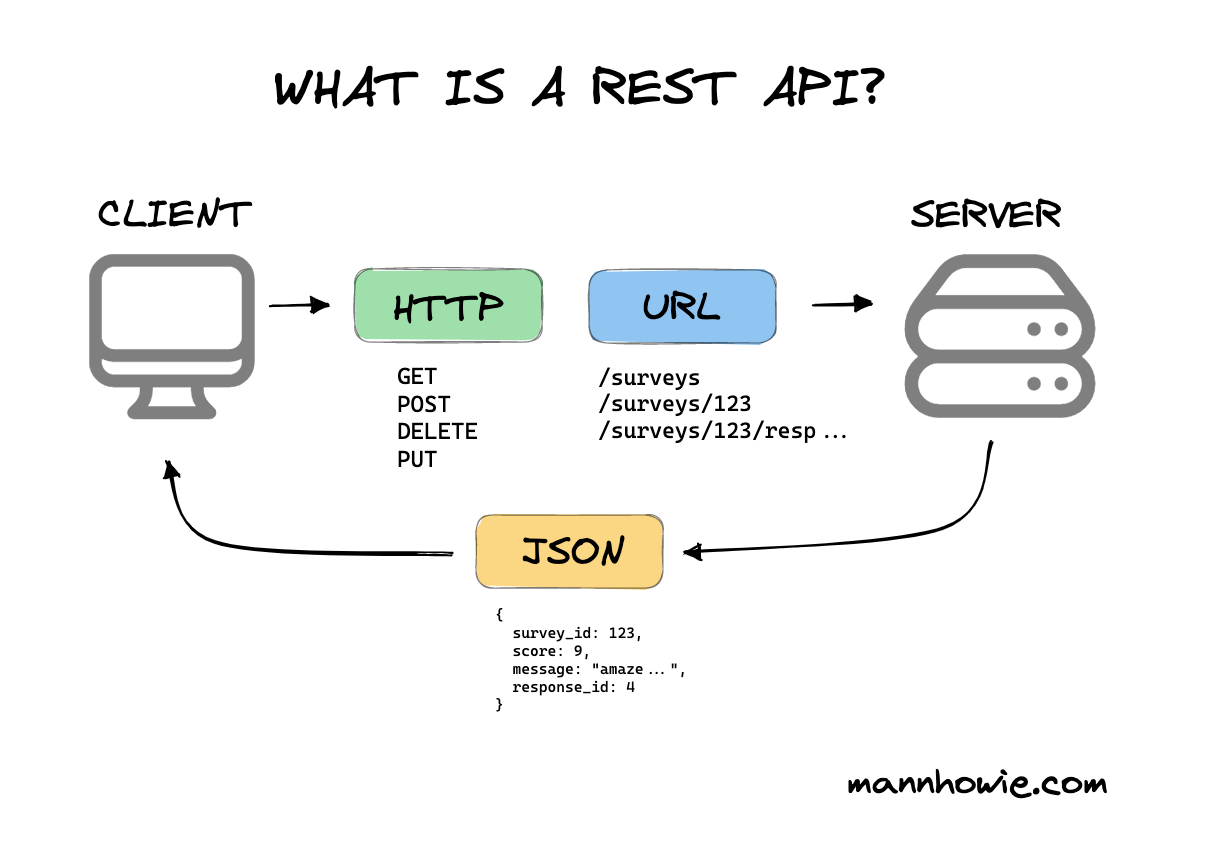
MASTERING API DESIGN A COMPREHENSIVE GUIDE TO ARCHITECTURAL
12 common network protocols and their functions explained TechTarget
Majority of Ransomware Attacks Start via Email
Everything is always situational Blindly following a past down PED
Why is HTTP not secure HTTP vs. HTTPS Cloudflare
Jamiel Sheikh on LinkedIn Ethereum Layer 2 is where the growth is